An Iranian-linked threat actor known as Rocket Kitten[1]
has been observed actively exploiting a recently patched VMware
vulnerability to gain initial access and deploy the Core Impact
penetration testing tool on vulnerable systems.
Tracked as CVE-2022-22954[2]
(CVSS score: 9.8), the critical issue concerns a case of remote
code execution (RCE) vulnerability affecting VMware Workspace ONE
Access and Identity Manager.
While the issue was patched by the virtualization services
provider on April 6, 2022, the company cautioned users[3]
of confirmed exploitation of the flaw occurring in the wild a week
later.
“A malicious actor exploiting this RCE vulnerability potentially
gains an unlimited attack surface,” researchers from Morphisec Labs
said[4]
in a new report. “This means highest privileged access into any
components of the virtualized host and guest environment.”
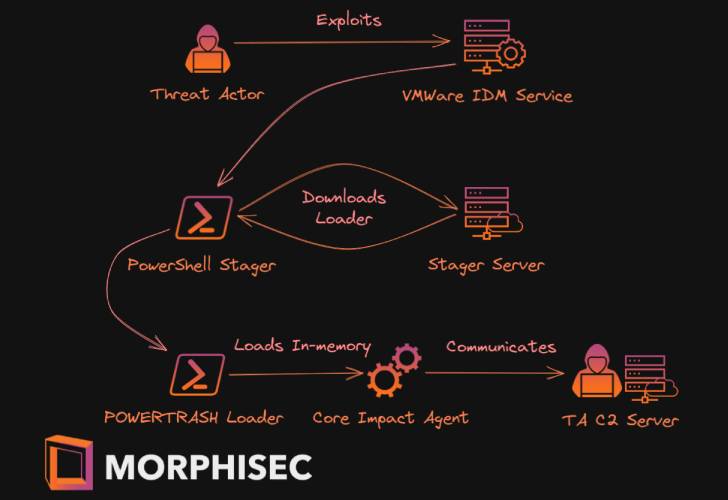
Attack chains exploiting the flaw involve the distribution of a
PowerShell-based stager, which is then used to download a
next-stage payload called PowerTrash Loader that, in turn, injects
the penetration testing tool, Core Impact, into memory for
follow-on activities.
“The widespread use of VMWare identity access management
combined with the unfettered remote access this attack provides is
a recipe for devastating breaches across industries,” the
researchers said.
“VMWare customers should also review their VMware architecture
to ensure the affected components are not accidentally published on
the internet, which dramatically increases the exploitation
risks.”
References
- ^
Rocket
Kitten (malpedia.caad.fkie.fraunhofer.de) - ^
CVE-2022-22954
(thehackernews.com) - ^
cautioned users
(thehackernews.com) - ^
said
(blog.morphisec.com)
Read more https://thehackernews.com/2022/04/iranian-hackers-exploiting-vmware-rce.html