Researchers have detailed a previously undocumented .NET-based
post-exploitation framework called IceApple that has been deployed
on Microsoft Exchange server instances to facilitate reconnaissance
and data exfiltration.
“Suspected to be the work of a state-nexus adversary, IceApple
remains under active development, with 18 modules observed in use
across a number of enterprise environments, as of May 2022,”
CrowdStrike said[1]
in a Wednesday report.
The cybersecurity firm, which discovered the sophisticated
malware in late 2021, noted its presence in multiple victim
networks and in geographically distinct locations. Targeted victims
span a wide range of sectors, including technology, academic, and
government entities.
A post-exploitation toolset, as the name implies, is not used to
provide initial access, but is rather employed to carry out
follow-on attacks after having already compromised the hosts in
question.
IceApple is notable for the fact that it’s an in-memory
framework, indicating an attempt on the part of the threat actor to
maintain a low forensic footprint and evade detection, which, in
turn, bears all hallmarks of a long-term intelligence-gathering
mission.
While intrusions observed so far have involved the malware being
loaded on Microsoft Exchange Servers, IceApple is capable of
running under any Internet Information Services (IIS[2]) web application, making
it a potent threat[3].
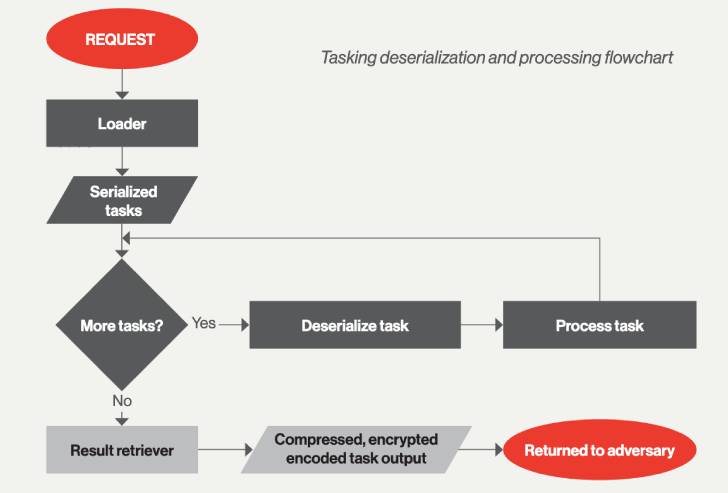
The different modules that come with the framework equip the
malware to list and delete files and directories, write data, steal
credentials, query Active Directory, and export sensitive data.
Build timestamps on these components date back to May 2021.
“At its core, IceApple is a post-exploitation framework focused
on increasing an adversary’s visibility of a target through
acquisition of credentials and exfiltration of data,” the
researchers concluded.
“IceApple has been developed by an adversary with detailed
knowledge of the inner workings of IIS. Ensuring all web
applications are regularly and fully patched is critical to
preventing IceApple from ending up in your environment.”
References
Read more https://thehackernews.com/2022/05/hackers-deploy-iceapple-exploitation.html