The 2022 SaaS Security Survey Report,[1] in collaboration with
CSA, examines the state of SaaS security as seen in the eyes of
CISOs and security professionals in today’s enterprises. The report
gathers anonymous responses from 340 CSA members to examine not
only the growing risks in SaaS security but also how different
organizations are currently working to secure themselves.
Demographics
The majority (71%) of respondents were located in the Americas,
another 17% from Asia, and 13% from EMEA. Of these participants 49%
influence the decision-making process while 39% run the process
itself. The survey examined organizations from a variety of
industries, such as telecommunications (25%), finance (22%), and
government (9%).
While there are many takeaways from the survey, these are our
top seven.
1: SaaS Misconfigurations are Leading to Security
Incidents
Since 2019, SaaS misconfigurations have become a top concern for
organizations, with at least 43% of organizations reporting they’ve
dealt with one or more security incidents caused by a SaaS
misconfiguration. However, since many other organizations state
they are unaware if they had experienced a security incident, the
number of SaaS misconfigured-related incidents could be as
high as 63%. These numbers are striking when compared to
the 17% of security incidents caused by IaaS misconfiguration.
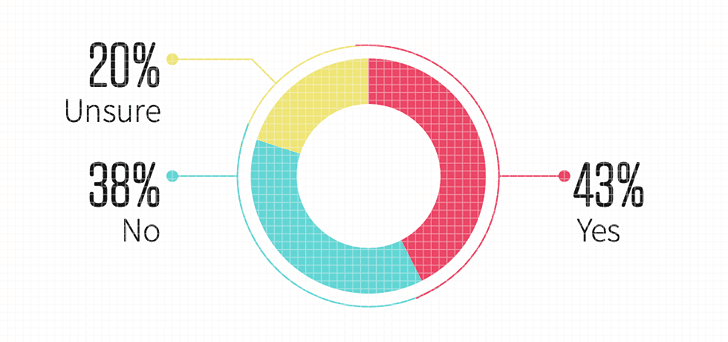 |
| Figure 1. Companies experienced a security incident due to a SaaS misconfiguration |
Learn how to prevent misconfigurations in
your SaaS stack[2]
2: Lack of Visibility and too Many Departments with Access
Reported as Leading Cause for SaaS Misconfigurations
So what exactly is the cause of these SaaS misconfigurations?
While there are several factors to consider, the survey respondents
narrow it down to the two leading causes – having too many
departments with access to SaaS security settings (35%), and a lack
of visibility into the changes in the SaaS security settings (34%).
These are two related issues, neither of which are surprising given
that lack of visibility was rated a top concern when adopting SaaS
applications, and that on average organizations have multiple
departments with access to security settings. One of the leading
reasons for the lack of visibility is the fact that too many
departments have access to security settings, and many of these
departments don’t have proper training and focus on security.
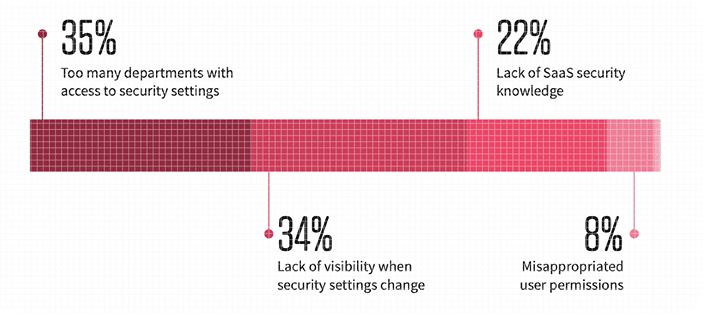 |
| Figure 2. The main causes of SaaS misconfigurations |
3: Investment in Business-Critical SaaS Applications are
Outpacing SaaS Security Tools and Staff
It’s well-known that businesses are adopting more apps – this
past year alone, 81% of respondents say that they have increased
their investments in business-critical SaaS applications. On the
other hand, investment in security tools (73%) and staff (55%) for
SaaS security is lower. This dissonance represents an increasing
burden on the existing security teams to monitor SaaS security.
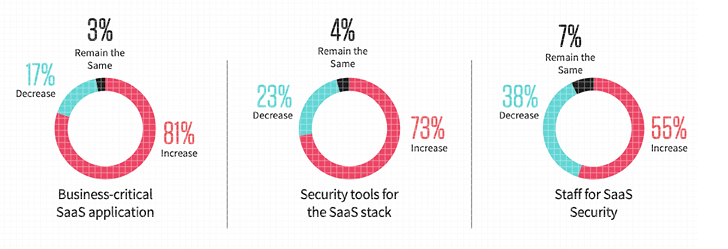 |
| Figure 3. Companies’ investment in SaaS apps, security tools, and staff |
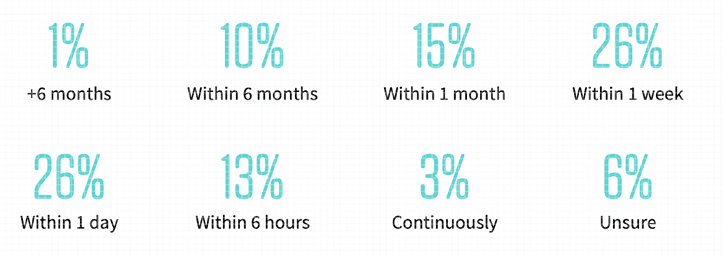
4: Manual detection and remediation of SaaS misconfigurations
keeps organizations exposed
46% of organizations that manually monitor their SaaS security
are conducting checks only once a month or less, while 5% don’t
conduct checks at all. After discovering a misconfiguration, it
takes additional time for security teams to resolve it.
Approximately 1 in 4 organizations take one week or longer to
resolve a misconfiguration when remediating manually. This lengthy
timing leaves organizations vulnerable.
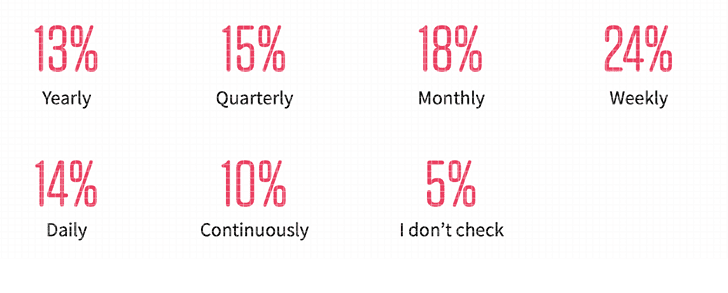 |
| Figure 4. How often companies to manually check their SaaS misconfigurations |
 |
| Figure 5. How long it takes companies to manually fix SaaS misconfiguration |
5: Use of an SSPM reduces timeline to detect and remediate SaaS
misconfigurations
The flip side of the coin for finding #4 is that the
organizations that have implemented an SSPM can more quickly and
accurately detect and remediate their SaaS misconfigurations. The
majority of these organizations (78%) utilize an SSPM to check
their SaaS security configurations once a week or more. When it
comes to resolving the misconfiguration, 81% of organizations using
an SSPM are able to resolve it within a day to a week.
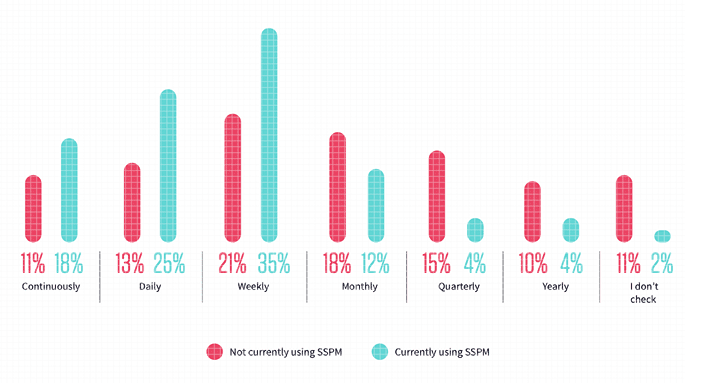 |
| Figure 6. Frequency of SaaS security configuration checks |
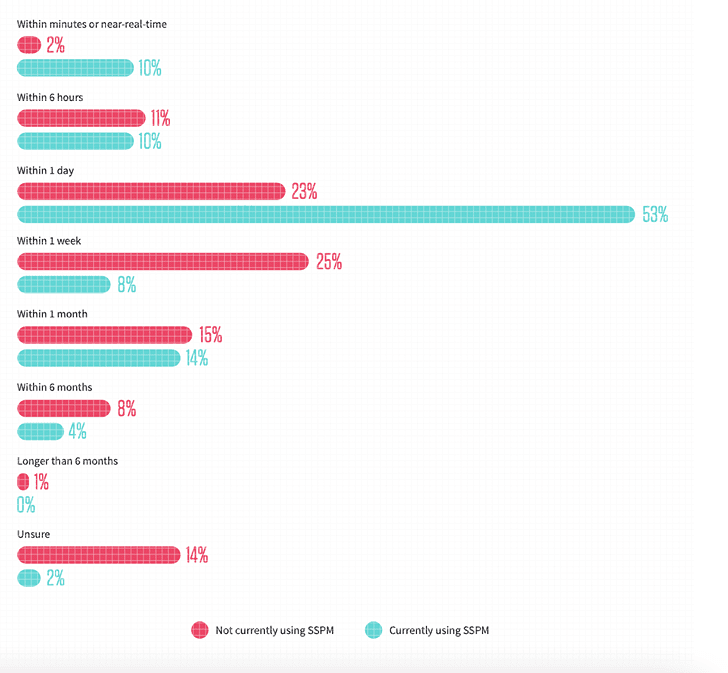 |
| Figure 7. Length of time to fix SaaS misconfigurations |
Click here to schedule a 15-minute demo of
how Adaptive Shield SSPM can help you[3]
6: 3rd party app access is a top concern
Third-party apps, also called no-code or low-code platforms, can
boost productivity, enable hybrid work, and are overall essential
in building and scaling a company’s work processes. However, many
users quickly connect 3rd party apps without considering what
permission these apps are requesting. Once accepted, the
permissions and subsequent access granted to these 3rd party apps
could be harmless or as malicious as an executable file. Without
visibility into the SaaS-to-SaaS supply chain, employees are
connecting to their organization’s business-critical apps, security
teams are blind to many potential threats. As organizations
continue to adopt SaaS applications, one of their top concerns is
the lack of visibility, especially that of third-party application
access to the core SaaS stack (56%).
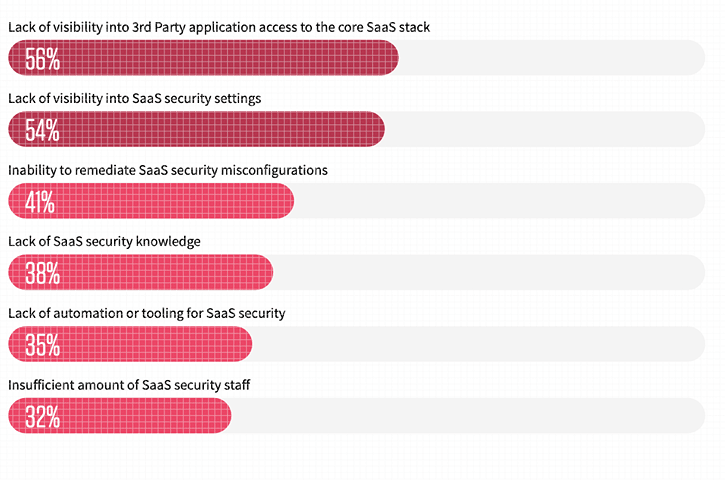 |
| Figure 8. Companies’ top concern when adopting SaaS apps |
Planning Ahead and Implementing SSPM
Despite the category being introduced to the market two years
ago, it is fast maturing. When assessing four cloud security
solutions, SSPM receives an average rating of “somewhat familiar.”
Furthermore, 62% of respondents report that they are already using
an SSPM or plan to implement one in the coming 24 months.
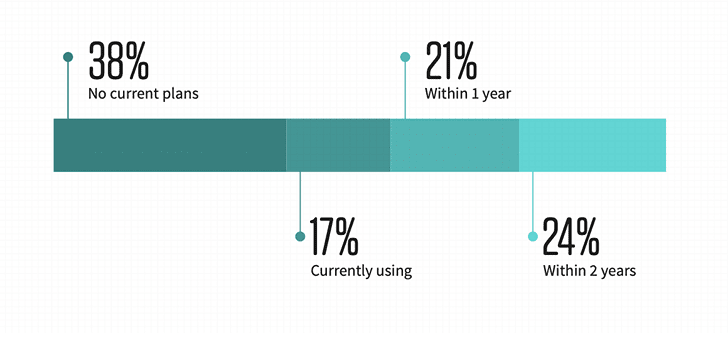 |
| Figure 9. Companies currently using or planning to use SSPM |
Conclusion
The 2022 SaaS Security Survey Report offers insights into how
organizations are using and protecting their SaaS applications. It
is without a doubt that as companies continue to adopt more
business-critical SaaS apps, there is more risk. To face this
challenge head-on companies should begin securing themselves
through two best practices:
- The first being to enable security teams to gain full
visibility into all SaaS app security settings, including 3rd party
app access and user permissions, which in turn allows departments
to maintain their access without risk of making improper changes
that leave the organization vulnerable. - Secondly, companies should utilize automated tools, such as
SSPMs, to continuously monitor and quickly remediate SaaS security
misconfigurations. These automated tools allow security teams to
recognize and fix issues in near-real time, reducing the overall
time the organization is left vulnerable or preventing the problem
from occurring all together.
Both of these changes provide support to their security team
while not preventing departments from continuing their work.
References
- ^
2022
SaaS Security Survey Report,
(www.adaptive-shield.com) - ^
Learn
how to prevent misconfigurations in your SaaS stack
(www.adaptive-shield.com) - ^
Click
here to schedule a 15-minute demo of how Adaptive Shield SSPM can
help you (www.adaptive-shield.com)
Read more https://thehackernews.com/2022/05/7-key-findings-from-2022-saas-security.html
