A new wave of phishing campaigns has been observed spreading a
previously documented malware called SVCReady.
“The malware is notable for the unusual way it is delivered to
target PCs — using shellcode hidden in the properties of Microsoft
Office documents,” Patrick Schläpfer, a threat analyst at HP,
said[1]
in a technical write-up.
SVCReady is said to be in its early stage of development, with
the authors iteratively updating the malware several times last
month. First signs of activity date back to April 22, 2022.
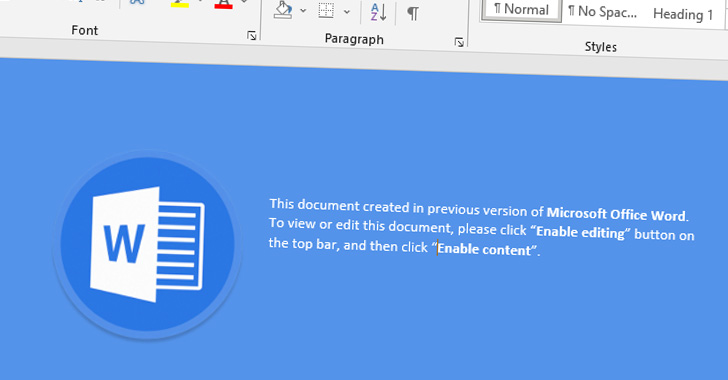
Infection chains involve sending Microsoft Word document
attachments to targets via email that contain VBA macros to
activate the deployment of malicious payloads.
But where this campaign stands apart is that instead of
employing PowerShell or MSHTA to retrieve next-stage executables
from a remote server, the macro runs shellcode stored in the
document properties[2], which subsequently
drops the SVCReady malware.
In addition to achieving persistence on the infected host by
means of a scheduled task, the malware comes with the ability to
gather system information, capture screenshots, run shell commands,
as well as download and execute arbitrary files.
This also included delivering RedLine Stealer[3]
as a follow-up payload in one instance on April 26 after a machine
was initially compromised with SVCReady.
HP said it identified overlaps between the file names of the
lure documents and the images contained in the files used to
distribute SVCReady and those employed by another group called
TA551[4]
(aka Hive0106 or Shathak[5]), but it’s not
immediately clear if the same threat actor is behind the latest
campaign.
“It is possible that we are seeing the artifacts left by two
different attackers who are using the same tools,” Schläpfer noted.
“However, our findings show that similar templates and potentially
document builders are being used by the actors behind the TA551 and
SVCReady campaigns.”
References
- ^
said
(threatresearch.ext.hp.com) - ^
document
properties (support.microsoft.com) - ^
RedLine
Stealer (thehackernews.com) - ^
TA551
(thehackernews.com) - ^
Shathak
(thehackernews.com)
Read more https://thehackernews.com/2022/06/researchers-warn-of-spam-campaign.html