As many as eight zero-day vulnerabilities have been disclosed in
Carrier’s LenelS2 HID Mercury access control system that’s used
widely in healthcare, education, transportation, and government
facilities.
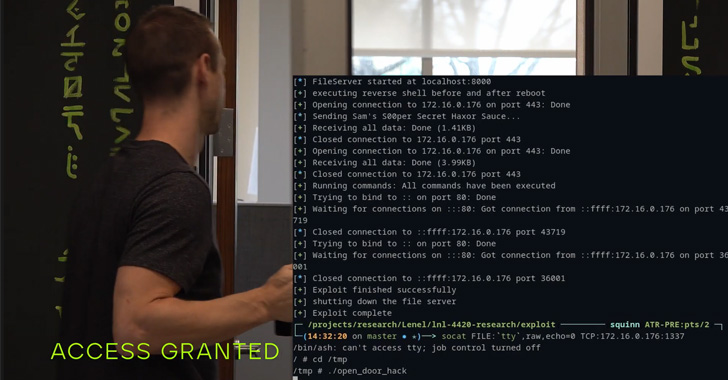
“The vulnerabilities uncovered allowed us to demonstrate the
ability to remotely unlock and lock doors, subvert alarms and
undermine logging and notification systems,” Trellix security
researchers Steve Povolny and Sam Quinn said in a report shared
with The Hacker News.
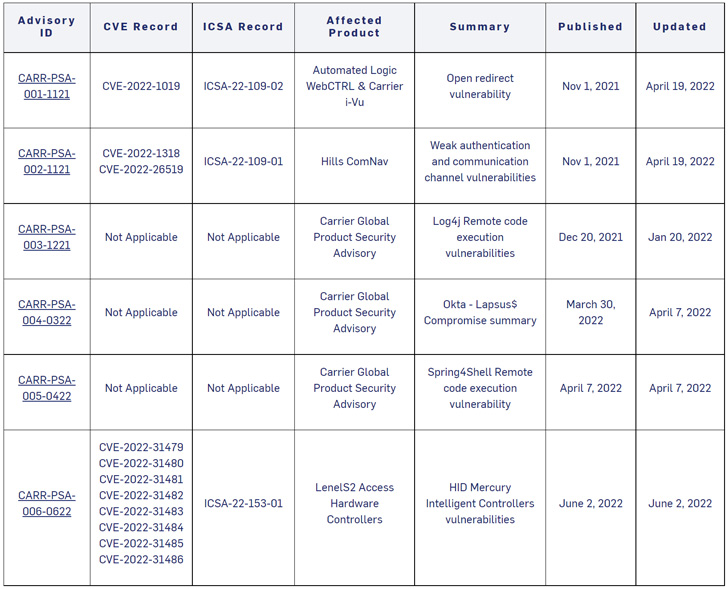
The issues, in a nutshell, could be weaponized by a malicious
actor to gain full system control, including the ability to
manipulate door locks. One of the bugs (CVE-2022-31481) includes an
unauthenticated remote execution flaw that’s rated 10 out of 10 for
severity on the CVSS scoring system.
Other shortcomings could lead to command injection
(CVE-2022-31479, CVE-2022-31486), denial-of-service
(CVE-2022-31480, CVE-2022-31482), user modification
(CVE-2022-31484), and information spoofing (CVE-2022-31485) as well
as achieve arbitrary file write (CVE-2022-31483).
LenelS2 is employed in environments to grant physical access to
privileged facilities and integrate with more complex building
automation deployments. The following HID Mercury access panels
sold by LenelS2 are impacted –
- LNL-X2210
- LNL-X2220
- LNL-X3300
- LNL-X4420
- LNL-4420
- S2-LP-1501
- S2-LP-1502
- S2-LP-2500, and
- S2-LP-4502
Trellix noted that by chaining two of the aforementioned
weaknesses, it was able to gain root-level privileges on the device
remotely and unlock and control the doors, effectively subverting
the system monitoring protections.
Coinciding with the public disclosure is an industrial control
systems (ICS) advisory from the U.S. Cybersecurity and
Infrastructure Security Agency (CISA), urging users to update the
access panels to the latest firmware version[1]
(CARR-PSA-006-0622).
“Successful exploitation of these vulnerabilities could allow an
attacker access to the device, allowing monitoring of all
communications sent to and from the device, modification of onboard
relays, changing of configuration files, device instability, and a
denial-of-service condition,” the agency said[2]
in an alert.
References
- ^
latest
firmware version
(www.corporate.carrier.com) - ^
said
(www.cisa.gov)
Read more https://thehackernews.com/2022/06/researchers-disclose-critical-flaws-in.html