A novel hardware attack dubbed PACMAN has been
demonstrated against Apple’s M1 processor chipsets, potentially
arming a malicious actor with the capability to gain arbitrary code
execution on macOS systems.
It leverages “speculative execution attacks to bypass an
important memory protection mechanism, ARM Pointer Authentication,
a security feature that is used to enforce pointer integrity,” MIT
researchers Joseph Ravichandran, Weon Taek Na, Jay Lang, and
Mengjia Yan said[1]
in a new paper.
What’s more concerning is that “while the hardware mechanisms
used by PACMAN cannot be patched with software features, memory
corruption bugs can be,” the researchers added.
The vulnerability is rooted in pointer authentication codes
(PACs[2]), a line of defense
introduced in arm64e architecture that aims to detect and secure
against unexpected changes to pointers[3]
— objects that store a memory address — in memory.
PACs aim to solve a common problem in software security, such as
memory corruption vulnerabilities, which are often exploited by
overwriting control data in memory (i.e., pointers) to redirect
code execution to an arbitrary location controlled by the
attacker.
While strategies like Address Space Layout Randomization
(ASLR[4]) have been devised to
increase the difficulty of performing buffer overflow attacks, the
goal of PACs is to ascertain the “validity of pointers with minimal
size and performance impact,” effectively preventing an adversary
from creating valid pointers for use in an exploit.
This is achieved by protecting a pointer with a cryptographic
hash — called a Pointer Authentication Code (PAC) — to ensure its
integrity. Apple explains[5]
PACs as follows –
Pointer authentication works by offering a special CPU
instruction to add a cryptographic signature — or PAC — to unused
high-order bits of a pointer before storing the pointer. Another
instruction removes and authenticates the signature after reading
the pointer back from memory. Any change to the stored value
between the write and the read invalidates the signature. The CPU
interprets authentication failure as memory corruption and sets a
high-order bit in the pointer, making the pointer invalid and
causing the app to crash.
But PACMAN “removes the primary barrier to conducting
control-flow hijacking attacks on a platform protected using
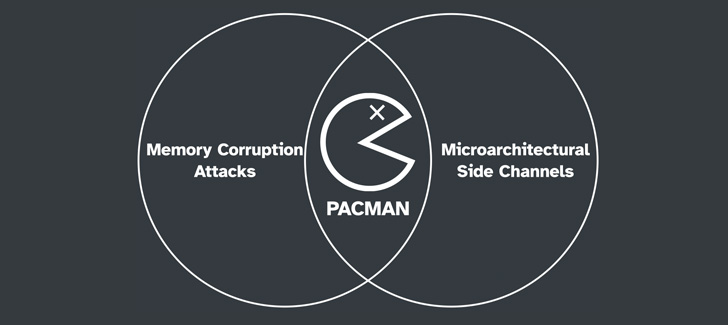
pointer authentication.” It combines memory corruption and speculative execution[6]
to circumvent the security feature, leaking “PAC verification
results via microarchitectural side channels without causing any
crashes.”
The attack method, in a nutshell, makes it possible to
distinguish between a correct PAC and incorrect hash, permitting a
bad actor to “brute-force the correct PAC value while suppressing
crashes and construct a control-flow hijacking attack on a
PA-enabled victim program or operating system.”
The crash prevention, for its part, succeeds because each PAC
value is speculatively guessed[7]
by exploiting a timing-based side channel via the translation
look-aside buffer (TLB[8]) using a Prime+Probe attack[9].
Speculative execution vulnerabilities, as observed in the case
of Spectre and Meltdown, weaponize out-of-order execution[10], a technique that’s
used to bring about a performance improvement in modern
microprocessors by predicting[11] the most likely path of
a program’s execution flow.
However, it’s worth noting that the threat model presumes that
there already exists an exploitable memory corruption vulnerability
in a victim program (kernel), which, in turn, allows the
unprivileged attacker (a malicious app) to inject rogue code into
certain memory locations in the victim process.
“This attack has important implications for designers looking to
implement future processors featuring pointer authentication, and
has broad implications for the security of future control-flow
integrity primitives,” the researchers concluded.
References
- ^
said
(pacmanattack.com) - ^
PACs (lwn.net) - ^
pointers
(en.wikipedia.org) - ^
ASLR
(en.wikipedia.org) - ^
explains
(developer.apple.com) - ^
speculative execution
(thehackernews.com) - ^
speculatively guessed
(thehackernews.com) - ^
TLB
(en.wikipedia.org) - ^
Prime+Probe attack
(thehackernews.com) - ^
out-of-order execution
(en.wikipedia.org) - ^
predicting
(en.wikipedia.org)
Read more https://thehackernews.com/2022/06/mit-researchers-discover-new-flaw-in.html