A Chinese advanced persistent threat (APT) known as Gallium has
been observed using a previously undocumented remote access trojan
in its espionage attacks targeting companies operating in Southeast
Asia, Europe, and Africa.
Called PingPull[1], the
“difficult-to-detect” backdoor is notable for its use of the
Internet Control Message Protocol (ICMP[2]) for command-and-control
(C2) communications, according to new research published by Palo
Alto Networks Unit 42 today.
Gallium is known for its attacks primarily aimed at telecom
companies dating as far back as 2012. Also tracked under the name
Soft Cell[3]
by Cybereason, the state-sponsored actor has been connected[4]
to a broader set of attacks targeting five major telecom companies
located in Southeast Asian countries since 2017.
Over the past year, however, the group is said to have expanded
its victimology footprint to include financial institutions and
government entities located in Afghanistan, Australia, Belgium,
Cambodia, Malaysia, Mozambique, the Philippines, Russia, and
Vietnam.
PingPull, a Visual C++-based malware, provides a threat actor
the ability to access a reverse shell and run arbitrary commands on
a compromised host. This encompasses carrying out file operations,
enumerating storage volumes, and timestomping[5]
files.
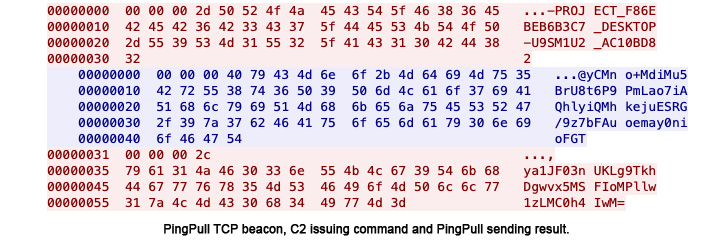
“PingPull samples that use ICMP for C2 communications issue ICMP
Echo Request (ping) packets to the C2 server,” the researchers
detailed. “The C2 server will reply to these Echo requests with an
Echo Reply packet to issue commands to the system.”
Also identified are PingPull variants that rely on HTTPS and TCP
to communicate with its C2 server instead of ICMP and over 170 IP
addresses associated with the group since late 2020.
It’s not immediately clear how the targeted networks are
breached, although the threat actor is known to exploit
internet-exposed applications to gain an initial foothold and
deploy a modified version of the China Chopper[6]
web shell to establish persistence.
“Gallium remains an active threat to telecommunications, finance
and government organizations across Southeast Asia, Europe and
Africa,” the researchers noted.
“While the use of ICMP tunneling is not a new technique,
PingPull uses ICMP to make it more difficult to detect its C2
communications, as few organizations implement inspection of ICMP
traffic on their networks.”
References
Read more https://thehackernews.com/2022/06/chinese-gallium-hackers-using-new.html