BPFDoor isn’t new to the cyberattack[1]
game — in fact, it’s gone undetected for years — but PwC
researchers discovered the piece of malware in 2021. Subsequently,
the cybersecurity community is learning more about the stealthy nature of malware[2], how it works, and how
it can be prevented.
What’s BPFDoor?
BPFDoor[3]
is a piece of malware associated with China-based threat actor Red
Menshen that has hit mostly Linux operating systems. It’s
undetected by firewalls and goes unnoticed by most detection
systems — so unnoticed that it’s been a work in progress over the
last five years, going through various phases of development and
complexity.
How Does It Work?
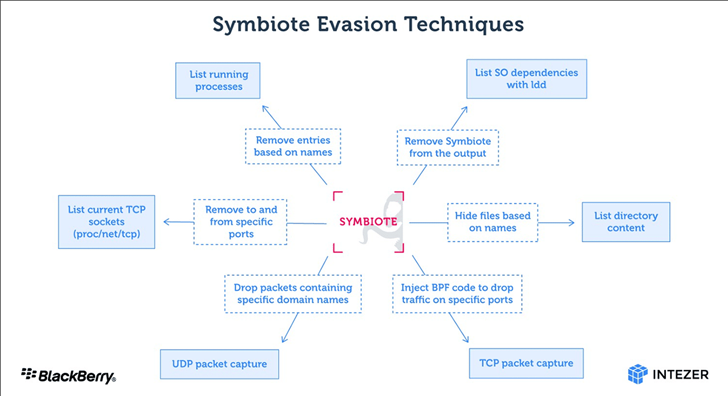
BPF stands for Berkley Packet Filters, which is appropriate
given that the virus exploits packet filters. BPFDoor uses BPF
“sniffers[4]” to see all network
traffic and find vulnerabilities. Packet filters are programs that
analyze “packets” (files, metadata, network traffic) and permit or
decline them to pass based on the source and destination IP
addresses, protocols, or ports. To put it simply, packet filters
work as a firewall of sorts to prevent infected malware from
reaching operating systems.
When BPFDoor is in action, it gets in front of firewalls to
receive packets, then modifies the local firewall or scripts to
allow a threat actor into an operating system. It can function
without opening any ports and can receive commands from any IP
address on the web. And since IP addresses are what the filters
analyze to allow or decline access to packets, BPFDoor could
essentially allow any packet to be sent or received. #nofilter
Why Is It Dangerous?
As stated previously, this malware is extremely dangerous
because of its stealthy and hidden nature. Once BPFDoor is
activated, remote code can be sent through the unfiltered and
unblocked passageway. Malicious traffic blends into legitimate
traffic, making it difficult for firewalls and security solutions
to detect. The BPFDoor also renames itself after infecting a system
as an evasion technique.
Systems have been compromised across the US, South Korea, Hong
Kong, Turkey, India, Vietnam, and Myanmar, and targets have
included telecommunications, government, education, and logistics
organizations.
What Can We Do About It?
In order for BPFDoor to launch, the threat actor would need to
upload the malicious binary to a server. The best lines of defense
are ensuring that virus and malware signatures are up to date to
catch any potential indicators and creating rules within
environments to help detect the seemingly undetectable.
References
- ^
cyberattack
(www.securelink.com) - ^
stealthy
nature of malware (thehackernews.com) - ^
BPFDoor
(elastic.github.io) - ^
sniffers
(www.sandflysecurity.com)
Read more https://thehackernews.com/2022/06/quick-and-simple-bpfdoor-explained.html