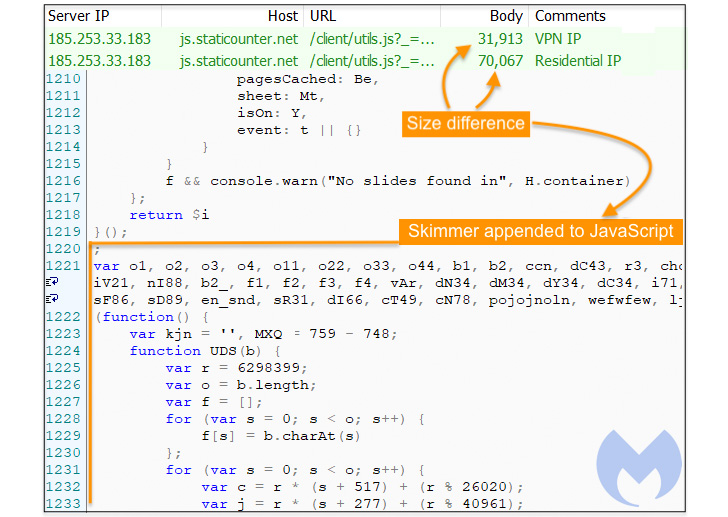
A newly discovered Magecart skimming campaign has its roots in a
previous attack activity going all the way back to November
2021.
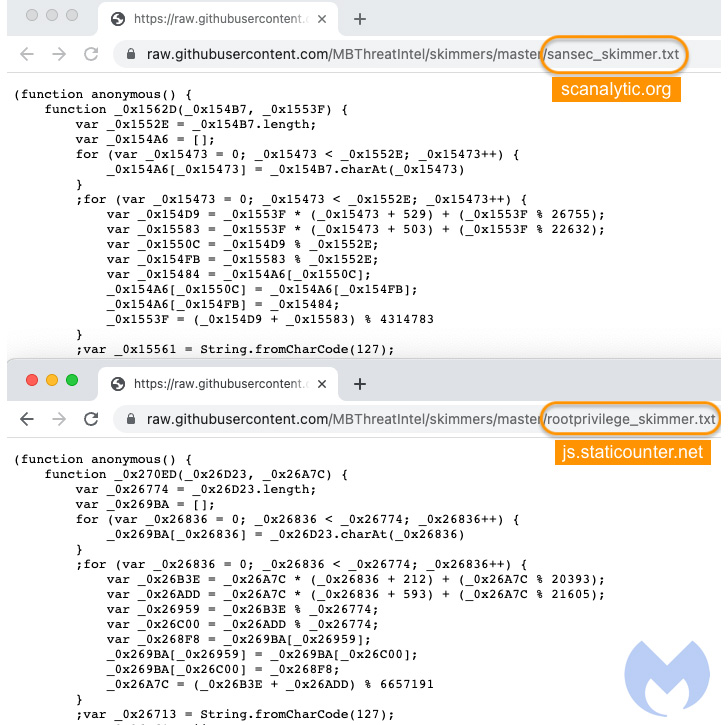
To that end, it has come to light that two[1]
malware[2]
domains identified as hosting credit card skimmer code —
“scanalytic[.]org” and “js.staticounter[.]net” — are part of a
broader infrastructure used to carry out the intrusions,
Malwarebytes said in a Tuesday analysis.
“We were able to connect these two domains with a previous campaign from November
2021[3] which was the first
instance to our knowledge of a skimmer checking for the use of
virtual machines,” Jérôme Segura said[4]. “However, both of them
are now devoid of VM detection code. It’s unclear why the threat
actors removed it, unless perhaps it caused more issues than
benefits.”
The earliest evidence of the campaign’s activity, based on the
additional domains uncovered, suggests it dates back to at least
May 2020.
Magecart[5]
refers to a cybercrime syndicate comprised of dozens of subgroups
that specialize in cyberattacks involving digital credit card theft
by injecting JavaScript code on e-commerce storefronts, typically
on checkout pages.
This works by operatives gaining access to websites either
directly or via third-party services that supply software to the
targeted websites.
While the attacks gained prominence in 2015[6] for singling out the
Magento e-commerce platform (the name Magecart is a portmanteau of
“Magento” and “shopping cart”), they have since expanded to other
alternatives, including a WordPress plugin named WooCommerce[7].
According to a report[8]
published by Sucuri in April 2022, WordPress has emerged as the top
CMS platform for credit card skimming malware, outpacing Magento as
of July 2021, with skimmers[9]
concealed in the websites in the form of fake images[10] and seemingly innocuous
JavaScript theme[11] files[12].
What’s more, WordPress websites accounted for 61% of known
credit card skimming malware detections during the first five
months of 2022, followed by Magento (15.6%), OpenCart (5.5%), and
others (17.7%).
“Attackers follow the money, so it was only a matter of time
before they shifted their focus toward the most popular e-commerce
platform on the web,” Sucuri’s Ben Martin noted at the time.
References
- ^
two
(twitter.com) - ^
malware
(twitter.com) - ^
previous
campaign from November 2021
(blog.malwarebytes.com) - ^
said
(blog.malwarebytes.com) - ^
Magecart
(thehackernews.com) - ^
gained
prominence in 2015 (www.riskiq.com) - ^
WooCommerce
(www.riskiq.com) - ^
report
(blog.sucuri.net) - ^
skimmers
(blog.sucuri.net) - ^
fake
images (blog.sucuri.net) - ^
theme
(blog.sucuri.net) - ^
files
(blog.sucuri.net)
Read more https://thehackernews.com/2022/06/newly-discovered-magecart.html