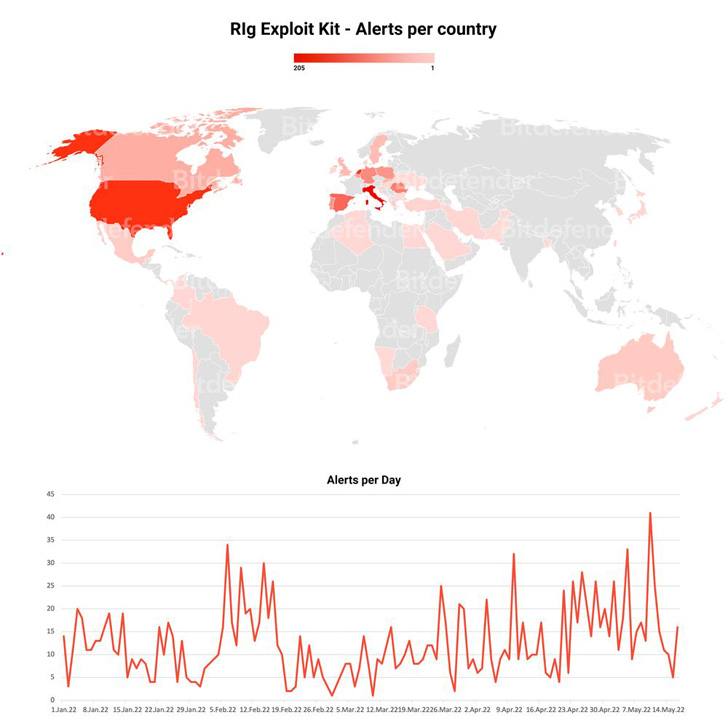
The operators behind the Rig Exploit Kit have swapped the
Raccoon Stealer malware for the Dridex financial trojan as part of
an ongoing campaign that commenced in January 2022.
The switch in modus operandi, spotted[1]
by Romanian company Bitdefender, comes in the wake of Raccoon
Stealer temporarily closing the project[2] after one of its team
members responsible for critical operations passed away in the
Russo-Ukrainian war in March 2022.
The Rig Exploit Kit is notable for its abuse of browser exploits
to distribute an array of malware. First spotted in 2019, Raccoon
Stealer is a credential-stealing trojan that’s advertised and sold
on underground forums as a malware-as-a-service (MaaS) for $200 a
month.
That said, the Raccoon Stealer actors are already working on a
second version that’s expected to be “rewritten from scratch and
optimized.” But the void left by the malware’s exit is being filled
by other information stealers such as RedLine Stealer and
Vidar.
Dridex[3]
(aka Bugat and Cridex), for its part, has the capability to
download additional payloads, infiltrate browsers to steal customer
login information entered on banking websites, capture screenshots,
and log keystrokes, among others, through different modules that
allow its functionality to be extended at will.
In April 2022, Bitdefender discovered[4]
another Rig Exploit Kit campaign distributing the RedLine Stealer
trojan by exploiting an Internet Explorer flaw patched by Microsoft
last year (CVE-2021-26411[5]).
That’s not all. Last May, a separate campaign exploited[6]
two scripting engine vulnerabilities in unpatched Internet Explorer
browsers (CVE-2019-0752[7]
and CVE-2018-8174[8]) to deliver a malware
called WastedLoader, so named for its similarities to WasterLocker
but lacking the ransomware component.
“This once again demonstrates that threat actors are agile and
quick to adapt to change,” the cybersecurity firm said. “By design,
Rig Exploit Kit allows for rapid substitution of payloads in case
of detection or compromise, which helps cyber criminal groups
recover from disruption or environmental changes.”
References
- ^
spotted
(www.bitdefender.com) - ^
temporarily closing the project
(thehackernews.com) - ^
Dridex
(www.cisa.gov) - ^
discovered
(thehackernews.com) - ^
CVE-2021-26411
(thehackernews.com) - ^
exploited
(www.bitdefender.com) - ^
CVE-2019-0752
(nvd.nist.gov) - ^
CVE-2018-8174
(nvd.nist.gov)
Read more https://thehackernews.com/2022/06/rig-exploit-kit-now-infects-victims-pcs.html