CODESYS has released patches to address as many as 11 security
flaws that, if successfully exploited, could result in information
disclosure and a denial-of-service (DoS) condition, among
others.
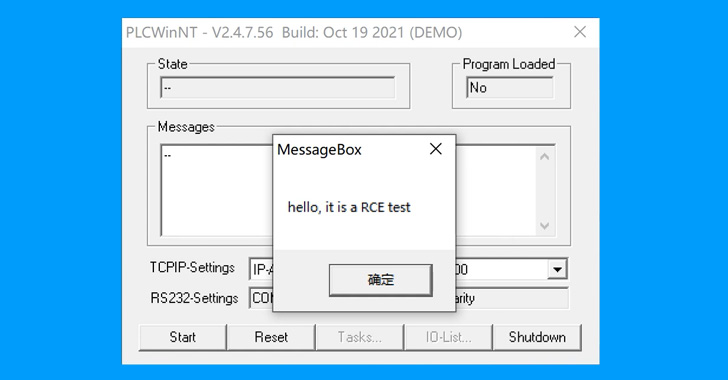
“These vulnerabilities are simple to exploit, and they can be
successfully exploited to cause consequences such as sensitive
information leakage, PLCs entering a severe fault state, and
arbitrary code execution,” Chinese cybersecurity firm NSFOCUS
said[1]. “In combination with
industrial scenarios on the field, these vulnerabilities could
expose industrial production to stagnation, equipment damage,
etc.”
CODESYS is a software[2]
suite[3]
used by automation specialists as a development environment for
programmable logic controller applications (PLCs[4]).
Following responsible disclosure between September 2021 and
January 2022, fixes were shipped[5]
by the German software company last week on June 23, 2022. Two of
the bugs are rated as Critical, seven as High, and two as Medium in
severity. The issues collectively affect the following products
–
- CODESYS Development System prior to version V2.3.9.69
- CODESYS Gateway Client prior to version V2.3.9.38
- CODESYS Gateway Server prior to version V2.3.9.38
- CODESYS Web server prior to version V1.1.9.23
- CODESYS SP Realtime NT prior to version V2.3.7.30
- CODESYS PLCWinNT prior to version V2.4.7.57, and
- CODESYS Runtime Toolkit 32 bit full prior to version
V2.4.7.57
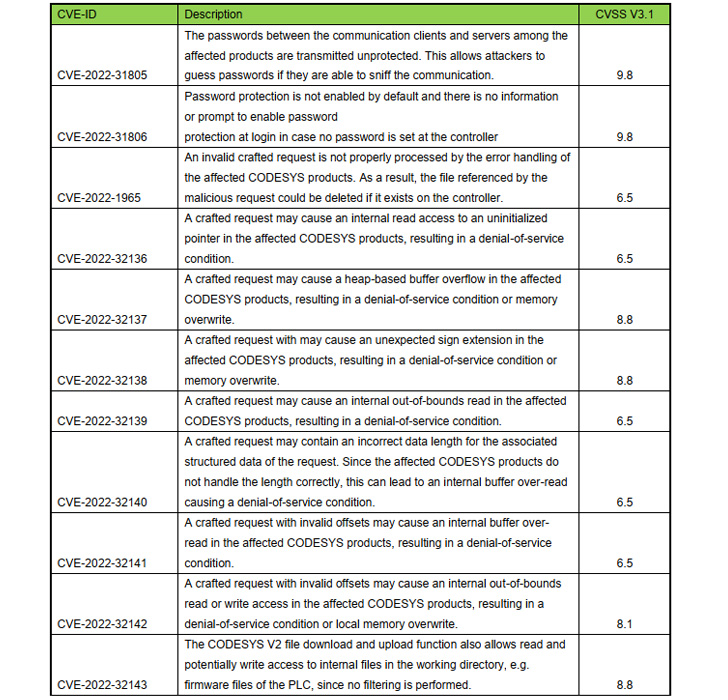
Chief among the flaws are CVE-2022-31805 and CVE-2022-31806
(CVSS scores: 9.8), which relate to the cleartext use of passwords
used to authenticate before carrying out operations on the PLCs and
a failure to enable password protection by default in the CODESYS
Control runtime system respectively.
Exploiting the weaknesses could not only allow a malicious actor
to seize control of the target PLC device, but also download a
rogue project to a PLC and execute arbitrary code.
A majority of the other vulnerabilities (from CVE-2022-32136 to
CVE-2022-32142) could be weaponized by a previously authenticated
attacker on the controller to lead to a denial-of-service
condition.
In a separate advisory published on June 23, CODESYS said it
also remediated three other flaws in CODESYS Gateway Server
(CVE-2022-31802, CVE-2022-31803, and CVE-2022-31804) that could be
leveraged to send crafted requests to bypass authentication and
crash the server.
Besides applying patches in a timely fashion, it’s recommended
to “locate the affected products behind the security protection
devices and perform a defense-in-depth strategy for network
security.”
References
Read more https://thehackernews.com/2022/06/critical-security-flaws-identified-in.html