Cybersecurity researchers have detailed the various measures
ransomware actors have taken to obscure their true identity online
as well as the hosting location of their web server
infrastructure.
“Most ransomware operators use hosting providers outside their
country of origin (such as Sweden, Germany, and Singapore) to host
their ransomware operations sites,” Cisco Talos researcher Paul
Eubanks said[1]. “They use VPS
hop-points as a proxy to hide their true location when they connect
to their ransomware web infrastructure for remote administration
tasks.”
Also prominent are the use of the TOR network and DNS proxy
registration services to provide an added layer of anonymity for
their illegal operations.
But by taking advantage of the threat actors’ operational
security missteps and other techniques, the cybersecurity firm
disclosed last week that it was able to identify TOR hidden
services hosted on public IP addresses, some of which are
previously unknown infrastructure associated with DarkAngels[2], Snatch[3], Quantum[4], and Nokoyawa[5]
ransomware groups.
While ransomware groups are known to rely on the dark web to
conceal their illicit activities ranging from leaking stolen data
to negotiating payments with victims, Talos disclosed that it was
able to identify “public IP addresses hosting the same threat actor
infrastructure as those on the dark web.”
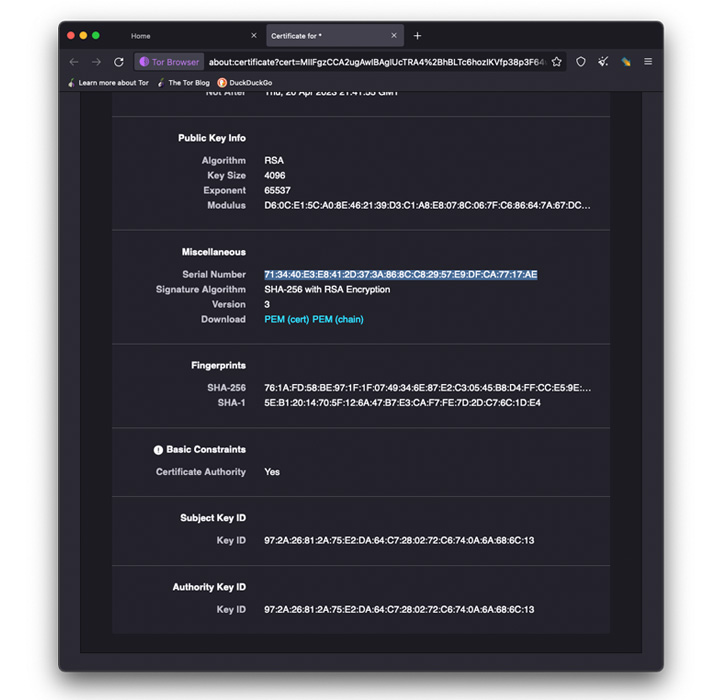
“The methods we used to identify the public internet IPs
involved matching threat actors’ [self-signed] TLS certificate[6]
serial numbers and page elements with those indexed on the public
internet,” Eubanks said.
Besides TLS certificate matching, a second method employed to
uncover the adversaries’ clear web infrastructures entailed
checking the favicons associated with the darknet websites against
the public internet using web crawlers like Shodan.
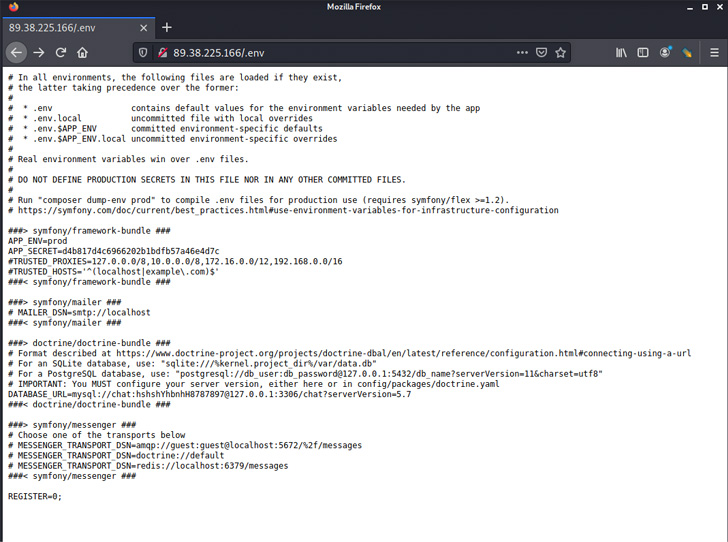
In the case of Nokoyawa[7], a new Windows
ransomware strain that appeared earlier this year and shares
substantial code similarities with Karma, the site hosted on the
TOR hidden service was found to harbor a directory traversal flaw
that enabled the researchers to access the “/var/log/auth.log[8]” file used to capture
user logins.
The findings demonstrate that not only are the criminal actors’
leak sites accessible for any user on the internet, other
infrastructure components, including identifying server data, were
left exposed, effectively making it possible to obtain the login
locations used to administer the ransomware servers.
Further analysis of the successful root user logins showed that
they originated from two IP addresses 5.230.29[.]12 and
176.119.0[.]195, the former of which belongs to GHOSTnet GmbH, a
hosting provider that offers Virtual Private Server (VPS)
services.
“176.119.0[.]195 however belongs to AS58271 which is listed
under the name Tyatkova Oksana Valerievna,” Eubanks noted. “It’s
possible the operator forgot to use the German-based VPS for
obfuscation and logged into a session with this web server directly
from their true location at 176.119.0[.]195.”
LockBit adds a bug bounty program to its revamped RaaS
operation
The development comes as the operators of the emerging Black Basta[9]
ransomware expanded[10] its attack arsenal by
using QakBot for initial access and lateral movement, and taking
advantage of the PrintNightmare vulnerability (CVE-2021-34527[11]) to conduct privileged
file operations.
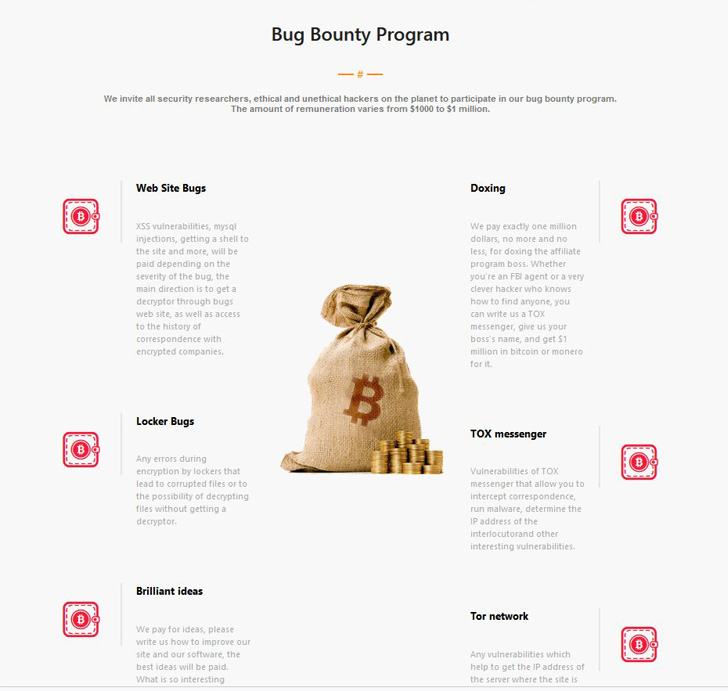
What’s more, the LockBit ransomware gang last week announced[12] the release of LockBit
3.0 with the message “Make Ransomware Great Again!,” in addition to
launching their own Bug Bounty program, offering rewards ranging
between $1,000 and $1 million for identifying security flaws and
“brilliant ideas” to improve its software.
“The release of LockBit 3.0 with the introduction of a bug
bounty program is a formal invitation to cybercriminals to help
assist the group in its quest to remain at the top,” Satnam Narang,
senior staff research engineer at Tenable, said in a statement
shared with The Hacker News.
“A key focus of the bug bounty program are defensive measures:
Preventing security researchers and law enforcement from finding
bugs in its leak sites or ransomware, identifying ways that members
including the affiliate program boss could be doxed, as well as
finding bugs within the messaging software used by the group for
internal communications and the Tor network itself.”
“The threat of being doxed or identified signals that law
enforcement efforts are clearly a great concern for groups like
LockBit. Finally, the group is planning to offer Zcash as a payment
option, which is significant, as Zcash is harder to trace than
Bitcoin, making it harder for researchers to keep tabs on the
group’s activity.”
References
- ^
said
(blog.talosintelligence.com) - ^
DarkAngels
(blog.cyble.com) - ^
Snatch
(malpedia.caad.fkie.fraunhofer.de) - ^
Quantum
(www.cybereason.com) - ^
Nokoyawa
(malpedia.caad.fkie.fraunhofer.de) - ^
TLS
certificate (www.digicert.com) - ^
Nokoyawa
(www.fortinet.com) - ^
/var/log/auth.log
(help.ubuntu.com) - ^
Black
Basta (thehackernews.com) - ^
expanded
(www.trendmicro.com) - ^
CVE-2021-34527
(thehackernews.com) - ^
announced
(twitter.com)
Read more https://thehackernews.com/2022/07/researchers-share-techniques-to-uncover.html