Security researchers have uncovered yet another vulnerability
affecting numerous older AMD and Intel microprocessors that could
bypass current defenses and result in Spectre-based
speculative-execution attacks.
Dubbed Retbleed[1] by ETH Zurich
researchers Johannes Wikner and Kaveh Razavi, the issues are
tracked as CVE-2022-29900 (AMD) and CVE-2022-29901 (Intel), with
the chipmakers releasing[2]
software[3]
mitigations[4]
as part of a coordinated disclosure process.
Retbleed is also the latest addition to a class of Spectre attacks[5]
known as Spectre-BTI (CVE-2017-5715 or Spectre-V2), which exploit
the side effects of an optimization technique called speculative execution[6]
by means of a timing side channel to trick a program into accessing
arbitrary locations in its memory space and leak private
information.
Speculative execution attempts to fill the instruction pipeline
of a program by predicting which instruction will be executed next
in order to gain a performance boost, while also undoing the
results of the execution should the guess turn out to be wrong.
Attacks like Spectre take advantage of the fact that these
erroneously executed instructions — a result of the misprediction —
are bound to leave traces of the execution in the cache, resulting
in a scenario where a rogue program can trick the processor into
executing incorrect code paths and infer secret data pertaining to
the victim.
Put differently, Spectre is an instance of transient execution
attack, which relies on hardware design flaws to “influence” which
instruction sequences are speculatively executed and leak
encryption keys or passwords from within the victim’s memory
address space.
This, in turn, is achieved through microarchitectural side
channels like Flush+Reload[7]
that measures the time taken to perform memory reads from the cache
that’s shared with the victim, but not before flushing some of the
shared memory, resulting in either fast or slow reads depending on
whether the victim accessed the monitored cache line since it was
evicted.
While safeguards like Retpoline[8]
(aka “return trampoline”) have been devised to prevent branch
target injection (BTI), Retbleed is designed to get around this
countermeasure and achieve speculative code execution.
“Retpolines[9]
work by replacing indirect jumps [branches where the branch target
is determined at runtime] and calls with returns,” the researchers
explained.
“Retbleed aims to hijack a return instruction in the kernel to
gain arbitrary speculative code execution in the kernel context.
With sufficient control over registers and/or memory at the victim
return instruction, the attacker can leak arbitrary kernel
data.”
The core idea, in a nutshell, is to treat return instructions[10] as an attack vector for
speculation execution and force the returns to be predicted like
indirect branches, effectively undoing protections offered by
Retpoline.
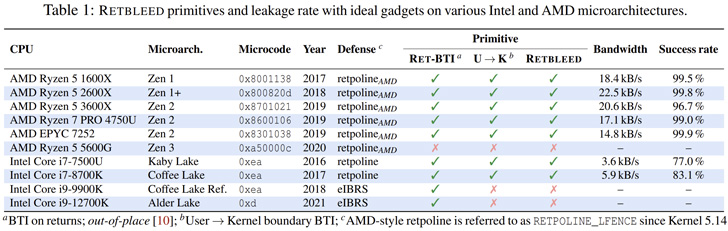
As a new line of defense, AMD has introduced what’s referred to
as Jmp2Ret[11], while Intel has
recommended[12] using enhanced Indirect
Branch Restricted Speculation (eIBRS[13]) to address the
potential vulnerability even if Retpoline mitigations are in
place.
“Windows operating system uses IBRS by default, so no update is
required,” Intel said in an advisory, noting it worked with the
Linux community to make available software updates for the
shortcoming.
References
- ^
Retbleed
(comsec.ethz.ch) - ^
releasing
(www.amd.com) - ^
software
(www.intel.com) - ^
mitigations
(www.intel.com) - ^
Spectre
attacks (thehackernews.com) - ^
speculative execution
(en.wikipedia.org) - ^
Flush+Reload
(thehackernews.com) - ^
Retpoline
(support.google.com) - ^
Retpolines
(www.intel.com) - ^
return
instructions (en.wikipedia.org) - ^
Jmp2Ret
(www.amd.com) - ^
recommended
(www.intel.com) - ^
eIBRS
(www.intel.com)
Read more https://thehackernews.com/2022/07/new-retbleed-speculative-execution.html