Microsoft on Wednesday shed light on a now patched security
vulnerability affecting Apple’s operating systems that, if
successfully exploited, could allow attackers to escalate device
privileges and deploy malware.
“An attacker could take advantage of this sandbox escape
vulnerability to gain elevated privileges on the affected device or
execute malicious commands like installing additional payloads,”
Jonathan Bar Or of the Microsoft 365 Defender Research Team
said[1]
in a write-up.
Tracked as CVE-2022-26706[2]
(CVSS score: 5.5), the security vulnerability impacts iOS, iPadOS,
macOS, tvOS, and watchOS and was fixed by Apple in May 2022.
Calling it an access issue affecting the LaunchServices
(launchd) component, the tech giant noted that “A sandboxed process
may be able to circumvent sandbox restrictions,” adding it
mitigates the issue with additional restrictions.
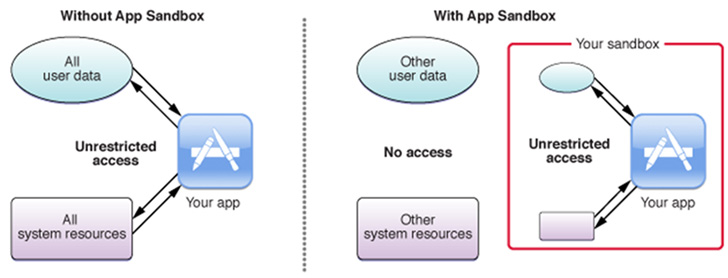
While Apple’s App Sandbox[3]
is designed to tightly regulate a third-party app’s access to
system resources and user data, the vulnerability makes it possible
to bypass these restrictions and compromise the machine.
“The sandbox’s primary function is to contain damage to the
system and the user’s data if the user executes a compromised app,”
Apple explains[4]
in its documentation.
“While the sandbox doesn’t prevent attacks against your app, it
does reduce the harm a successful attack can cause by restricting
your app to the minimum set of privileges it requires to function
properly.”
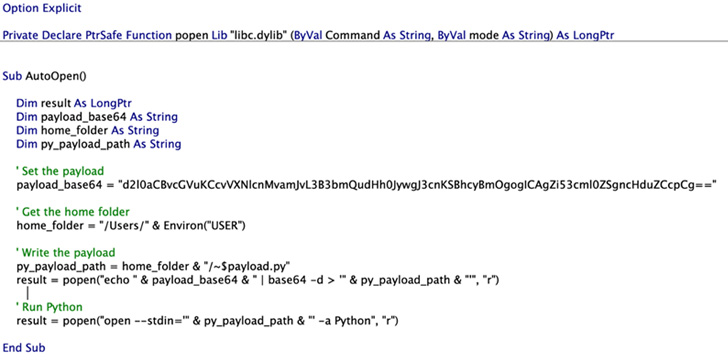
Microsoft said it discovered the flaw during its attempts to
figure out a way to escape the sandbox and execute arbitrary
commands on macOS by concealing the malicious code in a specially
crafted Microsoft Office macro.
Specifically, the tweet-sized proof-of-concept (PoC) devised by
the tech giant leverages Launch Services as a means to run an
open command[5]
— a utility used to open files and launch apps — on a Python
payload containing rogue instructions.
But it’s worth noting that any file dropped by a sandboxed app
is automatically attached to the “com.apple.quarantine[6]” extended attribute so
as to trigger[7]
a prompt requiring explicit user’s consent prior to execution.
This constraint, however, can be eliminated by utilizing the
-stdin option for the open command associated with the Python
exploit file.
“–stdin bypassed the ‘com.apple.quarantine’ extended attribute
restriction, as there was no way for Python to know that the
contents from its standard input originated from a quarantined
file,” Bar Or said.
References
- ^
said
(www.microsoft.com) - ^
CVE-2022-26706
(nvd.nist.gov) - ^
App
Sandbox (developer.apple.com) - ^
explains
(developer.apple.com) - ^
open
command (www.trendmicro.com) - ^
com.apple.quarantine
(objective-see.org) - ^
trigger
(support.apple.com)
Read more https://thehackernews.com/2022/07/microsoft-details-app-sandbox-escape.html