Researchers from Wordfence have sounded[1]
the alarm about a “sudden” spike in cyber attacks attempting to
exploit an unpatched flaw in a WordPress plugin called Kaswara Modern WPBakery Page Builder
Addons[2].
Tracked as CVE-2021-24284[3], the issue is rated 10.0
on the CVSS vulnerability scoring system and relates to an
unauthenticated arbitrary file upload that could be abused to gain
code execution, permitting attackers to seize control of affected
WordPress sites.
Although the bug was originally disclosed[4]
in April 2021 by the WordPress security company, it continues to
remain unresolved to date. To make matters worse, the plugin has
been closed and is no longer actively maintained.
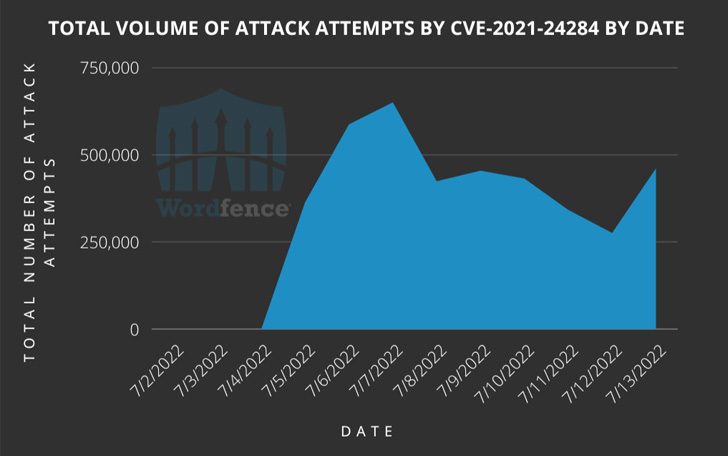
Wordfence, which is protecting over 1,000 websites that have the
plugin installed, said it has blocked an average of 443,868 attack
attempts per day since the start of the month.
The attacks have emanated from 10,215 IP addresses, with a
majority of the exploitation attempts narrowed down to 10 IP
addresses. These involve uploading a ZIP archive containing a
malicious PHP file that allows the attacker to upload rogue files
to the infected website.
The goal of the campaign, it appears, is to insert code into
otherwise legitimate JavaScript files and redirect site visitors to
malicious websites. It’s worth noting that the attacks have been
tracked by Avast and Sucuri under the monikers Parrot TDS[5]
and NDSW[6], respectively.
Between 4,000 and 8,000 websites are said to have the plugin
installed, making it imperative that users remove it from their
WordPress sites to thwart potential attacks and find an appropriate
alternative.
References
- ^
sounded
(www.wordfence.com) - ^
Kaswara
Modern WPBakery Page Builder Addons
(codecanyon.net) - ^
CVE-2021-24284
(nvd.nist.gov) - ^
disclosed
(www.wordfence.com) - ^
Parrot
TDS (thehackernews.com) - ^
NDSW
(thehackernews.com)
Read more https://thehackernews.com/2022/07/experts-notice-sudden-surge-in.html