Cybersecurity researchers have taken the wraps off a previously
undocumented spyware targeting the Apple macOS operating
system.
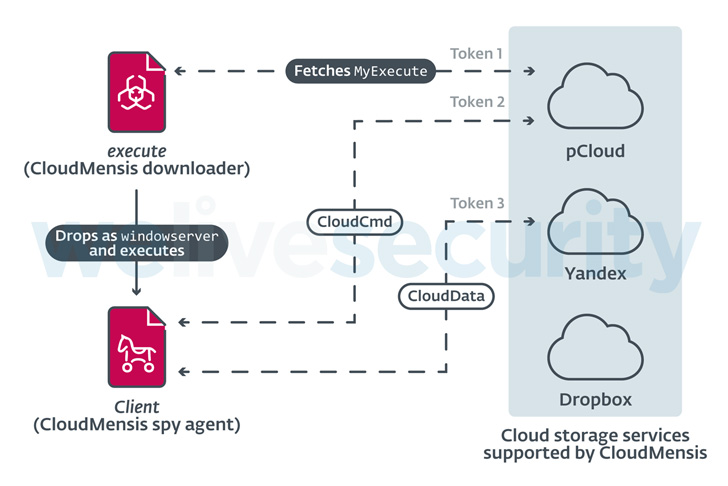
The malware, codenamed CloudMensis by Slovak
cybersecurity firm ESET, is said to exclusively use public cloud
storage services such as pCloud, Yandex Disk, and Dropbox for
receiving attacker commands and exfiltrating files.
“Its capabilities clearly show that the intent of its operators
is to gather information from the victims’ Macs by exfiltrating
documents, keystrokes, and screen captures,” ESET researcher
Marc-Etienne M.Léveillé said[1]
in a report published today.
CloudMensis, written in Objective-C, was first discovered in
April 2022 and is designed to strike both Intel and Apple silicon
architectures. The initial infection vector for the attacks and the
targets remain unknown as yet. But its very limited distribution is
an indication that the malware is being used as part of a highly
targeted operation directed against entities of interest.
The attack chain spotted by ESET abuses code execution and
administrative privileges to launch a first-stage payload that’s
utilized to fetch and execute a second-stage malware hosted on
pCloud, which, in turn, exfiltrates documents, screenshots, and
email attachments, among others.
The first-stage downloader is also known to erase traces of
Safari sandbox escape and privilege escalation exploits that make
use of four now-resolved security flaws[2] in 2017, suggesting that
CloudMensis may have flown under the radar for many years.
The implant also comes with features to bypass the Transparency,
Consent, and Control (TCC[3]) security framework,
which aims to ensure that all apps obtain user consent before
accessing files in Documents, Downloads, Desktop, iCloud Drive, and
network volumes.
It achieves this by exploiting another patched security
vulnerability tracked as CVE-2020-9934[4]
that came to light in 2020. Other functions supported by the
backdoor include getting the list of running processes, capturing
screenshots, listing files from removable storage devices, and
running shell commands and other arbitrary payloads.
On top of that, an analysis of metadata from the cloud storage
infrastructure shows that the pCloud accounts were created on
January 19, 2022, with the compromises commencing on February 4 and
peaking in March.
“The general quality of the code and lack of obfuscation shows
the authors may not be very familiar with Mac development and are
not so advanced,” M.Léveillé said. “Nonetheless a lot of resources
were put into making CloudMensis a powerful spying tool and a
menace to potential targets.”
References
- ^
said
(www.welivesecurity.com) - ^
four
now-resolved security flaws (phoenhex.re) - ^
TCC
(support.apple.com) - ^
CVE-2020-9934
(thehackernews.com)
Read more https://thehackernews.com/2022/07/experts-uncover-new-cloudmensis-spyware.html