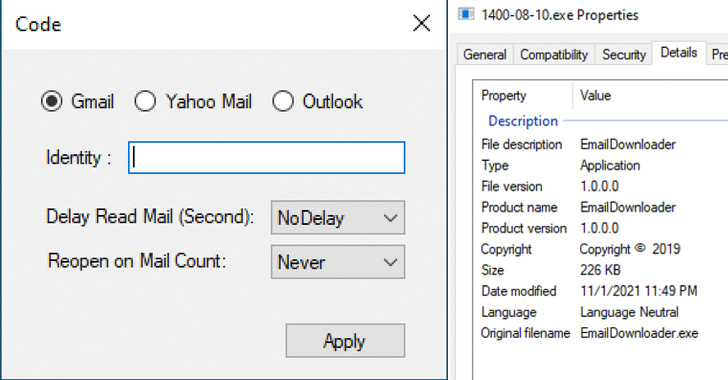
The Iranian government-backed actor known as Charming Kitten has
added a new tool to its malware arsenal that allows it to retrieve
user data from Gmail, Yahoo!, and Microsoft Outlook accounts.
Dubbed HYPERSCRAPE by Google Threat Analysis
Group (TAG), the actively in-development malicious software is said
to have been used against less than two dozen accounts in Iran,
with the oldest known sample dating back to 2020. The tool was
first discovered in December 2021.
Charming Kitten, a prolific advanced persistent threat (APT), is
believed to be associated[1]
with Iran’s Islamic Revolutionary Guard Corps (IRGC) and has a
history of conducting espionage aligned with the interests of the
government.
Tracked as APT35, Cobalt Illusion, ITG18, Phosphorus, TA453, and
Yellow Garuda, elements of the group have also carried out
ransomware attacks, suggesting that the threat actor’s motives are
both espionage and financially driven.
“HYPERSCRAPE requires the victim’s account credentials to run
using a valid, authenticated user session the attacker has
hijacked, or credentials the attacker has already acquired,” Google
TAG researcher Ajax Bash said[2].
Written in .NET and designed to run on the attacker’s Windows
machine, the tool comes with functions to download and exfiltrate
the contents of a victim’s email inbox, in addition to deleting
security emails sent from Google to alert the target of any
suspicious logins.
Should a message be originally unread, the tool marks it as
unread after opening and downloading the email as a “.eml” file.
What’s more, earlier versions of HYPERSCRAPE are said to have
included an option to request data from Google Takeout[3], a feature that allows
users to export their data to a downloadable archive file.
The findings follow the recent discovery of a C++-based Telegram “grabber” tool[4]
by PwC used against domestic targets to obtain access to Telegram
messages and contacts from specific accounts.
Previously, the group was spotted deploying a custom Android
surveillanceware called LittleLooter[5], a feature-rich implant
capable of gathering sensitive information stored in the
compromised devices as well as recording audio, video, and
calls.
“Like much of their tooling, HYPERSCRAPE is not notable for its
technical sophistication, but rather its effectiveness in
accomplishing Charming Kitten’s objectives,” Bash said. The
affected accounts have since been re-secured and the victims
notified.
References
- ^
associated
(thehackernews.com) - ^
said
(blog.google) - ^
Google
Takeout (support.google.com) - ^
Telegram
“grabber” tool (www.pwc.com) - ^
LittleLooter
(securityintelligence.com)
Read more https://thehackernews.com/2022/08/google-uncovers-tool-used-by-iranian.html