A suspected Iranian threat activity cluster has been linked to
attacks aimed at Israeli shipping, government, energy, and
healthcare organizations as part of an espionage-focused campaign
that commenced in late 2020.
Cybersecurity firm Mandiant is tracking the group under its
uncategorized moniker UNC3890, which is believed
to conduct operations that align with Iranian interests.
“The collected data may be leveraged to support various
activities, from hack-and-leak, to enabling kinetic warfare attacks
like those that have plagued the shipping industry in recent
years,” the company’s Israel Research Team noted[1].
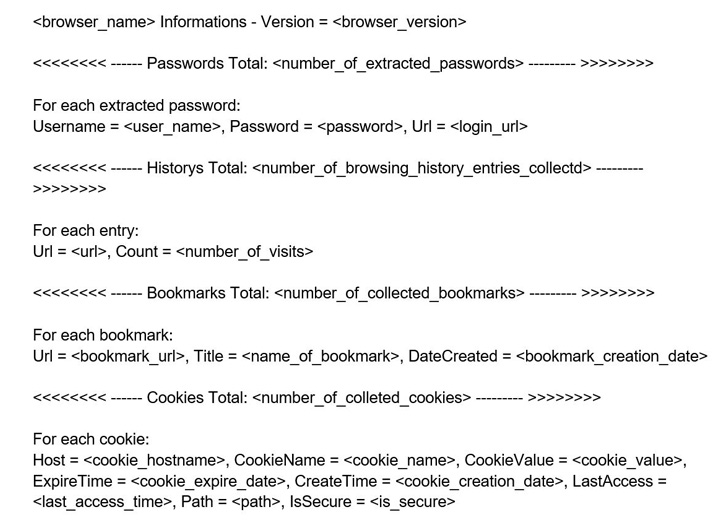
Intrusions mounted by the group lead to the deployment of two
proprietary pieces of malware: a “small but efficient” backdoor
named SUGARUSH and a browser credential stealer called SUGARDUMP
that exfiltrates password information to an email address
associated with Gmail, ProtonMail, Yahoo, and Yandex.
Also employed is a network of command-and-control (C2) servers
that host fake login pages impersonating legitimate platforms such
as Office 365, LinkedIn, and Facebook that are designed to
communicate with the targets as well as a watering hole that’s
believed to have singled out the shipping sector.
The watering hole, as of November 2021, was hosted on a login
page of a legitimate Israeli shipping company, Mandiant pointed
out, adding the malware transmitted preliminary data about the
logged-in user to an attacker-controlled domain.
While the exact methodology for initial access remains unknown,
it’s suspected to involve a mix of watering holes, credential
harvesting by masquerading as legitimate services, and fraudulent
job offers for a software developer position at a data analytics
firm LexisNexis.
“One of UNC3890’s most recent endeavors to target victims
includes the usage of a video commercial for AI-based robotic
dolls, used as a lure to deliver SUGARDUMP,” the researchers
noted.
SUGARUSH, the second bespoke malware, works by establishing a
connection with an embedded C2 server to execute arbitrary CMD
commands issued by the attacker, granting the adversary full
control over the victim’s environment upon gaining initial
access.
Other tools used by UNC3890 include the Metasploit penetration
testing software and Unicorn, a publicly available utility for
conducting a PowerShell downgrade attack and injecting shellcode
into memory.
The group’s connections to Iran stem from the use of Farsi
language artifacts in the newest version of SUGARDUMP, the
consistent targeting of Israeli entities that dovetails with other
Iranian threat actor clusters, and the usage of the NorthStar C2
Framework.
Read more https://thehackernews.com/2022/08/suspected-iranian-hackers-targeted.html