A Linux variant of a backdoor known as SideWalk was used to
target a Hong Kong university in February 2021, underscoring the
cross-platform abilities of the implant.
Slovak cybersecurity firm ESET, which detected the malware in
the university’s network, attributed the backdoor to a nation-state
actor dubbed SparklingGoblin. The unnamed
university is said to have been already targeted by the group in
May 2020 during the student protests[1].
“The group continuously targeted this organization over a long
period of time, successfully compromising multiple key servers,
including a print server, an email server, and a server used to
manage student schedules and course registrations,” ESET said[2]
in a report shared with The Hacker News.
SparklingGoblin is the name given to a Chinese advanced
persistent threat (APT) group with connections to the Winnti umbrella[3]
(aka APT41, Barium, or Wicked Panda). It’s primarily known for its
attacks targeting various entities in East and Southeast Asia at
least since 2019, with a specific focus on the academic sector.
In August 2021, ESET unearthed a new piece of custom Windows
malware codenamed SideWalk[4]
that was exclusively leveraged by the actor to strike an unnamed
computer retail company based in the U.S.
Subsequent findings from Symantec, part of Broadcom software,
have linked the use of SideWalk to an espionage attack group it
tracks under the moniker Grayfly[5], while pointing out the
malware’s similarities to that of Crosswalk.
“SparklingGoblin’s Tactics, Techniques and Procedures (TTPs)
partially overlap with APT41 TTPs,” Mathieu Tartare, malware
researcher at ESET, told The Hacker News. “Grayfly’s definition
given by Symantec seems to (at least partially) overlap with
SparklingGoblin.”
The latest research from ESET dives into SideWalk’s Linux
counterpart (originally called StageClient[6]
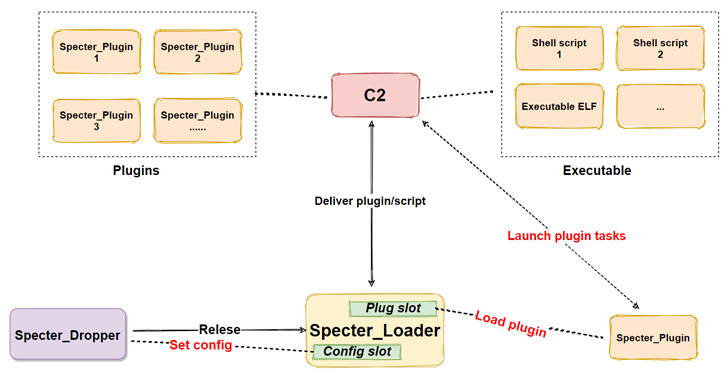
in July 2021), with the analysis also uncovering that Specter RAT[7], a Linux botnet that
came to light in September 2020, is in fact a Linux variant of
SideWalk as well.
Aside from multiple code similarities between the SideWalk Linux
and various SparklingGoblin tools, one of the Linux samples has
been found using a command-and-control address (66.42.103[.]222)
that was previously used by
SparklingGoblin[8].
Other commonalities include the use of the same bespoke ChaCha20
implementation, multiple threads to execute one particular task,
ChaCha20 algorithm for decrypting its configuration, and an
identical dead drop resolver[9]
payload.
Despite these overlaps, there are some significant changes, the
most notable being the switch from C to C++, addition of new
built-in modules to execute scheduled tasks and gather system
information, and changes to four commands that are not handled in
the Linux version.
“Since we have seen the Linux variant only once in our telemetry
(deployed at a Hong Kong university in February 2021) one can
consider the Linux variant to be less prevalent — but we also have
less visibility on Linux systems which could explain this,” Tartare
said.
“On the other hand, the Specter Linux variant is used against IP
cameras and NVR and DVR devices (on which we have no visibility)
and is mass spread by exploiting a vulnerability on such
devices.”
References
- ^
student
protests (en.wikipedia.org) - ^
said
(www.welivesecurity.com) - ^
Winnti
umbrella (www.mandiant.com) - ^
SideWalk
(thehackernews.com) - ^
Grayfly
(thehackernews.com) - ^
StageClient
(twitter.com) - ^
Specter
RAT (blog.netlab.360.com) - ^
previously used by SparklingGoblin
(thehackernews.com) - ^
dead
drop resolver (attack.mitre.org)
Read more https://thehackernews.com/2022/09/sparklinggoblin-apt-hackers-using-new.html