Details have emerged about a previously undocumented and fully
undetectable (FUD) PowerShell backdoor that gains its stealth by
disguising itself as part of a Windows update process.
“The covert self-developed tool and the associated C2 commands
seem to be the work of a sophisticated, unknown threat actor who
has targeted approximately 100 victims,” Tomer Bar, director of
security research at SafeBreach, said[1]
in a new report.
Attributed to an unnamed threat actor[2], attack chains involving
the malware commence with a weaponized Microsoft Word document[3]
that, per the company, was uploaded from Jordan on August 25,
2022.
Metadata associated with the lure document indicates that the
initial intrusion vector is a LinkedIn-based spear-phishing attack,
which ultimately leads to the execution of a PowerShell script via
a piece of embedded macro code.
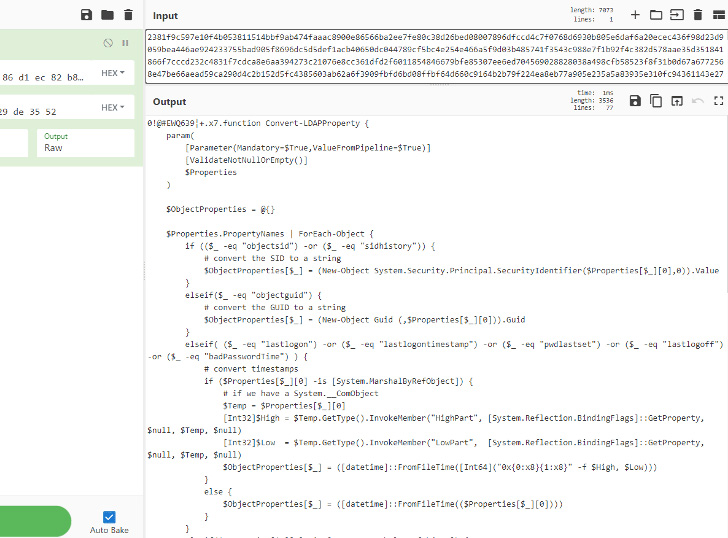
The PowerShell script (Script1.ps1[4]) is designed to connect
to a remote command-and-control (C2) server and retrieve a command
to be launched on the compromised machine by means of a second
PowerShell script (temp.ps1[5]).
But an operational security error made by the actor by using a
trivial incremental identifier to uniquely identify each victim
(i.e., 0, 1, 2, etc.) allowed for reconstructing the commands
issued by the C2 server.
Some of the notable commands issued consist of exfiltrating the
list of running processes, enumerating files in specific folders,
launching whoami, and deleting files under the public user
folders.
As of writing, 32 security vendors and 18 anti-malware engines
flag the decoy document and the PowerShell scripts as malicious,
respectively.
The findings come as Microsoft has taken steps[6]
to block Excel 4.0 (XLM or XL4) and Visual Basic for Applications
(VBA) macros by default across Office apps, prompting threat actors
to pivot to alternative delivery methods[7].
References
- ^
said
(www.safebreach.com) - ^
unnamed
threat actor (securelist.com) - ^
Microsoft Word document
(www.virustotal.com) - ^
Script1.ps1
(www.virustotal.com) - ^
temp.ps1
(www.virustotal.com) - ^
taken
steps (thehackernews.com) - ^
alternative delivery methods
(thehackernews.com)
Read more https://thehackernews.com/2022/10/experts-warn-of-stealthy-powershell.html