The Amadey malware is being used to deploy LockBit 3.0 ransomware[1]
on compromised systems, researchers have warned.
“Amadey bot, the malware that is used to install LockBit, is
being distributed through two methods: one using a malicious Word
document file, and the other using an executable that takes the
disguise of the Word file icon,” AhnLab Security Emergency Response
Center (ASEC) said[2]
in a new report published today.
Amadey, first discovered in 2018, is a “criminal-to-criminal
(C2C) botnet infostealer project,” as described[3]
by the BlackBerry Research and Intelligence Team, and is offered
for purchase on the criminal underground for as much as $600.
While its primary function is to harvest sensitive information
from the infected hosts, it further doubles up as a channel to
deliver next-stage artifacts. Earlier this July, it was spread using SmokeLoader[4], a malware with
not-so-different features like itself.
Just last month, ASEC also found[5] the malware distributed
under the disguise of KakaoTalk, an instant messaging service
popular in South Korea, as part of a phishing campaign.
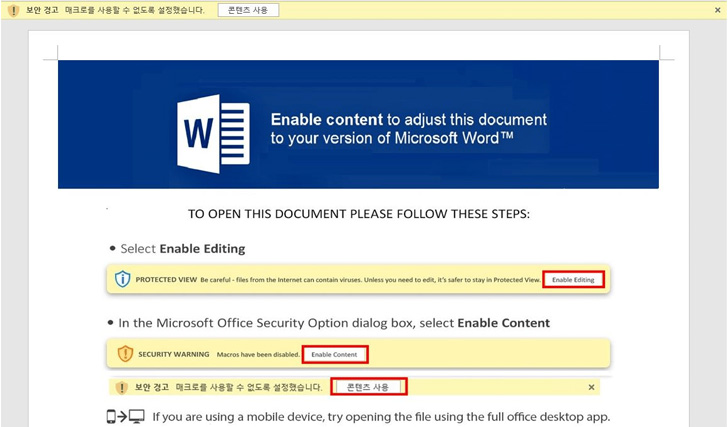
The cybersecurity firm’s latest analysis is based on a Microsoft
Word file (“심시아.docx[6]“) that was uploaded to
VirusTotal on October 28, 2022. The document contains a malicious
VBA macro that, when enabled by the victim, runs a PowerShell
command to download and run Amadey.
In an alternative attack chain, Amadey is disguised as a
seemingly harmless file bearing a Word icon but is actually an
executable (“Resume.exe”) that’s propagated via a phishing message.
ASEC said it was not able to identify the email used as a lure.
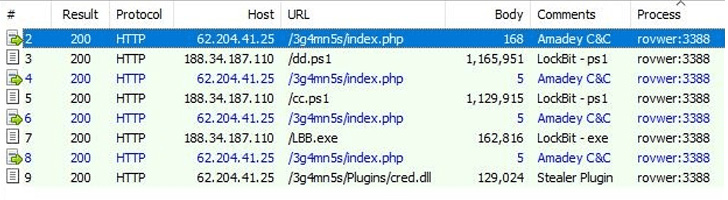
Succeeding in the execution of Amadey, the malware fetches and
launches additional commands from a remote server, which includes
the LockBit ransomware either in PowerShell (.ps1) or binary (.exe)
formats.
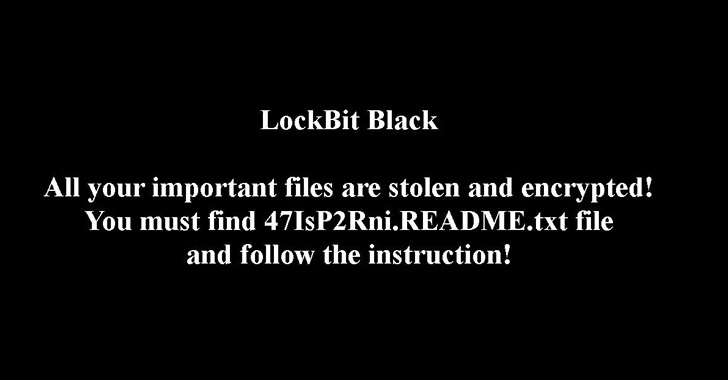
LockBit 3.0[7], also known as LockBit Black[8], launched in June 2022,
alongside a new dark web portal and the very first bug bounty program[9]
for a ransomware operation, promising rewards of up to $1 million
for finding bugs in its website and software.
“As LockBit ransomware is being distributed through various
methods, user caution is advised,” the researchers concluded.
References
- ^
LockBit
3.0 ransomware (thehackernews.com) - ^
said
(asec.ahnlab.com) - ^
described
(blogs.blackberry.com) - ^
spread
using SmokeLoader (thehackernews.com) - ^
found
(asec.ahnlab.com) - ^
심시아.docx
(www.virustotal.com) - ^
LockBit
3.0 (research.nccgroup.com) - ^
LockBit
Black (www.malwarebytes.com) - ^
bug
bounty program (blogs.vmware.com)
Read more https://thehackernews.com/2022/11/amadey-bot-spotted-deploying-lockbit-30.html