Cybersecurity researchers have unearthed new samples of malware
called RapperBot that are being used to build a botnet capable of
launching Distributed Denial of Service (DDoS) attacks against game
servers.
“In fact, it turns out that this campaign is less like RapperBot
than an older campaign that appeared in February and then
mysteriously disappeared in the middle of April,” Fortinet
FortiGuard Labs researchers Joie Salvio and Roy Tay said[1]
in a Tuesday report.
RapperBot, which was first documented[2]
by the network security firm in August 2022, is known to
exclusively brute-force SSH servers configured to accept password authentication[3].
The nascent malware is heavily inspired by the Mirai botnet[4], whose source code
leaked in October 2016, leading to the rise of several
variants.
What’s notable about the updated version of RapperBot is its
ability to perform Telnet brute-force, in addition to supporting
DoS attacks using the Generic Routing Encapsulation (GRE[5]) tunneling protocol.
“The Telnet brute-forcing code is designed primarily for
self-propagation and resembles the old Mirai Satori botnet,” the
researchers said.
This list of hard-coded plaintext credentials, which are default
credentials associated with IoT devices, are embedded into the
binary as opposed to retrieving it from a command-and-control (C2)
server, a behavior that was observed in artifacts detected after
July 2022.
A successful break-in is followed by reporting the credentials
used back to the C2 server and installing the RapperBot payload on
the hacked device.
Fortinet said the malware is designed to only target appliances
that run on ARM, MIPS, PowerPC, SH4, and SPARC architectures, and
halt its self-propagation mechanism should they be running on Intel
chipsets.
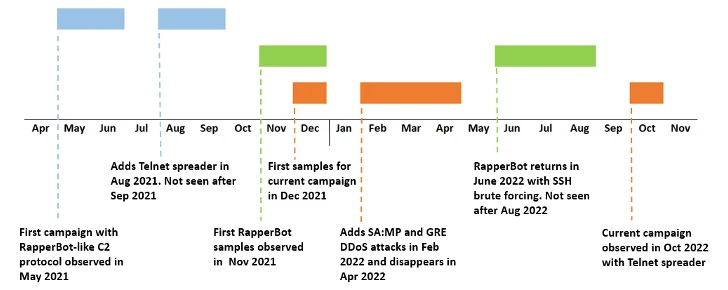
What’s more, the October 2022 campaign has been found to share
overlaps with other operations involving the malware as far back as
May 2021, with the Telnet spreader module making its first
appearance in August 2021, only to be removed in later samples and
reintroduced last month.
“Based on the undeniable similarities between this new campaign
and the previously reported RapperBot campaign, it is highly likely
that they are being operated by a single threat actor or by
different threat actors with access to a privately-shared base
source code,” the researchers concluded.
References
- ^
said
(www.fortinet.com) - ^
documented
(thehackernews.com) - ^
password
authentication (www.hostinger.com) - ^
Mirai
botnet (thehackernews.com) - ^
GRE
(en.wikipedia.org)
Read more https://thehackernews.com/2022/11/warning-new-rapperbot-campaign-aims-to.html