Cybersecurity researchers took the wraps off a new spyware
operation targeting users in Pakistan that leverages trojanized
versions of legitimate Android apps to carry out covert
surveillance and espionage.
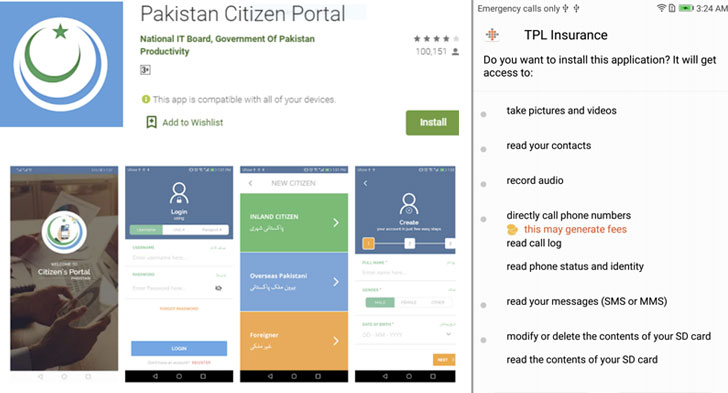
Designed to masquerade apps such as the Pakistan Citizen
Portal, a Muslim prayer-clock app called Pakistan Salat
Time, Mobile Packages Pakistan, Registered SIMs
Checker, and TPL Insurance, the malicious variants have
been found to obfuscate their operations to stealthily download a
payload in the form of an Android Dalvik executable (DEX) file.
“The DEX payload contains most of the malicious features, which
include the ability to covertly exfiltrate sensitive data like the
user’s contact list and the full contents of SMS messages,”
Sophos[1]
threat researchers Pankaj Kohli and Andrew Brandt said.
“The app then sends this information to one of a small number of
command-and-control websites hosted on servers located in eastern
Europe.”
Interestingly, the fake website of the Pakistan Citizen Portal
was also prominently displayed in the form of a static image on the
Trading Corporation of Pakistan (TCP) website, potentially in an
attempt to lure unsuspecting users into downloading the
malware-laced app.
Visiting the TCP website (tcp.gov.pk) now shows the message
“Down for Maintenance.”
Besides the aforementioned apps, Sophos researchers also
discovered a separate app called Pakistan Chat that didn’t have a
benign analogue distributed via the Google Play Store. But the app
was found to leverage the API of a legitimate chat service called
ChatGum.
Once installed, the app requests intrusive permissions,
including the ability to access contacts, file system, location,
microphone, and read SMS messages, which allow it to gather a wide
swathe of data on a victim’s device.
All these apps have one singular purpose — to conduct covert
surveillance and exfiltrate the data from a target device. In
addition to sending the unique IMEI identifier, the DEX payload
relays detailed profile information about the phone, location
information, contact lists, the contents of text messages, call
logs and the full directory listing of any internal or SD card
storage on the device.
Troublingly, the malicious Pakistan Citizen Portal app also
transmits sensitive information such as users’ computerized
national identity card (CNIC[2]) numbers, their passport
details, and the username and password for Facebook and other
accounts.
“The spying and covert surveillance capability of these modified
Android apps highlight the dangers of spyware to smartphone users
everywhere,” Pankaj Kohli said. “Cyber-adversaries target mobiles
not just to get their hands on sensitive and personal information,
but because they offer a real-time window into people’s lives,
their physical location, movements, and even live conversations
taking place within listening range of the infected phone.”
If anything, the development is yet another reason why users
need to stick to trusted sources to download third-party apps,
verify if an app is indeed built by a genuine developer, and
carefully scrutinize app permissions before installation.
“In the current Android ecosystem, apps are cryptographically
signed as a way to certify the code originates with a legitimate
source, tying the app to its developer,” the researchers concluded.
“However, Android doesn’t do a good job exposing to the end user
when a signed app’s certificate isn’t legitimate or doesn’t
validate. As such, users have no easy way of knowing if an app was
indeed published by its genuine developer.”
“This allows threat actors to develop and publish fake versions
of popular apps. The existence of a large number of app stores, and
the freedom of users to install an app from practically anywhere
makes it even harder to combat such threats.”