Open-source Tor browser has been updated to version 10.0.18 with
fixes for multiple issues, including a privacy-defeating bug that
could be used to uniquely fingerprint users across different
browsers based on the apps installed on a computer.
In addition to updating[1]
Tor to 0.4.5.9, the browser’s Android version has been upgraded to
Firefox to version 89.1.1, alongside incorporating patches rolled
out by Mozilla for several security vulnerabilities[2] addressed in Firefox
89.
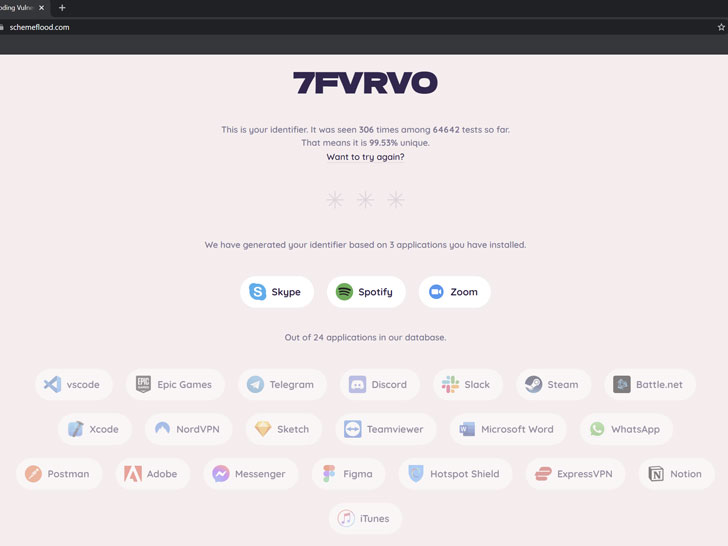
Chief among the rectified issues is a new fingerprinting attack
that came to light last month. Dubbed scheme flooding[3], the vulnerability
enables a malicious website to leverage information about installed
apps on the system to assign users a permanent unique identifier
even when they switch browsers, use incognito mode, or a VPN.
Put differently, the weakness[4]
takes advantage of custom URL schemes in apps as an attack vector,
allowing a bad actor to track a device’s user between different
browsers, including Chrome, Firefox, Microsoft Edge, Safari, and
even Tor, effectively circumventing cross-browser anonymity
protections on Windows, Linux, and macOS.
“A website exploiting the scheme flooding vulnerability could
create a stable and unique identifier that can link those browsing
identities together,” FingerprintJS researcher Konstantin Darutkin
said.
Currently, the attack checks a list of 24 installed applications
that consists of Adobe, Battle.net, Discord, Epic Games,
ExpressVPN, Facebook Messenger, Figma, Hotspot Shield, iTunes,
Microsoft Word, NordVPN, Notion, Postman, Sketch, Skype, Slack,
Spotify, Steam, TeamViewer, Telegram, Visual Studio Code, WhatsApp,
Xcode, and Zoom.
The issue has serious implications for privacy as it could be
exploited by adversaries to unmask Tor users by correlating their
browsing activities as they switch to a non-anonymizing browser,
such as Google Chrome. To counter the attack[5], Tor now sets
“network.protocol-handler.external” to false so as to block the
browser from probing installed apps.
Of the other three browsers, while Google Chrome features
built-in safeguards[6]
against scheme flooding — it prevents launching any application
unless it’s triggered by a user gesture, like a mouse click — the
browser’s PDF Viewer[7]
was found to bypass this mitigation.
“Until this vulnerability is fixed, the only way to have private
browsing sessions not associated with your primary device is to use
another device altogether,” Darutkin said. Tor browser users are
recommended to move quickly to apply the update to ensure they are
protected.
The development arrives little over a week after encrypted
messaging service Wire addressed[8] two critical
vulnerabilities in its iOS and web app that could lead to a
denial-of-service (CVE-2021-32666[9]) and permit an attacker
to take control of a user account (CVE-2021-32683[10]).
References
- ^
updating
(blog.torproject.org) - ^
security
vulnerabilities (www.mozilla.org) - ^
scheme
flooding (fingerprintjs.com) - ^
weakness
(github.com) - ^
counter
the attack (gitlab.torproject.org) - ^
built-in
safeguards (bugs.chromium.org) - ^
PDF
Viewer (bugs.chromium.org) - ^
addressed
(twitter.com) - ^
CVE-2021-32666
(github.com) - ^
CVE-2021-32683
(github.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/XKKC6PkSyXg/patch-tor-browser-bug-to-prevent.html