A prominent Togolese human rights defender has been targeted
with spyware by a threat actor known for striking victims in South
Asia, marking the hacking group’s first foray into digital
surveillance in Africa.
Amnesty International tied the covert attack campaign to a
collective tracked as “Donot Team[1]” (aka APT-C-35), which
has been linked to cyber offensives in India and Pakistan, while
also identifying apparent evidence linking the group’s
infrastructure to an Indian company called Innefu Labs. The unnamed
activist is believed to have targeted over a period of two months
starting in December 2019 with the help of fake Android
applications and spyware-loaded emails.
“The persistent attacks over WhatsApp and email tried to trick
the victim into installing a malicious application that masqueraded
as a secure chat application,” Amnesty International said[2]
in a report published last week. “The application was in fact a
piece of custom Android spyware designed to extract some of the
most sensitive and personal information stored on the activist’s
phone.”
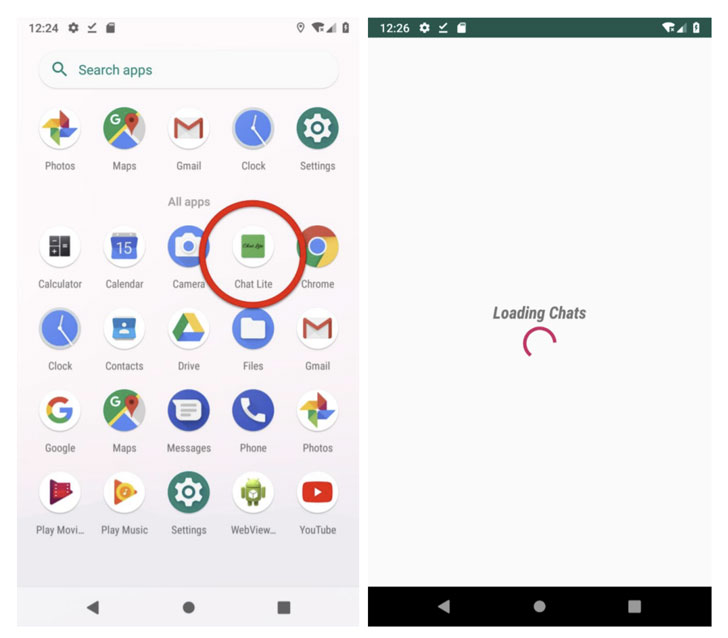
The messages originated from a WhatsApp account associated with
an Indian phone number that’s registered in the state of Jammu and
Kashmir. Once installed, the malicious software — which takes the
form of an app named “ChatLite” — grants the adversary permissions
to access the camera and microphone, gather photos and files stored
on the device, and even grab WhatsApp messages as they are being
sent and received.
But when the aforementioned attempt failed, the attackers
switched to an alternate infection chain in which an email sent
from a Gmail account contained a malware-laced Microsoft Word
document that leveraged a now-patched remote code execution
vulnerability (CVE-2017-0199[3]) to drop a full-fledged
Windows spying tool known as the YTY framework that grants complete
access to the victim’s machine.
“The spyware can be used to steal files from the infected
computer and any connected USB drives, record keystrokes, take
regular screenshots of the computer, and download additional
spyware components,” the researchers said.
Although Innefu Labs has not been directly implicated in the
incident, Amnesty International said it discovered a domain
(“server.authshieldserver.com”) that pointed to an IP address
(122.160.158[.]3) used by a Delhi- based company named Innefu Labs.
In a statement shared with the non-governmental organization,
Innefu Labs denied any connection to the Donot Team APT, adding
“they are not aware of any use of their IP address for the alleged
activities.”
We have reached out to the company for further comment, and we
will update the story if we hear back.
“The worrying trend of private companies actively performing
unlawful digital surveillance increases the scope for abuse while
reducing avenues for domestic legal redress, regulation, and
judicial control,” Amnesty said. “The nature of cross-border
commercial cyber surveillance where the surveillance targets, the
operators, the end customer, and the attack infrastructure can all
be located in different jurisdictions creates significant
impediments to achieving remediation and redress for human rights
abuses.”
References
- ^
Donot
Team (malpedia.caad.fkie.fraunhofer.de) - ^
said
(www.amnesty.org) - ^
CVE-2017-0199
(msrc.microsoft.com)