I recently hopped on the Lookout podcast[1] to talk about virtual
private networks (VPNs) and how they’ve been extended beyond their
original use case of connecting remote laptops to your corporate
network. Even in this new world where people are using personal
devices and cloud apps, VPN continues to be the go-to solution for
remote access and cloud access. After my conversation with Hank
Schless, I was inspired to put some additional thoughts about VPN
on paper.
When most organizations were forced to shift to remote work last
year, they needed a quick-fix solution that would enable their
remote employees to access work resources securely. For many, this
solution came in the form of VPNs. However, VPNs were not designed
for the bring your own device (BYOD) and cloud app use cases.
While VPNs are able to provide remote access, it may come as a
surprise that they fall short when it comes to security. This is
because VPNs were built for when only a small portion of your
workforce wanted to work from home. They also place too much trust
on the device and the user. But now, as work from anywhere
continues, it is important to rethink how to provide access for
your entire organization in a secure manner.
What are the challenges of a remote-first
workforce?
When they first debuted twenty years ago, VPNs were the de-facto
method for connecting remote workers to an organization’s data
center when laptops became common. Back then, computers still used
modems and services like iPass for connectivity. A VPN ran over top
of services like iPass to create a “private network” and keep the
transmission secure.
But since then, the technological landscape has changed
dramatically. In several ways, they were built to solve yesterday’s
problems.
Now, the widespread adoption of cloud applications means the way
we store and access work data is completely different. On any given
day, I’ll connect to an internal development system, access
documents on Google Workspace, send Slack messages to coworkers and
use Zoom to attend meetings. I can perform all of these equally
easily on my smartphone and my laptop.
Many Lookout customers may have a similar experience that also
includes accessing applications on AWS or Azure, such as SAP
S/4HANA. As we work remotely, we’ve become accustomed to seamlessly
accessing what we need wherever it is and to work from any device
of our choosing.
Another significant challenge brought on by this new environment
is that organizations do not have the required visibility into
their complex IT environments.
Unlike back in the day, where you’d only be using work-issued
devices on company-managed networks, employees are accessing work
resources using devices, networks and software that your IT team
has no control over or may even be unaware of. This has
significantly increased the attack surface of your
organization.
Why are VPNs inadequate for the modern work
environment?
One of the biggest issues with VPNs is that they provide full
network access to whoever and whatever is connected. And it’s not
just the device connected, everything that’s on that device’s
network is also given access. So whether it’s a piece of malware,
or a compromised account, there’s nothing to stop them from moving
laterally across your infrastructure and causing harm.
VPNs also have a bad track record when it comes to user
experience. When direct access to the cloud is available
everywhere, expecting your employees to first sign into a VPN to go
to these cloud applications puts a road bump into their workflows.
Think of it like forcing someone to travel from Boston to New York
City via Los Angeles — inefficient. If you’ve ever experienced slow
page loading times or snail-paced downloads while on a VPN, then it
is likely due to your traffic being forced to take an inefficient
route.
What’s the alternative?
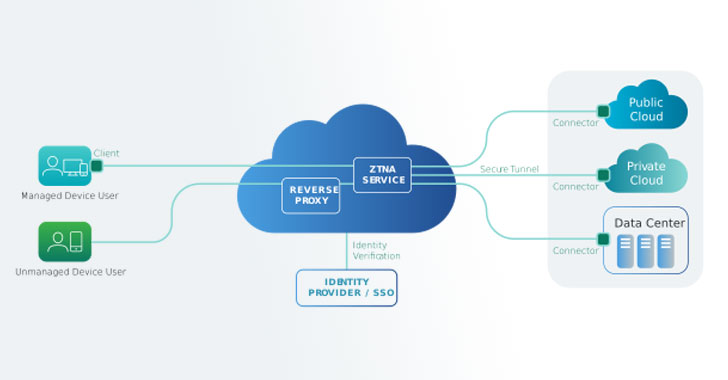
To address these new problems and for the reasons discussed
above, VPNs don’t cut it when it comes to giving your remote
workers secure access to what they need. Secure access technologies
like Zero Trust network access (ZTNA) or cloud access security
broker (CASB) pick up where VPNs leave off.
These secure access service edge (SASE) technologies give
granular access to only the applications and data that your workers
need while continuously monitoring user and device behavior to
adjust access based on risk dynamically. This means that the risk
of lateral movement is dramatically reduced, the connectivity
between the user and the app is efficient, and the security of the
connection goes well beyond encrypting traffic between two
points.
ZTNA provides seamless connection to your apps without
putting your data at risk
After all these years of connecting your workers to your
organization, they deserve their praise where it’s due. But the
problems they were made to address back then are no longer
relevant. Your organization is now facing the challenge of enabling
your workers with the freedom and flexibility to work with
applications in the cloud from anywhere while safeguarding your
data. Moving away from technology like VPNs to next-generation
alternatives like ZTNA is a good start.
Learn how you can augment your VPN[2] deployment and safeguard
your organization by checking out the Lookout Secure Access Service
Edge[3] solution.
Note — This article is written and contributed by Sundaram
Lakshmanan, CTO of SASE Products.
References
- ^
Lookout
podcast (www.lookout.com) - ^
how you
can augment your VPN (www.lookout.com) - ^
Lookout
Secure Access Service Edge
(www.lookout.com)
Read more https://thehackernews.com/2022/01/ztnas-address-requirements-vpns-cannot.html