A broad range of threat actors, including Fancy Bear,
Ghostwriter, and Mustang Panda, have launched phishing campaigns
against Ukraine, Poland, and other European entities amid Russia’s
invasion of Ukraine.
Google’s Threat Analysis Group (TAG) said it took down two
Blogspot domains that were used by the nation-state group FancyBear
(aka APT28) – which is attributed to Russia’s GRU military
intelligence – as a landing page for its social engineering
attacks.
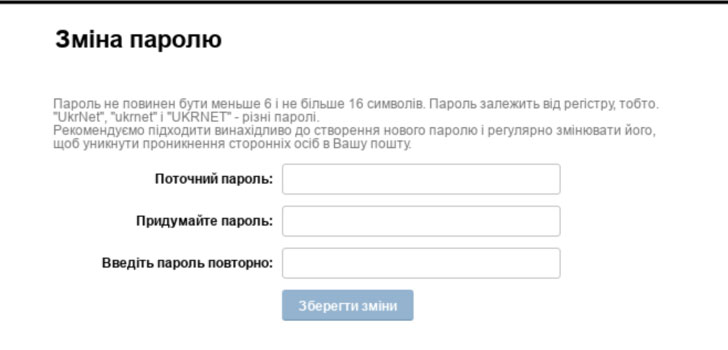
The disclosure comes close on the heels of an advisory from the
Computer Emergency Response Team of Ukraine (CERT-UA) warning[1]
of phishing campaigns targeting Ukr.net users that involve sending
messages from compromised accounts containing links to
attacker-controlled credential harvesting pages.
Another cluster of threat activity concerns webmail users of
Ukr.net, Yandex.ru, wp.pl, rambler.ru, meta.ua, and i.ua, who have
been at the receiving end of phishing attacks by a Belarusian
threat actor tracked as Ghostwriter (aka UNC1151).
The hacking group also “conducted credential phishing campaigns
over the past week against Polish and Ukrainian government and
military organizations,” Shane Huntley, director of Google TAG,
said[2]
in a report.
But it’s not just Russia and Belarus who have set their sights
on Ukraine and Europe. Included in the mix is a China-based threat
actor known as Mustang Panda[3]
(aka TA416 or RedDelta) attempting to plant malware in “targeted
European entities with lures related to the Ukrainian
invasion.”
The findings were also separately corroborated by enterprise
security firm Proofpoint, which detailed[4]
a multi-year TA416 campaign against diplomatic entities in Europe
starting in early November 2021, counting an “individual involved
in refugee and migrant services” on February 28, 2022.
The infection sequence entailed embedding a malicious URL in a
phishing message using a compromised email address of a diplomat
from a European NATO country, which, when clicked, delivered an
archive file incorporating a dropper that, in turn, downloaded a
decoy document to retrieve the final-stage PlugX malware.
The disclosures come as a deluge of distributed
denial-of-service (DDoS) attacks that have hit numerous Ukraine
sites, such as those associated with the Ministry of Defense,
Foreign Affairs, Internal Affairs, and services like Liveuamap.
“Russian hackers keep on attacking Ukrainian information
resources nonstop,” the State Service of Special Communications and
Information Protection of Ukraine (SSSCIP) said[5]
in a tweet over the weekend.
“The most powerful [DDoS] attacks exceeded 100 Gbps at their
peak. Despite all the involved enemy’s resources, the sites of the
central governmental bodies are available.”
In a related development, the Anonymous hacking collective
claimed[6]
that it took down the website of the Federal Security Service of
Russia and that it interrupted the live feeds for several Russian
TV channels and streaming services like Wink, Ivi, Russia 24,
Channel One, and Moscow 24 to broadcast war footage from
Ukraine.
The wave of counterattacks against Russia has been galvanized[7]
by the formation of an IT Army, a crowdsourced Ukrainian government
initiative that’s relying on digital warfare to disrupt Russian
government and military targets.
The development also follows Russia’s decision to ban Facebook
and throttle other widely-used social media platforms in the
country just as technology companies from the U.S. have moved to
sever ties with Russia, effectively creating an iron curtain[8] and curtailing online
access.
References
Read more https://thehackernews.com/2022/03/google-russian-hackers-target.html