Back in 2018, Palo Alto Networks CTO and co-founder Nir Zuk
coined a new term to describe the way that businesses needed to
approach cybersecurity in the years to come. That term, of course,
was extended detection and response (XDR). It described a unified
cybersecurity infrastructure that brought endpoint threat
detection, network analysis and visibility (NAV), access
management, and more under a single roof to find and neutralize
digital threats in real-time.
And Zuk’s vision of XDR proved prophetic. In the years since he
coined the phrase, platforms leveraging the XDR model have emerged
as the de-facto leaders of the business cybersecurity industry. But
their scale and complexity put them in a product class that’s just
out of reach for some enterprises.
Fortunately, the open-source community — as it often does — has
filled the XDR void with an affordable product — because it’s
totally free. It’s called Wazuh[1], and it provides
enterprises the tools they need to build a customized XDR solution
that meets their cybersecurity and budgetary needs at the same
time. Here’s how.
The Key Features of an XDR Platform
Although the varied implementations of XDR solutions come with
varying feature sets, most XDR platforms have a few major features
in common. They include:
Data Analytics and Detection Functionality
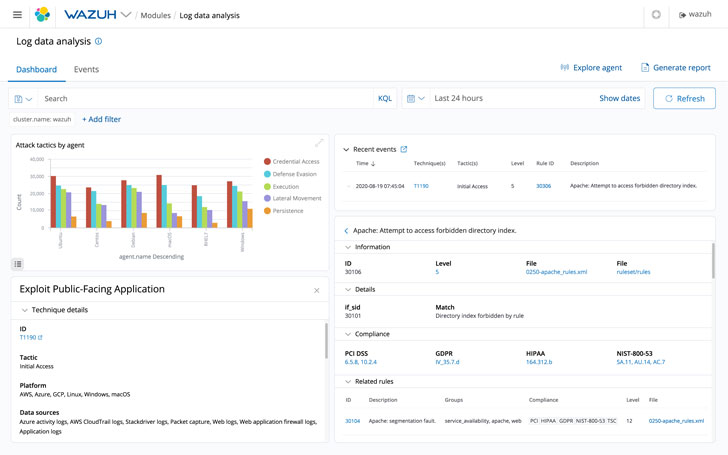
Much of the threat detection offered by XDR solutions come in
the form of data analytics. By analyzing the logs and performance
of major systems, it’s often possible to spot abnormal activity or
threats. To facilitate this, XDR platforms typically perform
analysis of both external and internal traffic, compare performance
and log data against known threat profiles, and employ machine
learning techniques to detect emerging threat patterns such as
those of zero-day attacks.
Threat Investigation and Active Response
XDR platforms don’t only provide businesses with a way to spot
potential threats. They also provide tools to help IT specialists
investigate those threats and deploy various countermeasures to
neutralize them using active responses. To make that possible, most
XDR platforms provide a centralized alert system that can group
related log alerts from multiple systems into a single UI. That UI
can also help administrators respond to alerts by orchestrating
responses across a variety of endpoints. Using that functionality,
admins can update enterprise-wide security policies in response to
a detected attack on a single endpoint.
Scalability and Evolutionary Capability
Last but not least, XDR platforms make it easy for businesses to
integrate new systems, technologies, and endpoints to keep them
protected. That means they’re built for scalability and
interoperability with a wide variety of other vendor-specific
technology products. In that way, they’re a relatively future-proof
solution that grows with a business over time. But they also
include machine learning functionalities that help their defensive
capabilities adapt to a given technology environment and improve as
they work.
How Wazuh Delivers XDR Functionality
The brilliance of the Wazuh approach to XDR is that it can
readily integrate with a variety of other open-source security
tools. That means businesses that use it can adapt the system to
serve their specific needs without any complex and expensive
licensing agreements getting in the way. For example, PDQ Deploy[2]
to install software and patches on workstations, AbuseIPDB[3]
to detect malicious IP addresses involved in spamming, hacking
attempts and DDoS attacks, and URLhaus[4]
to detect malicious URLs used for malware distribution.
But the core of the Wazuh XDR approach comes in the form of its
multi-platform monitoring agent[5]. It’s compatible with
most devices via its high-level OS support. That means businesses
can deploy it to begin collecting endpoint data with very little
customization needed. Those agents stream system information back
to the Wazuh server, where it performs a variety of anomaly and malware detection[6] routines on it. In that
way, administrators gain instant visibility into endpoint security
through the server’s centralized interface. But that’s not all.
Through integrations with tools like Suricata and OwlH,
administrators get powerful network intrusion detection and
visualization functions. That gives them the same kind of
situational awareness that other major XDR platforms offer, but
without the associated price tag. And the system can even execute
automated threat response[7] routines based on
network and endpoint data — taking action to stop attacks in their
tracks with little to no manual intervention required.
And because Wazuh is an open-source solution, it offers the
ultimate in scalability and evolutionary capabilities. It can
already integrate with security-focused machine learning solutions
like Amazon’s Macie[8], giving it stored data
surveillance capabilities. But the possibility for additional
integrations is endless. That means businesses that opt to use
Wazuh as an XDR solution won’t be locked into a particular machine
learning system, and they can tailor the system’s evolutionary
capability to their own needs.
The Critical Takeaways
There’s little doubt that today’s major XDR solutions represent
the current state-of-the-art in business-grade cybersecurity. And
their all-encompassing approach to defending digital business
infrastructure likely represents the future of it, too. That’s
because they acknowledge the reality that protecting business data
and assets means having true transparency into endpoint operations
and allowing for infrastructure-wide responses to threats at a
moment’s notice.
Although XDR will not penetrate the cybersecurity market for a
few years due to scaling issues, the fact that an open source
solution like Wazuh exists is no small feat. It holds the power to
provide meaningful and effective XDR functionality to organizations
of all sizes. And it’s also flexible enough to adapt to changing
business needs and new technology integrations. It’s no
exaggeration to say it’s a true game-changer in the cybersecurity
space as it exists today.
And best of all — it’s free and growing at a rapid pace with the
support of the open-source community. All businesses have to do to
take advantage of it is to invest in some modest hardware to serve
as a control hub, or can simply use Wazuh Cloud[9]. They can use Wazuh to
create a bespoke XDR system that’s on par with anything now
available on the commercial market.
And even better, they’ll end up with a system that’s endlessly
customizable and upgradeable — meaning it’s a system that
businesses can invest in without fear that it will someday be
outmoded and obsolete.
There aren’t many solutions in the world of cybersecurity that
can make such a claim — making Wazuh a force to be reckoned with in
the XDR market writ large.
References
- ^
Wazuh
(wazuh.com) - ^
PDQ
Deploy (wazuh.com) - ^
AbuseIPDB
(wazuh.com) - ^
URLhaus
(wazuh.com) - ^
monitoring agent
(documentation.wazuh.com) - ^
anomaly
and malware detection
(documentation.wazuh.com) - ^
automated threat response
(documentation.wazuh.com) - ^
Amazon’s
Macie (documentation.wazuh.com) - ^
Wazuh Cloud
(wazuh.com)
Read more https://thehackernews.com/2022/03/wazuh-offers-xdr-functionality-at-price.html