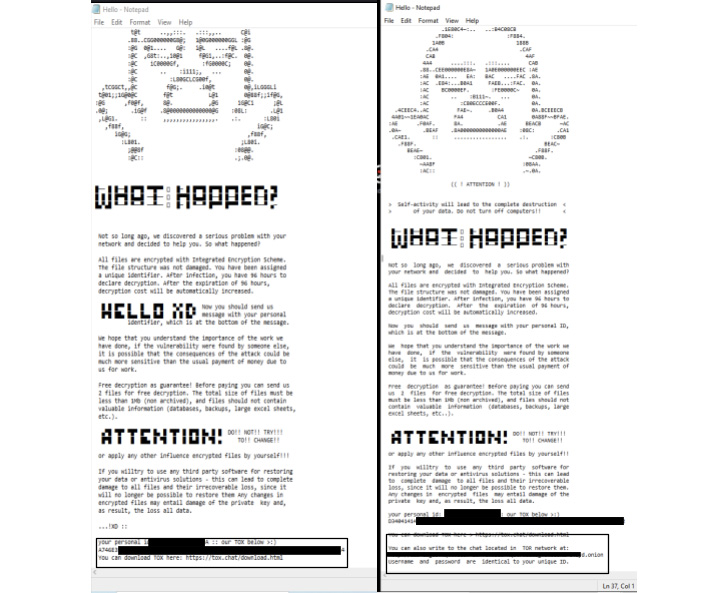
Windows and Linux systems are being targeted by a ransomware
variant called HelloXD, with the infections also involving the
deployment of a backdoor to facilitate persistent remote access to
infected hosts.
“Unlike other ransomware groups, this ransomware family doesn’t
have an active leak site; instead it prefers to direct the impacted
victim to negotiations through Tox chat[1]
and onion-based messenger instances,” Daniel Bunce and Doel Santos,
security researchers from Palo Alto Networks Unit 42, said[2]
in a new write-up.
HelloXD[3]
surfaced in the wild on November 30, 2021, and is based off leaked
code from Babuk, which was published[4]
on a Russian-language cybercrime forum in September 2021.
The ransomware family is no exception to the norm in that the
operators follow the tried-and-tested approach of double extortion[5]
to demand cryptocurrency payments by exfiltrating a victim’s
sensitive data in addition to encrypting it and threatening to
publicize the information.
The implant in question, named MicroBackdoor[6], is an open-source
malware that’s used for command-and-control (C2) communications,
with its developer Dmytro Oleksiuk calling[7] it a “really
minimalistic thing with all of the basic features in less than
5,000 lines of code.”
Notably, different variants of the implant were adopted[8]
by the Belarusian threat actor dubbed Ghostwriter (aka UNC1151) in
its cyber operations[9]
against Ukrainian state organizations in March 2022.
MicroBackdoor’s features allow an attacker to browse the file
system, upload and download files, execute commands, and erase
evidence of its presence from the compromise machines. It’s
suspected that the deployment of the backdoor is carried out to
“monitor the progress of the ransomware.”
Unit 42 said it linked the likely Russian developer behind
HelloXD — who goes by the online aliases x4k, L4ckyguy, unKn0wn,
unk0w, _unkn0wn, and x4kme — to further malicious activities such
as selling proof-of-concept (PoC) exploits and custom Kali Linux
distributions by piecing together the actor’s digital trail.
“x4k has a very solid online presence, which has enabled us to
uncover much of his activity in these last two years,” the
researchers said. “This threat actor has done little to hide
malicious activity, and is probably going to continue this
behavior.”
The findings come as a new study from IBM X-Force revealed[10] that the average
duration of an enterprise ransomware attack — i.e., the time
between initial access and ransomware deployment — reduced 94.34%
between 2019 and 2021 from over two months to a mere 3.85 days.
The increased speed and efficiency trends in the
ransomware-as-a-service (RaaS) ecosystem has been attributed to the
pivotal role played by initial access brokers (IABs[11]) in obtaining access to victim
networks[12] and then selling the
access to affiliates, who, in turn, abuse the foothold to deploy
ransomware payloads.
“Purchasing access may significantly reduce the amount of time
it takes ransomware operators to conduct an attack by enabling
reconnaissance of systems and the identification of key data
earlier and with greater ease,” Intel 471 said[13] in a report
highlighting the close working relationships between IABs and
ransomware crews.
“Additionally, as relationships strengthen, ransomware groups
may identify a victim who they wish to target and the access
merchant could provide them the access once it is available.”
References
- ^
Tox
chat (en.wikipedia.org) - ^
said
(unit42.paloaltonetworks.com) - ^
HelloXD
(twitter.com) - ^
published
(intel471.com) - ^
double
extortion (www.trendmicro.com) - ^
MicroBackdoor
(malpedia.caad.fkie.fraunhofer.de) - ^
calling
(github.com) - ^
adopted
(thehackernews.com) - ^
cyber
operations (inquest.net) - ^
revealed
(securityintelligence.com) - ^
IABs
(thehackernews.com) - ^
obtaining access to victim
networks (thehackernews.com) - ^
said
(intel471.com)
Read more https://thehackernews.com/2022/06/hello-xd-ransomware-installing-backdoor.html