A technically sophisticated threat actor known as
SeaFlower has been targeting Android and iOS users
as part of an extensive campaign that mimics official
cryptocurrency wallet websites intending to distribute backdoored
apps that drain victims’ funds.
Said to be first discovered in March 2022, the cluster of
activity “hint[s] to a strong relationship with a Chinese-speaking
entity yet to be uncovered,” based on the macOS usernames, source
code comments in the backdoor code, and its abuse of Alibaba’s
Content Delivery Network (CDN).
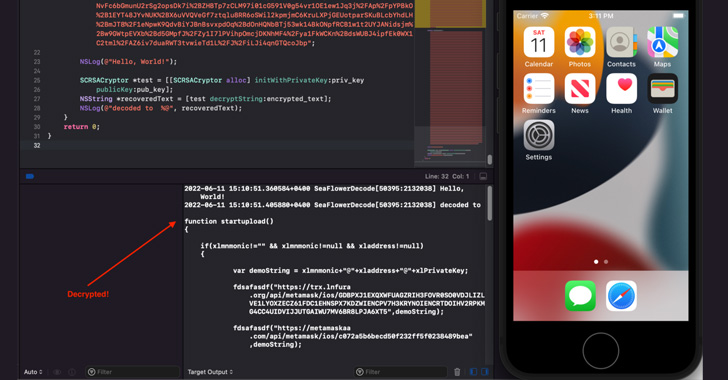
“As of today, the main current objective of SeaFlower is to
modify Web3 wallets with backdoor code that ultimately exfiltrates
the seed phrase,” Confiant’s Taha Karim said[1]
in a technical deep-dive of the campaign.
Targeted apps include Android and iOS versions of Coinbase
Wallet, MetaMask, TokenPocket, and imToken.
SeaFlower’s modus operandi involves setting up cloned websites
that act as a conduit to download trojanized versions of the wallet
apps that are virtually unchanged from their original counterparts
except for the addition of new code designed to exfiltrate the seed
phrase to a remote domain.
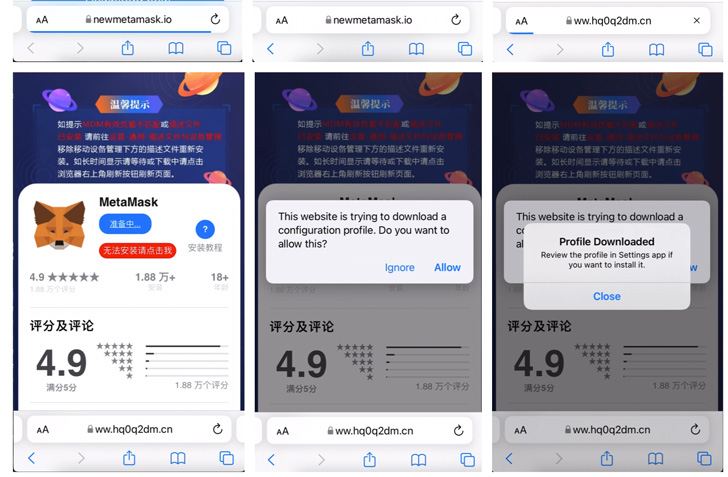
The malicious activity is also engineered to target iOS users by
means of provisioning profiles[2]
that enable the apps to be sideloaded onto the devices.
As for how users stumble upon these websites offering fraudulent
wallets, the attack leverages SEO poisoning techniques on Chinese
search engines like Baidu and Sogou so that searches for terms such
as “download MetaMask iOS” are rigged to surface the drive-by
download pages on top of the search results page.
If anything, the disclosure once again highlights how threat
actors are increasingly setting their sights on popular Web3
platforms[3] in an attempt to plunder
sensitive data and deceptively transfer virtual funds.
References
- ^
said
(blog.confiant.com) - ^
provisioning profiles
(developer.apple.com) - ^
setting
their sights on popular Web3 platforms
(thehackernews.com)
Read more https://thehackernews.com/2022/06/chinese-hackers-distribute-backdoored.html