The operators of the Hive ransomware-as-a-service (RaaS) scheme
have overhauled their file-encrypting software to fully migrate to
Rust and adopt a more sophisticated encryption method.
“With its latest variant carrying several major upgrades, Hive
also proves it’s one of the fastest evolving ransomware families,
exemplifying the continuously changing ransomware ecosystem,”
Microsoft Threat Intelligence Center (MSTIC) said[1]
in a report on Tuesday.
Hive[2], which was first
observed in June 2021, has emerged as one of the most prolific RaaS
groups, accounting[3]
for 17 attacks in the month of May 2022 alone, alongside Black Basta and Conti[4].
The shift from GoLang to Rust makes Hive the second ransomware
strain after BlackCat[5]
to be written in the programming language, enabling the malware to
gain additional benefits such as memory safety and deeper control
over low-level resources as well as make use of a wide range of
cryptographic libraries.
What it also affords is the ability to render the malware
resistant to reverse engineering, making it more evasive.
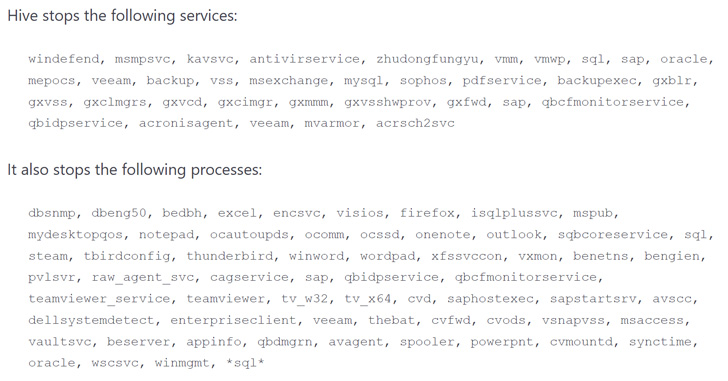
Furthermore, it comes with features to stop services and processes
associated with security solutions that may stop it in its
tracks.
Hive is no different from other ransomware families in that it
deletes backups to prevent recovery, but what’s changed
significantly in the new Rust-based variant is its approach to file
encryption.
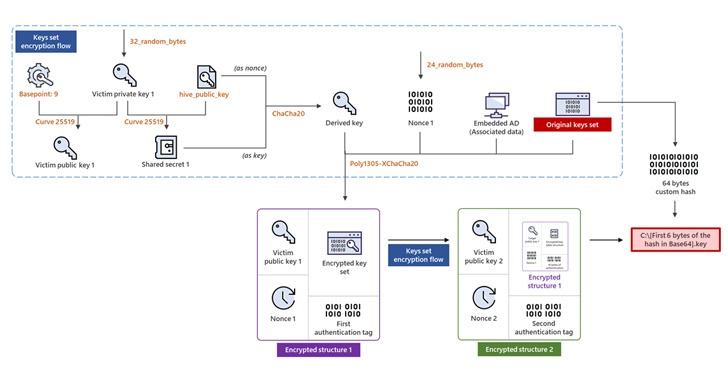
“Instead of embedding an encrypted key in each file that it
encrypts, it generates two sets of keys in memory, uses them to
encrypt files, and then encrypts and writes the sets to the root of
the drive it encrypts, both with .key extension,” MSTIC
explained.
To determine which of the two keys is used for locking a
specific file, an encrypted file is renamed to include the file
name containing the key that’s then followed by an underscore and a
Base64-encoded string (e.g., “C:\myphoto.jpg.l0Zn68cb _
-B82BhIaGhI8”) that points to two different locations in the
corresponding .key file.
The findings come as the threat actor behind the lesser-known
AstraLocker[6]
ransomware ceased operations and released a decryption tool as part
of a shift to crytojacking, Bleeping Computer reported[7]
this week.
But in an indication that the cybercriminal landscape is in
constant flux, cybersecurity researchers have discovered[8]
a new ransomware family[9]
called RedAlert (aka N13V) that’s capable of targeting both Windows
and Linux VMWare ESXi servers.
References
- ^
said
(www.microsoft.com) - ^
Hive
(thehackernews.com) - ^
accounting
(www.mynewsdesk.com) - ^
Black
Basta and Conti (thehackernews.com) - ^
BlackCat
(thehackernews.com) - ^
AstraLocker
(blog.reversinglabs.com) - ^
reported
(www.bleepingcomputer.com) - ^
discovered
(twitter.com) - ^
ransomware family
(www.bleepingcomputer.com)
Read more https://thehackernews.com/2022/07/hive-ransomware-upgrades-to-rust-for.html