Thai activists involved in the country’s pro-democracy protests
have had their smartphones infected with the infamous Pegasus
government-sponsored spyware.
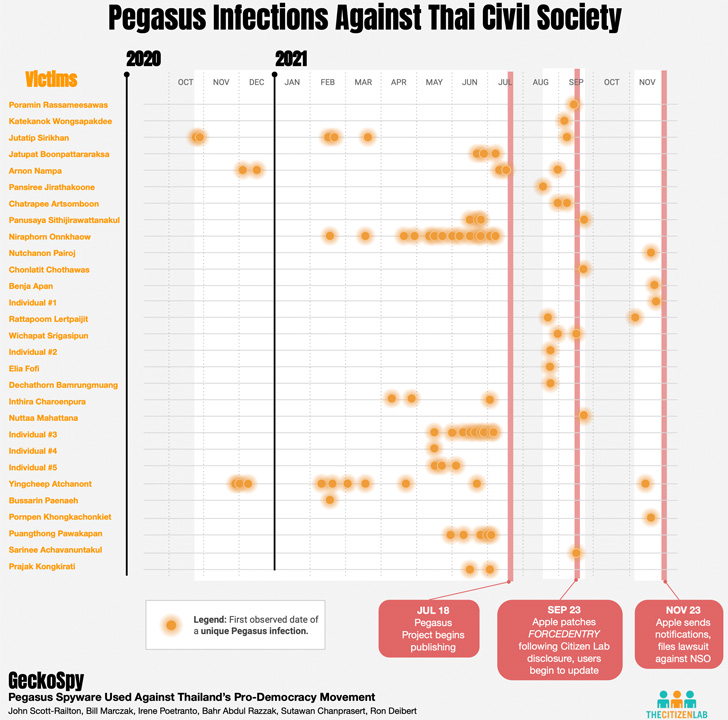
At least 30 individuals, spanning activists, academics, lawyers,
and NGO workers, are believed to have been infected between October
2020 and November 2021, many of whom have been previously detained,
arrested and imprisoned for their political activities or criticism
of the government.
“The timing of the infections is highly relevant to specific
political events in Thailand, as well as specific actions by the
Thai justice system,” the Citizen Lab said[1]
in a Sunday report. “In many cases, for example, infections
occurred slightly before protests and other political activities by
the victims.”
The findings are the result of threat notifications[2]
sent by Apple last November to alert users it believes have been
targeted by state-sponsored attackers.
The attacks entailed the use of two zero-click exploits —
KISMET[3]
and FORCEDENTRY[4]
— to compromise the victims’ phones and deploy Pegasus, spyware
that’s capable of intercepting calls and texts as well as amassing
other information stored in a phone. It can also turn it into a
remote listening device.
Google Project Zero researchers have described[5]
the iOS zero-click attacks as “a weapon against which there is no
defense,” adding “there is no way to prevent exploitation by a
zero-click exploit.”
The earliest cases of infections using the KISMET exploit
occurred in October 2020 against out-of-date iPhone, with the
FORCEDENTRY exploit deployed against Thai iPhones starting in
February 2021 running iOS versions 14.4, 14.6, and 14.7.1.
It’s worth pointing out that Apple fixed KISMET in iOS 14 with
what’s called the BlastDoor[6]
sandbox system. FORCEDENTRY was patched[7]
by the tech giant in September 2021 with iOS 14.8.
Apple, earlier this month, also announced[8]
that it’s architecting a new security measure called Lockdown Mode
to counteract mercenary spyware and safeguard high-risk users
against “highly targeted cyberattacks.”
Citizen Lab noted that there is currently at least one Pegasus
customer active in Thailand, although it’s not immediately known if
it’s connected to a specific government agency.
NSO has long claimed that its spyware is used by government
clients to tackle serious crime, but evidence gathered so far has
pointed to repeated instances[9]
of abuse of the surveillance tool to snoop on members of the civil
society. The Israeli firm has since been blocklisted[10] by the U.S.
“The hacking points to a sophisticated understanding of
non-public elements of the Thai activist community, including
funding and roles of specific individuals,” Citizen Lab researchers
said.
“This finding is part of a broader trend seen in Thailand where
the government has been engaged in increased efforts to monitor or
control information since the 2014 coup.”
The development also comes as Amnesty International reiterated[11] that the lack of a
global moratorium on the sale of spyware is enabling the
surveillance industry to function unchecked.
“We can now officially add Thailand to the growing list of
countries where people peacefully calling for change, expressing an
opinion, or discussing government policies may trigger invasive
surveillance with a profound toll on an individual’s freedom of
expression, privacy, and sense of security,” said[12] Amnesty International’s
Etienne Maynier.
References
- ^
said
(citizenlab.ca) - ^
threat
notifications (thehackernews.com) - ^
KISMET
(thehackernews.com) - ^
FORCEDENTRY
(thehackernews.com) - ^
described
(googleprojectzero.blogspot.com) - ^
BlastDoor
(thehackernews.com) - ^
patched
(thehackernews.com) - ^
announced
(thehackernews.com) - ^
repeated
instances (thehackernews.com) - ^
blocklisted
(thehackernews.com) - ^
reiterated
(www.amnesty.org) - ^
said
(www.amnesty.org)
Read more https://thehackernews.com/2022/07/pegasus-spyware-used-to-hack-devices-of.html