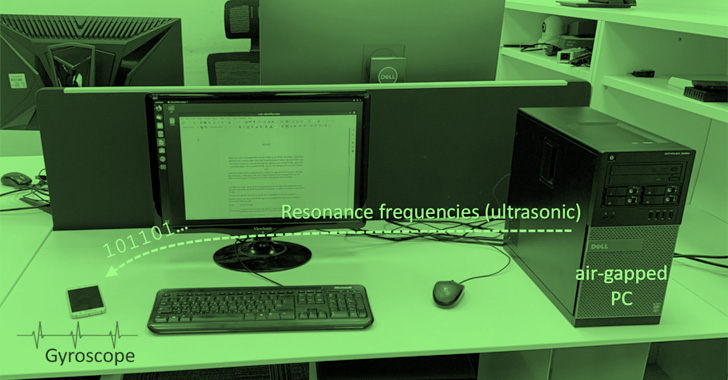
A novel data exfiltration technique has been found to leverage a
covert ultrasonic channel to leak sensitive information from
isolated, air-gapped computers to a nearby smartphone that doesn’t
even require a microphone to pick up the sound waves.
Dubbed GAIROSCOPE, the adversarial model is the
latest addition to a long list of acoustic, electromagnetic, optical, and
thermal approaches[1]
devised by Dr. Mordechai Guri, the head of R&D in the Cyber
Security Research Center in the Ben Gurion University of the Negev
in Israel.
“Our malware generates ultrasonic tones in the resonance
frequencies of the MEMS gyroscope[2],” Dr. Guri said in a
new
paper[3] published this week.
“These inaudible frequencies produce tiny mechanical oscillations
within the smartphone’s gyroscope, which can be demodulated into
binary information.”
Air-gapping is seen as an essential security countermeasure[4] that involves isolating
a computer or network and preventing it from establishing an
external connection, effectively creating an impenetrable barrier
between a digital asset and threat actors who try to forge a path
for espionage attacks.
Like other attacks against air-gapped networks, GAIROSCOPE is no
different in that it banks on the ability of an adversary to breach
a target environment via ploys such as infected USB sticks,
watering holes, or supply chain compromises to deliver the
malware.
What’s new this time around is that it also requires infecting
the smartphones of employees working in the victim organization
with a rogue app that, for its part, is deployed by means of attack
vectors like social engineering, malicious ads, or compromised
websites, among others.
In the next phase of the kill chain, the attacker abuses the
established foothold to harvest sensitive data (i.e., encryption
keys, credentials etc.), encodes, and broadcasts the information in
the form of stealthy acoustic sound waves via the machine’s
loudspeaker.
The transmission is then detected by an infected smartphone
that’s in close physical proximity and which listens through the
gyroscope sensor built into the device, following which the data is
demodulated, decoded, and transferred to the attacker via the
Internet over Wi-Fi.
This is made possible due to a phenomenon called ultrasonic
corruption that affects MEMS gyroscopes at resonance
frequencies[5]. “When this inaudible
sound is played near the gyroscope, it creates an internal
disruption to the signal output,” Dr. Guri explained. “The errors
in the output can be used to encode and decode information.”
Experimental results show that the covert channel can be used to
transfer data with bit rates of 1-8 bit/sec at distances of 0 – 600
cm, with the transmitter reaching a distance of 800 cm in narrow
rooms.
Should employees place their mobile phones close to their
workstations on the desk, the method could be used to exchange
data, including short texts, encryption keys, passwords, or
keystrokes.
The data exfiltration method is notable for the fact that it
doesn’t require the malicious app in the receiving smartphone (in
this case, One Plus 7, Samsung Galaxy S9, and Samsung Galaxy S10)
to have microphone access, thus tricking users into approving their
access without suspicion.
The speakers-to-gyroscope covert channel is also advantageous
from an adversarial point of view. Not only are there no visual
cues on Android and iOS when an app uses the gyroscope (like in the
case of location or microphone), the sensor is also accessible from
HTML via standard JavaScript.
This also means that the bad actor doesn’t have to install an
app to achieve the intended goals, and can instead inject backdoor
JavaScript code on a legitimate website that samples the gyroscope,
receives the covert signals, and exfiltrates the information via
the Internet.
Mitigating GAIROSCOPE requires organizations to enforce
separation policies to keep smartphones at least 800 cm away or
more from secured areas, remove loudspeakers and audio drivers from
endpoints, filter out ultrasonic signals using firewalls SilverDog[6] and SoniControl[7], and jam the covert
channel by adding background noises to the acoustic spectrum.
The study arrives a little over a month after Dr. Guri
demonstrated SATAn[8], a mechanism to jump
over air-gaps and extract information by taking advantage of Serial
Advanced Technology Attachment (SATA) cables.
References
- ^
acoustic, electromagnetic, optical, and
thermal approaches (cyber.bgu.ac.il) - ^
MEMS
gyroscope (en.wikipedia.org) - ^
new paper
(arxiv.org) - ^
essential security countermeasure
(thehackernews.com) - ^
resonance frequencies
(en.wikipedia.org) - ^
SilverDog
(github.com) - ^
SoniControl
(github.com) - ^
SATAn
(thehackernews.com)
Read more https://thehackernews.com/2022/08/new-air-gap-attack-uses-mems-gyroscope.html