A nascent information-stealing malware sold and distributed on
underground Russian underground forums has been written in Rust,
signalling a new trend where threat actors are increasingly
adopting exotic programming languages[1] to bypass security
protections, evade analysis, and hamper reverse engineering
efforts.
Dubbed “Ficker Stealer[2],” it’s notable for being
propagated via Trojanized web links and compromised websites,
luring in victims to scam landing pages purportedly offering free
downloads of legitimate paid services[3] like Spotify Music,
YouTube Premium, and other Microsoft Store applications.
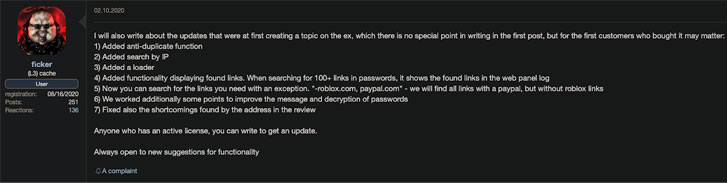
“Ficker is sold and distributed as Malware-as-a-Service (MaaS),
via underground Russian online forums,” BlackBerry’s research and
intelligence team said in a report published today. “Its creator,
whose alias is @ficker, offers several paid packages, with
different levels of subscription fees to use their malicious
program.”
First seen in the wild in August 2020, the Windows-based malware
is used to steal sensitive information, including login
credentials, credit card information, cryptocurrency wallets, and
browser information, in addition to functioning as a tool to grab
sensitive files from the compromised machine, and act as a
downloader to download and execute additional second-stage
malware.
Additionally, Ficker is known to be delivered through spam
campaigns, which involve sending targeted phishing emails with
weaponized macro-based Excel document attachments that, when
opened, drops the Hancitor[4]
loader, which then injects the final payload using a technique
called process hollowing[5]
to avoid detection and mask its activities.
In the months that followed since its discovery, the digital
threat has been found leveraging DocuSign-themed lures to install a
Windows binary[6]
from an attacker-controlled server. CyberArk, in an analysis[7]
of the Ficker malware last month, noted its heavily obfuscated
nature and Rust roots, making the analysis more difficult, if not
prohibitive.
“Once the fake DocuSign document is opened and its malicious
macro code is allowed to run, Hancitor will often reach out to its
command-and-control (C2) infrastructure to receive a malicious URL
containing a sample of Ficker to download,” BlackBerry researchers said[8].
Aside from relying on obfuscation techniques, the malware also
incorporates other anti-analysis checks that prevent it from
running on virtualized environments and on victim machines located
in Armenia, Azerbaijan, Belarus, Kazakhstan, Russia, and
Uzbekistan. Also worthy of particular note is that, unlike
traditional information stealers, Ficker is designed to execute the
commands and exfiltrate the information directly to the operators
instead of writing the stolen data to disk.
“The malware also has screen-capturing abilities, which allow
the malware’s operator to remotely capture an image of the victim’s
screen. The malware also enables file-grabbing and additional
downloading capabilities once connection to its C2 is established,”
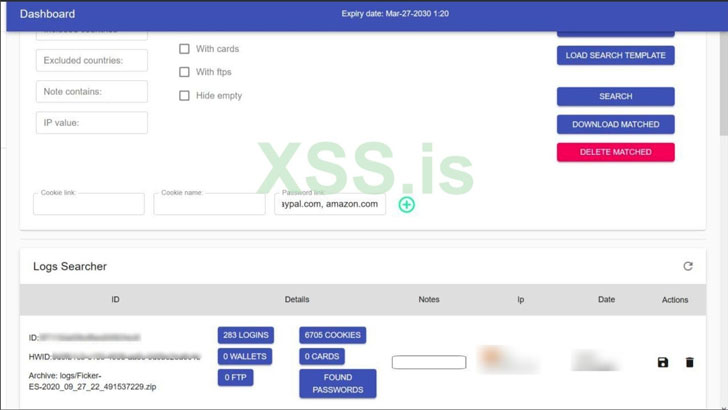
the researchers said. “Once information is sent back to Ficker’s
C2, the malware owner can access and search for all exfiltrated
data.”
References
- ^
exotic
programming languages (thehackernews.com) - ^
Ficker
Stealer (malpedia.caad.fkie.fraunhofer.de) - ^
legitimate paid services
(twitter.com) - ^
Hancitor
(malpedia.caad.fkie.fraunhofer.de) - ^
process
hollowing (attack.mitre.org) - ^
Windows
binary (blogs.quickheal.com) - ^
analysis
(www.cyberark.com) - ^
researchers said
(blogs.blackberry.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/15nGpY5992E/experts-shed-light-on-new-russian.html