Apple on Monday released a security update for iOS and iPad to
address a critical vulnerability that it says is being exploited in
the wild, making it the 17th zero-day flaw the company has
addressed in its products since the start of the year.’
The weakness, assigned the identifier CVE-2021-30883[1], concerns a memory
corruption issue in the “IOMobileFrameBuffer” component that could
allow an application to execute arbitrary code with kernel
privileges. Crediting an anonymous researcher for reporting the
vulnerability, Apple said it’s “aware of a report that this issue
may have been actively exploited.”
Technical specifics about the flaw and the nature of the attacks
remain unavailable as yet, as is the identity of the threat actor,
so as to allow a majority of the users to apply the patch and
prevent other adversaries from weaponizing the vulnerability. The
iPhone maker said it addressed the issue with improved memory
handling.
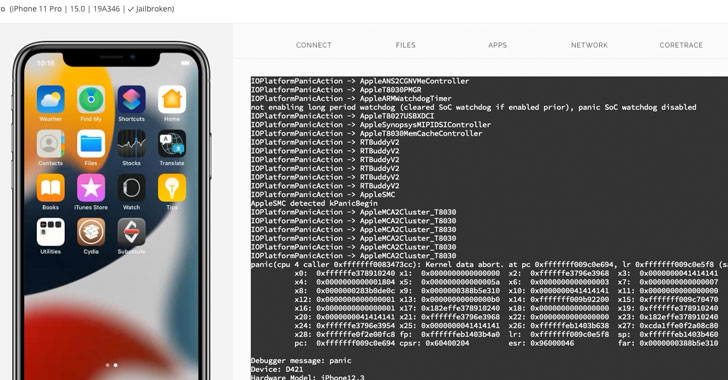
Security researcher Saar Amar shared[2]
additional details, and a proof-of-concept (PoC) exploit, noting
that “this attack surface is highly interesting because it’s
accessible from the app sandbox (so it’s great for jailbreaks) and
many other processes, making it a good candidate for LPEs exploits
in chains.”
CVE-2021-30883 is also the second zero-day impacting
IOMobileFrameBuffer after Apple addressed a similar, anonymously
reported memory corruption issue (CVE-2021-30807) in July 2021,
raising the possibility that the two flaws could be related. With
the latest fix, the company has resolved a record 17 zero-days to
date in 2021 alone —
- CVE-2021-1782[3] (Kernel) – A malicious
application may be able to elevate privileges - CVE-2021-1870[4] (WebKit) – A remote
attacker may be able to cause arbitrary code execution - CVE-2021-1871[5] (WebKit) – A remote
attacker may be able to cause arbitrary code execution - CVE-2021-1879[6] (WebKit) – Processing
maliciously crafted web content may lead to universal cross-site
scripting - CVE-2021-30657[7] (System Preferences) – A
malicious application may bypass Gatekeeper checks - CVE-2021-30661[8] (WebKit Storage) –
Processing maliciously crafted web content may lead to arbitrary
code execution - CVE-2021-30663[9] (WebKit) – Processing
maliciously crafted web content may lead to arbitrary code
execution - CVE-2021-30665[10] (WebKit) – Processing
maliciously crafted web content may lead to arbitrary code
execution - CVE-2021-30666[11] (WebKit) – Processing
maliciously crafted web content may lead to arbitrary code
execution - CVE-2021-30713[12] (TCC framework) – A
malicious application may be able to bypass Privacy
preferences - CVE-2021-30761[13] (WebKit) – Processing
maliciously crafted web content may lead to arbitrary code
execution - CVE-2021-30762[14] (WebKit) – Processing
maliciously crafted web content may lead to arbitrary code
execution - CVE-2021-30807[15] (IOMobileFrameBuffer) –
An application may be able to execute arbitrary code with kernel
privileges - CVE-2021-30858[16] (WebKit) – Processing
maliciously crafted web content may lead to arbitrary code
execution - CVE-2021-30860[17] (CoreGraphics) –
Processing a maliciously crafted PDF may lead to arbitrary code
execution - CVE-2021-30869[18] (XNU) – A malicious
application may be able to execute arbitrary code with kernel
privileges
Apple iPhone and iPad users are highly recommended to update to
the latest version (iOS 15.0.2 and iPad 15.0.2) to mitigate the
security vulnerability.
References
- ^
CVE-2021-30883
(support.apple.com) - ^
shared
(saaramar.github.io) - ^
CVE-2021-1782
(thehackernews.com) - ^
CVE-2021-1870
(thehackernews.com) - ^
CVE-2021-1871
(thehackernews.com) - ^
CVE-2021-1879
(thehackernews.com) - ^
CVE-2021-30657
(thehackernews.com) - ^
CVE-2021-30661
(thehackernews.com) - ^
CVE-2021-30663
(thehackernews.com) - ^
CVE-2021-30665
(thehackernews.com) - ^
CVE-2021-30666
(thehackernews.com) - ^
CVE-2021-30713
(thehackernews.com) - ^
CVE-2021-30761
(thehackernews.com) - ^
CVE-2021-30762
(thehackernews.com) - ^
CVE-2021-30807
(thehackernews.com) - ^
CVE-2021-30858
(thehackernews.com) - ^
CVE-2021-30860
(thehackernews.com) - ^
CVE-2021-30869
(thehackernews.com)