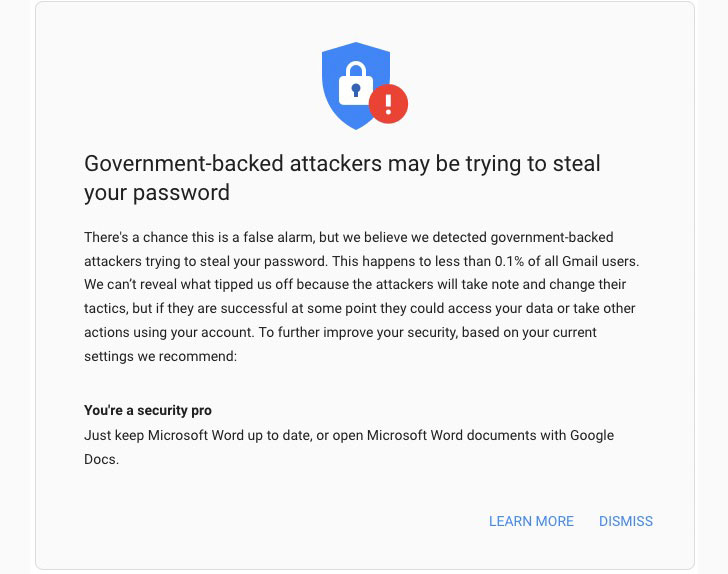
Google’s Threat Analysis Group (TAG) on Thursday said[1]
it’s tracking more than 270 government-backed threat actors from
more than 50 countries, adding it has approximately sent 50,000
alerts of state-sponsored phishing or malware attempts to customers
since the start of 2021.
The warnings mark a 33% increase from 2020, the internet giant
said, with the spike largely stemming[2]
from “blocking an unusually large campaign from a Russian actor
known as APT28 or Fancy Bear.”
Additionally, Google said it disrupted a number of campaigns
mounted by an Iranian state-sponsored attacker group tracked as
APT35[3]
(aka Charming Kitten, Phosphorous, or Newscaster), including a
sophisticated social engineering attack dubbed “Operation
SpoofedScholars” aimed at think tanks, journalists, and professors
with an aim to solicit sensitive information by masquerading as
scholars with the University of London’s School of Oriental and
African Studies (SOAS).
Details of the attack were first publicly documented[4]
by enterprise security firm Proofpoint in July 2021.
Other past attacks involved the use of a spyware-infested VPN app[5] uploaded to the Google
Play Store that, when installed, could be leveraged to siphon
sensitive information such as call logs, text messages, contacts,
and location data from the infected devices. Furthermore, an
unusual tactic adopted by APT35 concerned the use of Telegram to
notify the attackers when phishing sites under their control have
been visited in real-time via malicious JavaScript embedded into
the pages.
The threat actor is also said to have impersonated policy officials[6] by sending
“non-malicious first contact email messages” modeled around the
Munich Security and Think-20 (T20) Italy conferences as part of a
phishing campaign to lure high-profile individuals into visiting
rogue websites.
“For years, this group has hijacked accounts, deployed malware,
and used novel techniques to conduct espionage aligned with the
interests of the Iranian government,” Google TAG’s Ajax Bash
said.
References
- ^
said
(blog.google) - ^
stemming
(twitter.com) - ^
APT35
(malpedia.caad.fkie.fraunhofer.de) - ^
publicly
documented (thehackernews.com) - ^
spyware-infested VPN app
(www.virustotal.com) - ^
impersonated policy officials
(blogs.microsoft.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/JgKmNXMlZiI/google-were-tracking-270-state.html