The Chinese-backed Hafnium hacking group has been linked to a
piece of a new malware that’s used to maintain persistence on
compromised Windows environments.
The threat actor is said to have targeted entities in the
telecommunication, internet service provider and data services
sectors from August 2021 to February 2022, expanding from the
initial victimology patterns observed during its attacks exploiting
the then zero-day flaws in Microsoft Exchange Servers[1] in March 2021.
Microsoft Threat Intelligence Center (MSTIC), which dubbed the
defense evasion malware “Tarrask,” characterized
it as a tool that creates “hidden” scheduled tasks on the system.
“Scheduled task abuse is a very common method of persistence and
defense evasion — and an enticing one, at that,” the researchers
said[2].
Hafnium, while most notable for Exchange Server attacks, has
since leveraged unpatched zero-day vulnerabilities as initial
vectors to drop web shells and other malware, including Tarrask,
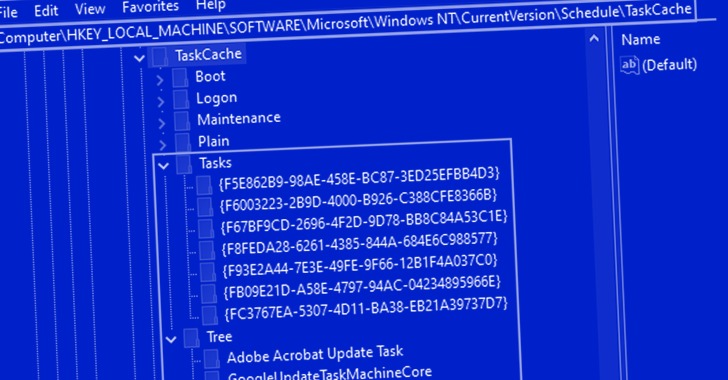
which creates new registry keys within two paths Tree and Tasks
upon the creation of new scheduled tasks –
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows
NT\CurrentVersion\Schedule\TaskCache\Tree\TASK_NAME - HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows
NT\CurrentVersion\Schedule\TaskCache\Tasks\{GUID}
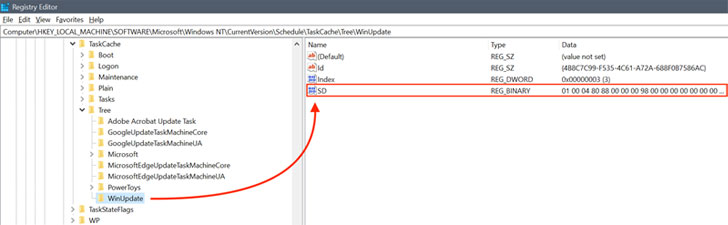
“In this scenario, the threat actor created a scheduled task
named ‘WinUpdate’ via HackTool:Win64/Tarrask in order to
re-establish any dropped connections to their command-and-control
(C&C) infrastructure,” the researchers said.
“This resulted in the creation of the registry keys and values
described in the earlier section, however, the threat actor deleted
the [Security Descriptor] value within the Tree registry path.” A
security descriptor (aka SD) defines access
controls for running the scheduled task.
But by erasing the SD value from the aforementioned Tree
registry path, it effectively leads to the task hidden from the
Windows Task Scheduler or the schtasks[3]
command-line utility, unless manually examined by navigating to the
paths in the Registry Editor.
“The attacks […] signify how the threat actor Hafnium displays
a unique understanding of the Windows subsystem and uses this
expertise to mask activities on targeted endpoints to maintain
persistence on affected systems and hide in plain sight,” the
researchers said.
References
Read more https://thehackernews.com/2022/04/microsoft-exposes-evasive-chinese.html