The Computer Emergency Response Team of Ukraine (CERT-UA) on
Tuesday disclosed[1]
that it thwarted a cyberattack by Sandworm[2], a hacking group
affiliated with Russia’s military intelligence, to sabotage the
operations of an unnamed energy provider in the country.
“The attackers attempted to take down several infrastructure
components of their target, namely: Electrical substations,
Windows-operated computing systems, Linux-operated server
equipment, [and] active network equipment,” The State Service of
Special Communications and Information Protection of Ukraine
(SSSCIP) said[3]
in a statement.
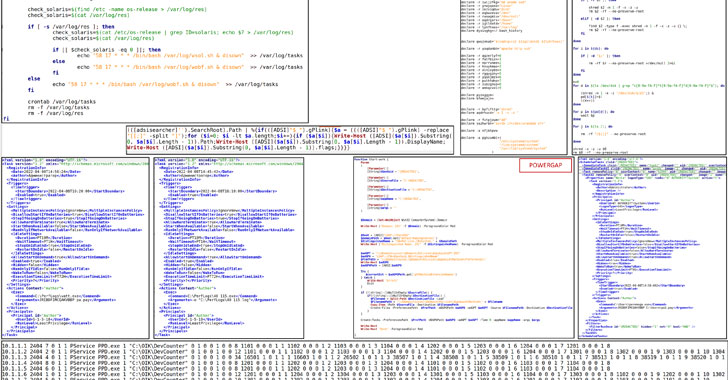
Slovak cybersecurity firm ESET, which collaborated with CERT-UA
to analyze the attack, said the attempted intrusion involved the
use of ICS-capable malware and regular disk wipers, with the
adversary unleashing an updated variant of the Industroyer[4]
malware, which was first deployed in a 2016 assault on Ukraine’s
power grid.
“The Sandworm attackers made an attempt to deploy the
Industroyer2 malware against high-voltage electrical substations in
Ukraine,” ESET explained[5]. “In addition to
Industroyer2, Sandworm used several destructive malware families
including CaddyWiper[6], OrcShred, SoloShred,
and AwfulShred.”
The victim’s power grid network is believed to have penetrated
in two waves, the initial compromise occurring no later than
February 2022, coinciding with the Russian invasion of Ukraine, and
a follow-on infiltration in April that allowed the attackers to
upload Industroyer2.
Industroyer, also known as “CrashOverride” and dubbed the
“biggest threat to industrial control systems since Stuxnet[7],” is both modular and
capable of gaining direct control of switches and circuit breakers
at an electricity distribution substation.
The new version of the sophisticated and highly customizable
malware, like its predecessor, leverages an industrial
communication protocol called IEC-104[8]
to commandeer the industrial equipment such as protection relays
that are used in electrical substations.
Forensic analysis of the artifacts left behind by Industroyer2
has revealed a compilation timestamp of March 23, 2022, indicating
that the attack had been planned for at least two weeks. That said,
it’s still unclear how the targeted power facility was initially
compromised, or how the intruders moved from the IT network to the
Industrial Control System (ICS) network.
ESET said that the destructive actions against the company’s
infrastructure were scheduled to take place on April 8, 2022, but
were ultimately foiled. This was set to be followed by the
execution of a data wiper called CaddyWiper 10 minutes later on the
same machine to erase traces of the Industroyer2 malware.
Alongside Industroyer2 and CaddyWiper, the targeted energy
provider’s network is also said to have been infected by a Linux
worm called OrcShred, which is then used to spread two different
wiper malware aimed at Linux and Solaris systems — AwfulShred and
SoloShred — and render the machines inoperable.
The findings come close on the heels of the court-authorized
takedown of Cyclops Blink[9], an advanced modular
botnet controlled by the Sandworm threat actor, last week.
CERT-UA, for its part, has also warned of a number of spear-phishing[10] campaigns[11] mounted by Armageddon,
another Russia-based group with ties to the Federal Security
Service (FSB) that has attacked Ukrainian entities since at least
2013.
“Ukraine is once again at the center of cyberattacks targeting
their critical infrastructure,” ESET said. “This new Industroyer
campaign follows multiple waves of wipers that have been targeting
various sectors in Ukraine.”
References
- ^
disclosed
(cert.gov.ua) - ^
cyberattack by Sandworm
(thehackernews.com) - ^
said
(cip.gov.ua) - ^
Industroyer
(thehackernews.com) - ^
explained
(www.welivesecurity.com) - ^
CaddyWiper
(thehackernews.com) - ^
Stuxnet
(thehackernews.com) - ^
IEC-104
(en.wikipedia.org) - ^
takedown
of Cyclops Blink (thehackernews.com) - ^
spear-phishing
(thehackernews.com) - ^
campaigns
(cert.gov.ua)
Read more https://thehackernews.com/2022/04/russian-hackers-tried-attacking.html