Cybersecurity researchers have detailed the workings of a
fully-featured malware loader dubbed PureCrypter
that’s being purchased by cyber criminals to deliver remote access
trojans (RATs) and information stealers.
“The loader is a .NET executable obfuscated with SmartAssembly
and makes use of compression, encryption, and obfuscation to evade
antivirus software products,” Zscaler’s Romain Dumont said[1]
in a new report.
Some of the malware families distributed using PureCrypter
include Agent Tesla[2], Arkei[3], AsyncRAT[4], AZORult[5], DarkCrystal RAT[6]
(DCRat), LokiBot[7], NanoCore[8], RedLine Stealer[9], Remcos[10], Snake Keylogger[11], and Warzone RAT[12].
Sold for a price of $59 by its developer named “PureCoder” for a
one-month plan (and $249 for a one-off lifetime purchase) since at
least March 2021, PureCrypter is advertised as the “only crypter in
the market that uses offline and online delivery technique.”
Crypters act as the first layer of defense[13] against reverse
engineering and are typically used to pack the malicious payload.
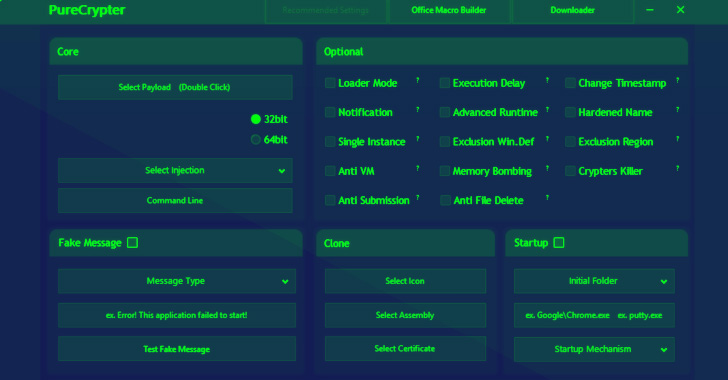
PureCrypter also features what it says is an advanced mechanism to
inject the embedded malware into native processes and a variety of
configurable options to achieve persistence on startup and turn on
additional options to fly under the radar.
Also offered is a Microsoft Office macro builder and a
downloader, highlighting the potential initial infection routes
that can be employed to propagate the malware.
Interestingly, while PureCoder makes it a point to note that the
“software was created for educational purposes only,” its terms of
service (ToS) forbids buyers from uploading the tool to malware
scanning databases such as VirusTotal, Jotti, and MetaDefender.
“You are not allowed to scan the crypted file, as the crypter
itself has a built-in scanner,” the ToS further states.
In one sample analyzed by Zscaler, a disk image file (.IMG) was
found to contain a first-stage downloader that, in turn, retrieves
and runs a second-stage module from a remote server, which
subsequently injects the final malware payload inside other
processes like MSBuild[14].
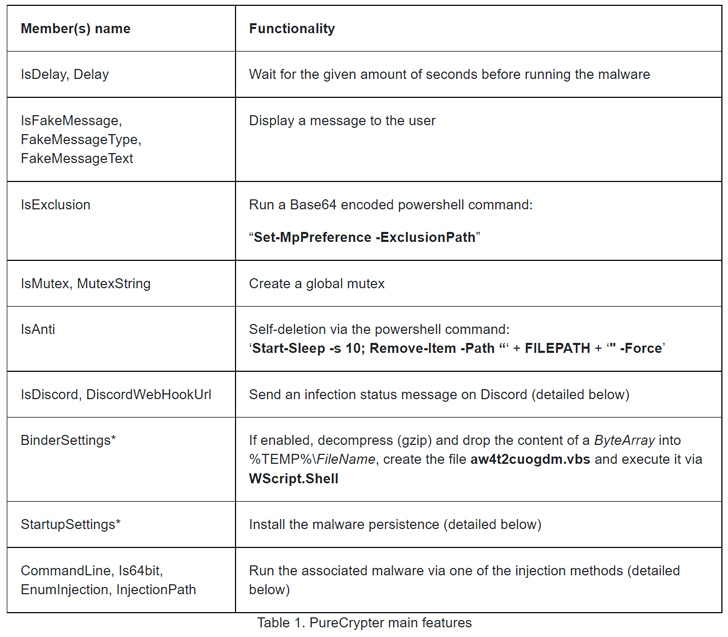
PureCryter also offers a number of notable features that allows
it to remove itself from the compromised machine and report the
infection status to the author via Discord and Telegram.
References
- ^
said
(www.zscaler.com) - ^
Agent
Tesla (malpedia.caad.fkie.fraunhofer.de) - ^
Arkei
(blogs.blackberry.com) - ^
AsyncRAT
(malpedia.caad.fkie.fraunhofer.de) - ^
AZORult
(malpedia.caad.fkie.fraunhofer.de) - ^
DarkCrystal RAT
(thehackernews.com) - ^
LokiBot
(thehackernews.com) - ^
NanoCore
(malpedia.caad.fkie.fraunhofer.de) - ^
RedLine
Stealer (thehackernews.com) - ^
Remcos
(malpedia.caad.fkie.fraunhofer.de) - ^
Snake
Keylogger (www.fortinet.com) - ^
Warzone RAT
(blogs.blackberry.com) - ^
first
layer of defense (blog.malwarebytes.com) - ^
MSBuild
(thehackernews.com)
Read more https://thehackernews.com/2022/06/researchers-detail-purecrypter-loader.html