A new covert Linux kernel rootkit named Syslogk
has been spotted under development in the wild and cloaking a
malicious payload that can be remotely commandeered by an adversary
using a magic network traffic packet[1].
“The Syslogk rootkit is heavily based on Adore-Ng but
incorporates new functionalities making the user-mode application
and the kernel rootkit hard to detect,” Avast security researchers
David Álvarez and Jan Neduchal said[2]
in a report published Monday.
Adore-Ng, an open-source rootkit[3]
available since 2004, equips the attacker with full control over a
compromised system. It also facilitates hiding processes as well as
custom malicious artifacts, files, and even the kernel module,
making it harder to detect.
“The module starts by hooking itself into various file systems.
It digs up the inode for the root filesystem, and replaces that
inode’s readdir()[4]
function pointer with one of its own,” LWN.net noted[5] at the time. “The Adore
version performs like the one it replaces, except that it hides any
files owned by a specific user and group ID.”
Besides its capabilities to hide network traffic from utilities
like netstat[6], housed within the
rootkit is a payload named “PgSD93ql” that’s nothing but a C-based
compiled backdoor trojan named Rekoobe[7]
and gets triggered upon receiving a magic packet.
“Rekoobe is a piece of code implanted in legitimate servers,”
the researchers said. “In this case it is embedded in a fake SMTP
server, which spawns a shell when it receives a specially crafted
command.”
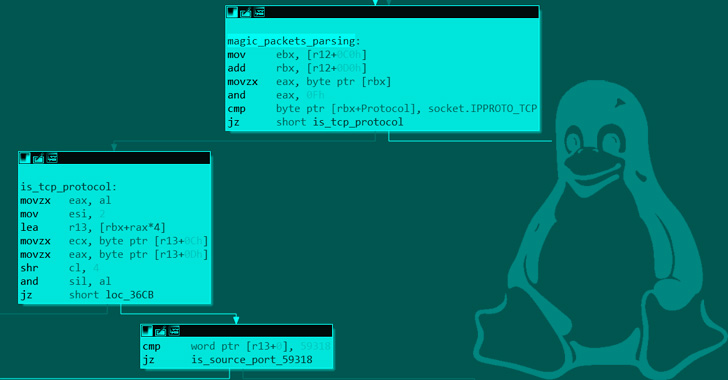
Specifically, Syslogk is engineered to inspect TCP packets
containing the source port number 59318 to launch the Rekoobe
malware. Stopping the payload, on the other hand, requires the TCP
packet to meet the following criteria –
- Reserved field of the TCP header is set to 0x08
- Source port is between 63400 and 63411 (inclusive)
- Both the destination port and the source address are the same
as that were used when sending the magic packet to start Rekoobe,
and - Contains a key (“D9sd87JMaij”) that is hardcoded in the rootkit
and located in a variable offset of the magic packet
For its part, Rekoobe masquerades as a seemingly innocuous SMTP
server but in reality is based on an open-source project called
Tiny
SHell[8] and stealthily
incorporates a backdoor command for spawning a shell that makes it
possible to execute arbitrary commands.
Syslogk adds to a growing list of newly discovered evasive Linux
malware such as BPFDoor and Symbiote[9], highlighting how cyber
criminals are increasingly targeting Linux servers and cloud
infrastructure to launch ransomware campaigns, cryptojacking
attacks, and other illicit activity.
“Rootkits are dangerous pieces of malware,” the researchers
said. “Kernel rootkits can be hard to detect and remove because
these pieces of malware run in a privileged layer.”
References
- ^
magic
network traffic packet (en.wikipedia.org) - ^
said
(decoded.avast.io) - ^
open-source rootkit
(github.com) - ^
readdir()
(man7.org) - ^
noted (lwn.net) - ^
netstat
(en.wikipedia.org) - ^
Rekoobe
(malpedia.caad.fkie.fraunhofer.de) - ^
Tiny SHell
(github.com) - ^
BPFDoor
and Symbiote (thehackernews.com)
Read more https://thehackernews.com/2022/06/new-syslogk-linux-rootkit-lets.html