A new malware tool that enables cybercriminal actors to build
malicious Windows shortcut (.LNK[1]) files has been spotted
for sale on cybercrime forums.
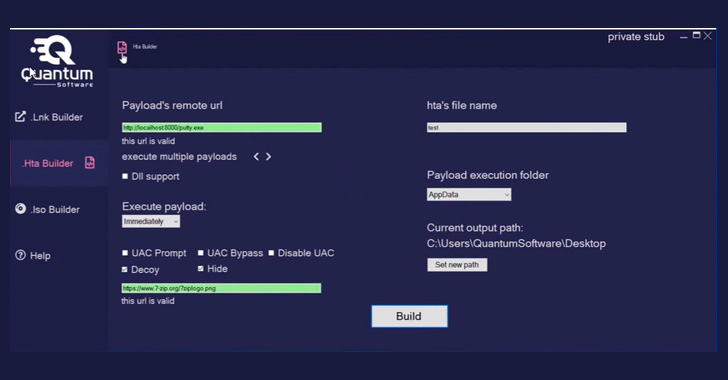
Dubbed Quantum Lnk Builder, the software makes it
possible to spoof any extension and choose from over 300 icons, not
to mention support UAC[2]
and Windows SmartScreen[3]
bypass as well as “multiple payloads per .LNK” file. Also offered
are capabilities to generate .HTA and disk image (.ISO)
payloads.
Quantum Builder is available for lease at different price
points: €189 a month, €355 for two months, €899 for six months, or
as a one-off lifetime purchase for €1,500.
“.LNK files are shortcut files that reference other files,
folders, or applications to open them,” Cyble researchers said[4]
in a report. “The [threat actor] leverages the .LNK files and drops
malicious payloads using LOLBins[5]
[living-off-the-land binaries].”
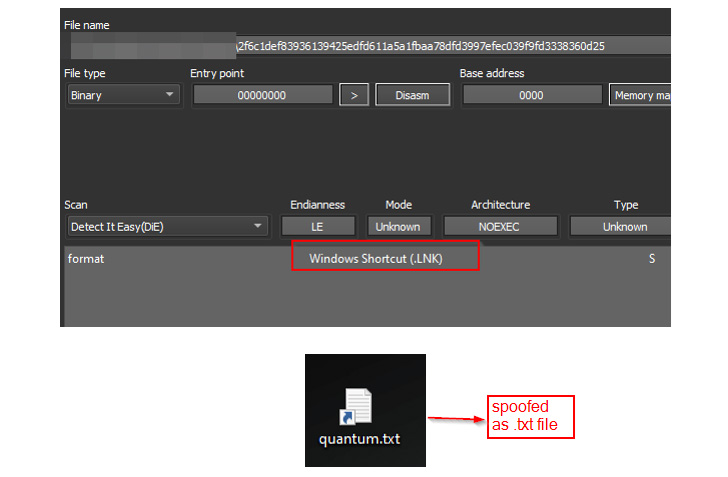
Early evidence of malware samples using Quantum Builder in the
wild is said to date back to May 24, masquerading as
harmless-looking text files (“test.txt.lnk”).
“By default, Windows hides the .LNK extension, so if a file is
named as file_name.txt.lnk, then only file_name.txt will be visible
to the user even if the show file extension option is enabled,” the
researchers said. “For such reasons, this might be an attractive
option for TAs, using the .LNK files as a disguise or
smokescreen.”
Launching the .LNK file executes PowerShell code that, in turn,
runs a HTML application (“bdg.hta”) file hosted on Quantum’s
website (“quantum-software[.]online”) using MSHTA[6], a legitimate Windows
utility that’s used to run HTA files.
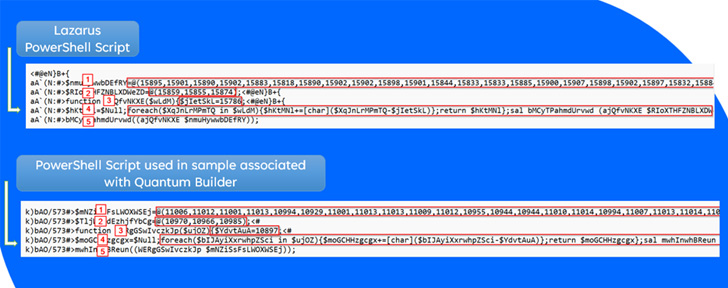
Quantum Builder is said to share ties with the North
Korean-based Lazarus Group[7]
based on source code-level overlaps in the tool and the latter’s
modus operandi of leveraging .LNK files for delivering further
stage payloads, indicating its potential use by APT actors in their
attacks.
The development comes as operators behind Bumblebee[8]
and Emotet[9]
are shifting to .LNK files as a conduit to trigger the infection
chains following Microsoft’s decision to disable[10] Visual Basic for
Applications (VBA) macros by default across its products earlier
this year.
Bumblebee, a replacement for BazarLoader malware first spotted
in March, functions as a backdoor designed to give the attackers
persistent access to compromised systems and a downloader for other
malware, including Cobalt Strike and Sliver.
The malware’s capabilities have also made it a tool of choice
for threat actors, with 413 incidents of Bumblebee infection
reported in May 2022, up from 41 in April, according to Cyble.
“Bumblebee is a new and highly sophisticated malware loader that
employs extensive evasive maneuvers and anti-analysis tricks,
including complex anti-virtualization techniques,” the researchers
said[11]. “It is likely to
become a popular tool for ransomware groups to deliver their
payload.”
References
- ^
.LNK
(docs.microsoft.com) - ^
UAC
(en.wikipedia.org) - ^
Windows
SmartScreen (docs.microsoft.com) - ^
said
(blog.cyble.com) - ^
LOLBins
(www.darktrace.com) - ^
MSHTA
(attack.mitre.org) - ^
Lazarus
Group (thehackernews.com) - ^
Bumblebee
(thehackernews.com) - ^
Emotet
(thehackernews.com) - ^
disable
(thehackernews.com) - ^
said
(blog.cyble.com)
Read more https://thehackernews.com/2022/06/new-quantum-builder-lets-attackers.html