A China-based advanced persistent threat (APT) group is possibly
deploying short-lived ransomware families as a decoy to cover up
the true operational and tactical objectives behind its
campaigns.
The activity cluster, attributed to a hacking group dubbed
Bronze Starlight by Secureworks, involves the
deployment of post-intrusion ransomware such as LockFile, Atom
Silo, Rook, Night Sky, Pandora, and LockBit 2.0.
“The ransomware could distract incident responders from
identifying the threat actors’ true intent and reduce the
likelihood of attributing the malicious activity to a
government-sponsored Chinese threat group,” the researchers
said[1]
in a new report. “In each case, the ransomware targets a small
number of victims over a relatively brief period of time before it
ceases operations, apparently permanently.”
Bronze Starlight, active since mid-2021, is also tracked by
Microsoft under the emerging threat cluster moniker DEV-0401, with
the tech giant emphasizing its involvement in all stages of the
ransomware attack cycle right from initial access to the payload
deployment.
Unlike other RaaS groups that purchase access from initial
access brokers (IABs[2]) to enter a network,
attacks mounted by the actor are characterized by the use of
unpatched vulnerabilities affecting Exchange Server, Zoho
ManageEngine ADSelfService Plus, Atlassian Confluence (including
the newly disclosed flaw[3]), and Apache Log4j.
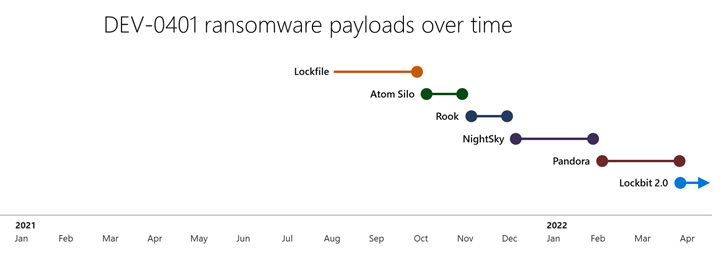
Since August 2021, the group is said to have cycled through as
many as six different ransomware strains such as LockFile (August),
Atom Silo (October), Rook (November), Night Sky (December), Pandora
(February 2022), and most recently LockBit 2.0 (April).
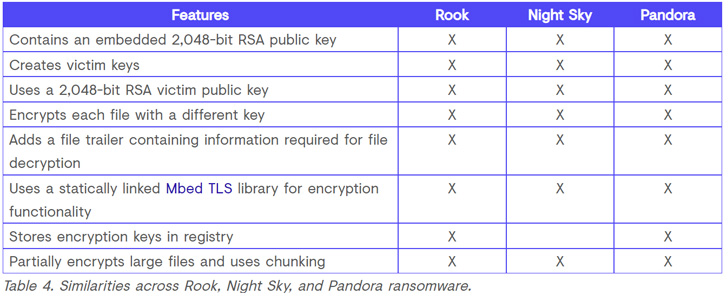
What’s more, similarities have been uncovered between LockFile
and Atom Silo as well as between Rook, Night Sky, and Pandora — the
latter three derived from Babuk ransomware, whose source code leaked[4]
in September 2021 — indicating the work of a common actor.
“Because DEV-0401 maintains and frequently rebrands their own
ransomware payloads, they can appear as different groups in
payload-driven reporting and evade detections and actions against
them,” Microsoft noted[5]
last month.
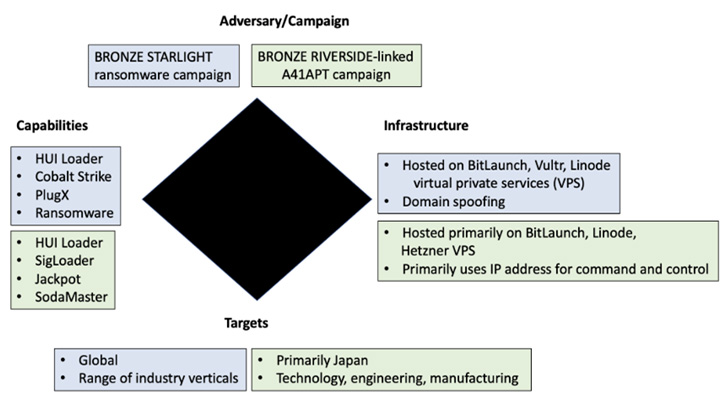
Upon gaining a foothold inside a network, Bronze Starlight is
known to rely on techniques like using Cobalt Strike and Windows
Management Instrumentation (WMI[6]) for lateral movement,
although starting this month, the group has begun replacing Cobalt
Strike with the Sliver framework in their attacks.
Other observed tradecraft relates to the use of HUI Loader[7]
to launch next-stage encrypted payloads such as PlugX[8]
and Cobalt Strike Beacons, the latter of which is employed to
deliver the ransomware, but not before obtaining privileged Domain
Administrator credentials.
“The use of HUI Loader to load Cobalt Strike Beacon, the Cobalt
Strike Beacon configuration information, the C2 infrastructure, and
the code overlap suggest that the same threat group is associated
with these five ransomware families,” the researchers
explained.
It’s worth pointing out that both HUI Loader and PlugX,
alongside ShadowPad[9], are malware
historically put to use by Chinese nation-state adversarial
collectives, lending credence to the possibility that Bronze
Starlight is more geared towards espionage than immediate monetary
benefits.
On top of that, the victimology pattern spanning across the
different ransomware strains shows that a majority of the targets
are likely to be of more interest to Chinese government-sponsored
groups focused on long-term intelligence gathering.
The key victims encompass pharmaceutical companies in Brazil and
the U.S., a U.S.-based media organization with offices in China and
Hong Kong, electronic component designers and manufacturers in
Lithuania and Japan, a law firm in the U.S., and an aerospace and
defense division of an Indian conglomerate.
To that end, the ransomware operations, besides providing a
means to exfiltrate data as part of the double extortion
“name-and-shame” scheme, also offer twin advantages in that it
allows the threat actor to destroy forensic evidence of their
malicious activities and act as a distraction from data theft.
“It is plausible that Bronze Starlight deploys ransomware as a
smokescreen rather than for financial gain, with the underlying
motivation of stealing intellectual property or conducting
espionage,” the researchers said.
References
- ^
said
(www.secureworks.com) - ^
IABs
(thehackernews.com) - ^
newly
disclosed flaw (thehackernews.com) - ^
source
code leaked (thehackernews.com) - ^
noted
(www.microsoft.com) - ^
WMI
(en.wikipedia.org) - ^
HUI
Loader (malpedia.caad.fkie.fraunhofer.de) - ^
PlugX
(thehackernews.com) - ^
ShadowPad
(thehackernews.com)
Read more https://thehackernews.com/2022/06/state-backed-hackers-using-ransomware.html