Consumer electronics maker Lenovo on Tuesday rolled out fixes[1]
to contain three security flaws in its UEFI firmware affecting over
70 product models.
“The vulnerabilities can be exploited to achieve arbitrary code
execution in the early phases of the platform boot, possibly
allowing the attackers to hijack the OS execution flow and disable
some important security features,” Slovak cybersecurity firm ESET
said[2]
in a series of tweets.
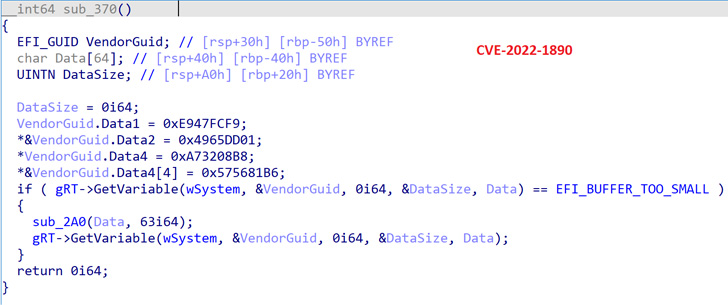
Tracked as CVE-2022-1890, CVE-2022-1891, and CVE-2022-1892, all
three bugs relate to buffer overflow vulnerabilities[3] that have been described
by Lenovo as leading to privilege escalation on affected systems.
Martin Smolár from ESET has been credited with reporting the
flaws.
The bugs stem from an insufficient validation of an NVRAM
variable called “DataSize” in three different drivers ReadyBootDxe,
SystemLoadDefaultDxe, and SystemBootManagerDxe, leading to a buffer
overflow that could be weaponized to achieve code execution.
This is the second time Lenovo has moved to address UEFI
security vulnerabilities since the start of the year. In April, the
company resolved three flaws[4]
(CVE-2021-3970, CVE-2021-3971, and CVE-2021-3972) — also discovered
by Smolár — that could have been abused to deploy and execute
firmware implants.
Users of impacted devices are highly recommended to update their
firmware to the latest version to mitigate potential threats.
References
- ^
rolled
out fixes (thehackernews.com) - ^
said
(twitter.com) - ^
buffer
overflow vulnerabilities
(support.lenovo.com) - ^
three
flaws (thehackernews.com)
Read more https://thehackernews.com/2022/07/new-uefi-firmware-vulnerabilities.html